Autonomous Threat Sweeper
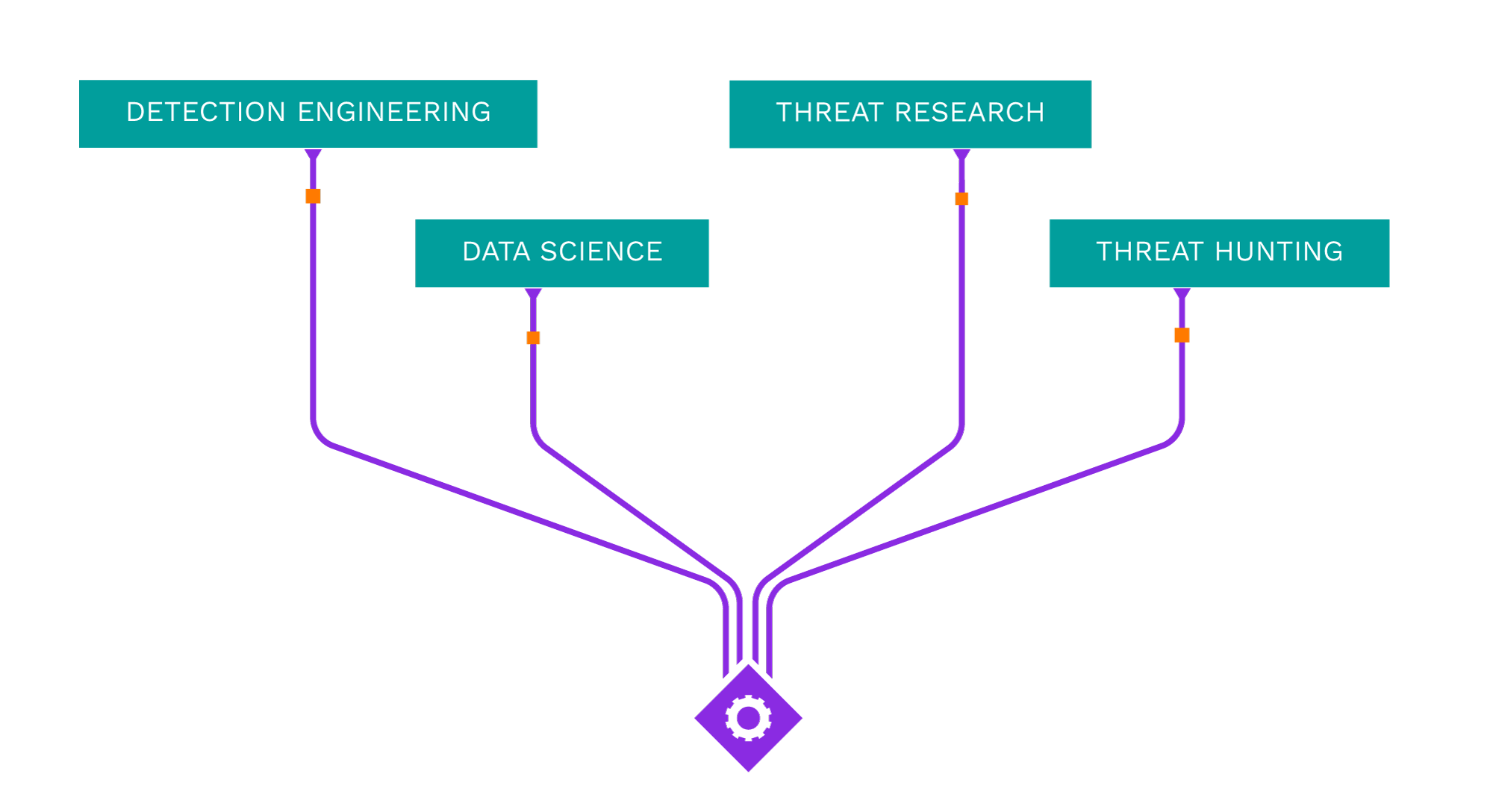
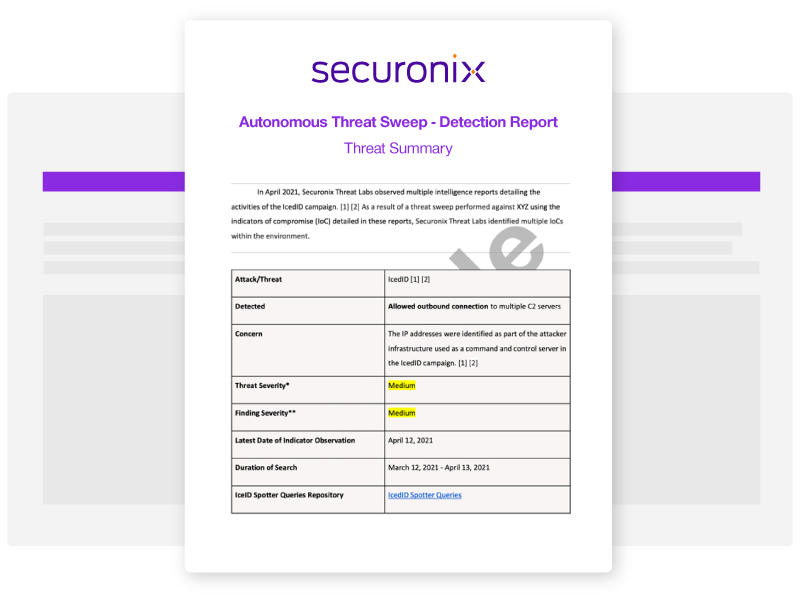
Acting as your own dedicated Cyber Rapid Response Team, Securonix Autonomous Threat Sweeper (ATS) automatically and retroactively hunts for new and emerging threats based on the latest threat intelligence from our Threat Labs Team.
