Autonomous Threat Sweeper