Latest ATS Entries
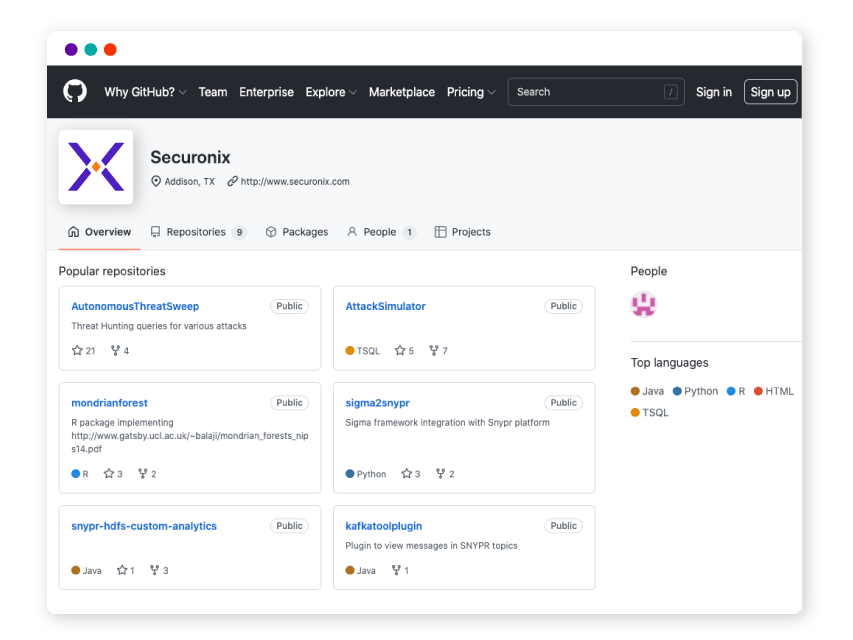
All indicators of compromise (IOC) and Spotter queries are available on our GitHub repository.
—
- Intel Source:
- Thehackernews
- Intel Name:
- Malvertising_Campaign_Leveraging_Google_Ads_Distributes_MadMxShell_Backdoor
- Date of Scan:
- 2024-04-18
- Impact:
- MEDIUM
- Summary:
- Zscaler ThreatLabz researchers have uncovered a sophisticated malvertising campaign utilizing Google Ads to distribute a previously unknown backdoor named MadMxShell. The campaign involves the registration of multiple domains resembling legitimate IP scanner software, which are then promoted through Google Ads to target specific search keywords. Victims who visit these sites are tricked into downloading a malicious file disguised as IP scanner software. Once executed, the malware employs DLL side-loading and process hollowing techniques to infect systems, ultimately establishing a backdoor for gathering system information and performing malicious activities.
Source:
https://thehackernews.com/2024/04/malicious-google-ads-pushing-fake-ip.html
—
- Intel Source:
- Trend Micro
- Intel Name:
- UK_Law_Enforcement_Successfully_Takes_Down_Phishing_as_a_Service_Provider_LabHost
- Date of Scan:
- 2024-04-18
- Impact:
- MEDIUM
- Summary:
- UK’s Metropolitan Police Service, in collaboration with international law enforcement agencies and private industry partners, executed an operation leading to the takedown of the notorious Phishing-as-a-Service (PhaaS) provider LabHost. LabHost, also known as LabRat, had gained notoriety since its emergence in late 2021 for offering a platform facilitating phishing attacks against numerous banks and organizations worldwide. With over 2,000 criminal users and more than 40,000 fraudulent sites deployed, LabHost posed a significant threat to global cybersecurity.
Source:
https://www.trendmicro.com/en_us/research/24/d/labhost-takedown.html
—
- Intel Source:
- Netscope
- Intel Name:
- Evil_Ant_Ransomware
- Date of Scan:
- 2024-04-17
- Impact:
- LOW
- Summary:
- Netscope researchers shared the analysis of a new ransomware strain called Evil Ant. It targets personal folders and external drives for encryption and requires administrator privileges to function properly. It also disables Windows Defender and Task Manager, collects the victim’s IP address, and uses Fernet symmetric cryptography to encrypt files.
Source:
https://www.netskope.com/jp/blog/netskope-threat-coverage-evil-ant-ransomware
—
- Intel Source:
- Cado Security
- Intel Name:
- Critical_Atlassian_Flaw_Exploited_to_Deploy_Linux_Variant_of_Cerber_Ransomware
- Date of Scan:
- 2024-04-17
- Impact:
- MEDIUM
- Summary:
- Researchers at Cado Security have noticed that threat actors are using unpatched Atlassian servers as a means of distributing the Linux version of the Cerber ransomware, also known as C3RB3R. The attacks take use of a significant security flaw in the Atlassian Confluence Data Center and Server known as CVE-2023-22518 (CVSS score: 9.1), which enables an unauthorized attacker to reset Confluence and create an administrator account.
Source:
https://www.cadosecurity.com/blog/cerber-ransomware-dissecting-the-three-heads
—
- Intel Source:
- Fortinet
- Intel Name:
- Botnets_Continue_Exploiting_CVE_2023_1389
- Date of Scan:
- 2024-04-17
- Impact:
- MEDIUM
- Summary:
- Fortinet researchers in their article explored patterns of the infection traffic and insights into the botnet that was exploited last year and believed to be exploited widely this month by a command injection vulnerability, CVE-2023-1389 was disclosed and a fix developed for the web management interface of the TP-Link Archer AX21 (AX1800). Recently, research has observed multiple attacks focusing on this year-old vulnerability, spotting botnets like Moobot, Miori, the Golang-based agent “AGoent,” and the Gafgyt Variant.
—
- Intel Source:
- Cisco Talos
- Intel Name:
- Attacks_Using_Brute_Force_to_Attack_VPN_and_SSH_Services
- Date of Scan:
- 2024-04-17
- Impact:
- MEDIUM
- Summary:
- Researchers at Cisco Talos have recently alerted about a global increase in brute-force attacks that, as of at least March 18, 2024, are targeting a variety of devices, including web application authentication interfaces, virtual private network (VPN) services, and SSH services. All of these attacks seem to be coming from anonymizing tunnels and proxies, as well as TOR exit nodes.
—
- Intel Source:
- CERT-UA
- Intel Name:
- Cyber_Threats_Targeting_Ukraine_Defense_Forces
- Date of Scan:
- 2024-04-17
- Impact:
- MEDIUM
- Summary:
- Researchers at CERT-UA are actively engaged to protect against online dangers. They noticed that in 2024, a group called UAC-0184 became more active. This group tries to steal documents and chat messages from computers used by Ukraine’s Defense Forces. They often send harmful software through popular chat apps, tricking people with fake messages about legal issues or war videos.
—
- Intel Source:
- Blackberry
- Intel Name:
- Threat_actors_FIN7_attack_the_US_Automotive
- Date of Scan:
- 2024-04-17
- Impact:
- MEDIUM
- Summary:
- Blackberry’s analysts shared the examined details about the threat of phishing attacks on businesses and provided recommendations for protecting against them. It includes a case study of a recent attack by the threat group FIN7 on a U.S. automotive company. The article suggests implementing various security measures, such as employee training, multi-factor authentication, and incident response plans, to prevent and mitigate the impact of phishing attacks. It also provides a detailed analysis of the tactics and techniques used by FIN7 in their attack, as well as a list of indicators of compromise.
Source:
https://blogs.blackberry.com/en/2024/04/fin7-targets-the-united-states-automotive-industry
—
- Intel Source:
- Forescout
- Intel Name:
- A_Recent_Wild_Exploit_Campaign_Targets_Media_Company
- Date of Scan:
- 2024-04-17
- Impact:
- LOW
- Summary:
- Forescout researchers have discovered that Vedere Labs describes an exploitation effort that targets businesses using FortiClient EMS from Fortinet, which is vulnerable to CVE-2023-48788.
Source:
https://www.forescout.com/blog/connectfun-new-exploit-campaign-in-the-wild-targets-media-company/
—
- Intel Source:
- ISC.SANS
- Intel Name:
- The_Peril_of_Malicious_Annotations
- Date of Scan:
- 2024-04-17
- Impact:
- LOW
- Summary:
- ISC.SANS researchers provided PDF files, long considered “read-only” and benign, remain a potent vector for malware delivery. Despite improvements in PDF viewer security, malicious actors exploit features like annotations and clickable links to deceive users into downloading malware. This analysis delves into the intricacies of PDF file structure, demonstrating how attackers embed clickable zones using “/Annot” keywords to link to external URLs. The provided YARA rule offers a means to detect such malicious PDF documents

Shared Security Content on Sigma
Securonix Threat Labs publishes up-to-date IOCs and threat hunting queries on Sigma, allowing you to tap into a vast community of collective defense and stay ahead of emerging threat research.
What's New from Threat Labs
-
BlogSecuronix Threat Research Knowledge Sharing Series: Detecting DLL Sideloading Techniques Found In Recent Real-world Malware Attack ChainsLearn More
-
BlogSecuronix Threat Research Security Advisory: Analysis of New DEEP#GOSU Attack Campaign Likely Associated with North Korean Kimsuky Targeting Victims with Stealthy MalwareLearn More
-
BlogSecuronix Threat Research Security Advisory: Analysis and Detection of STEADY#URSA Attack Campaign Targeting Ukraine Military Dropping New Covert SUBTLE-PAWS PowerShell BackdoorLearn More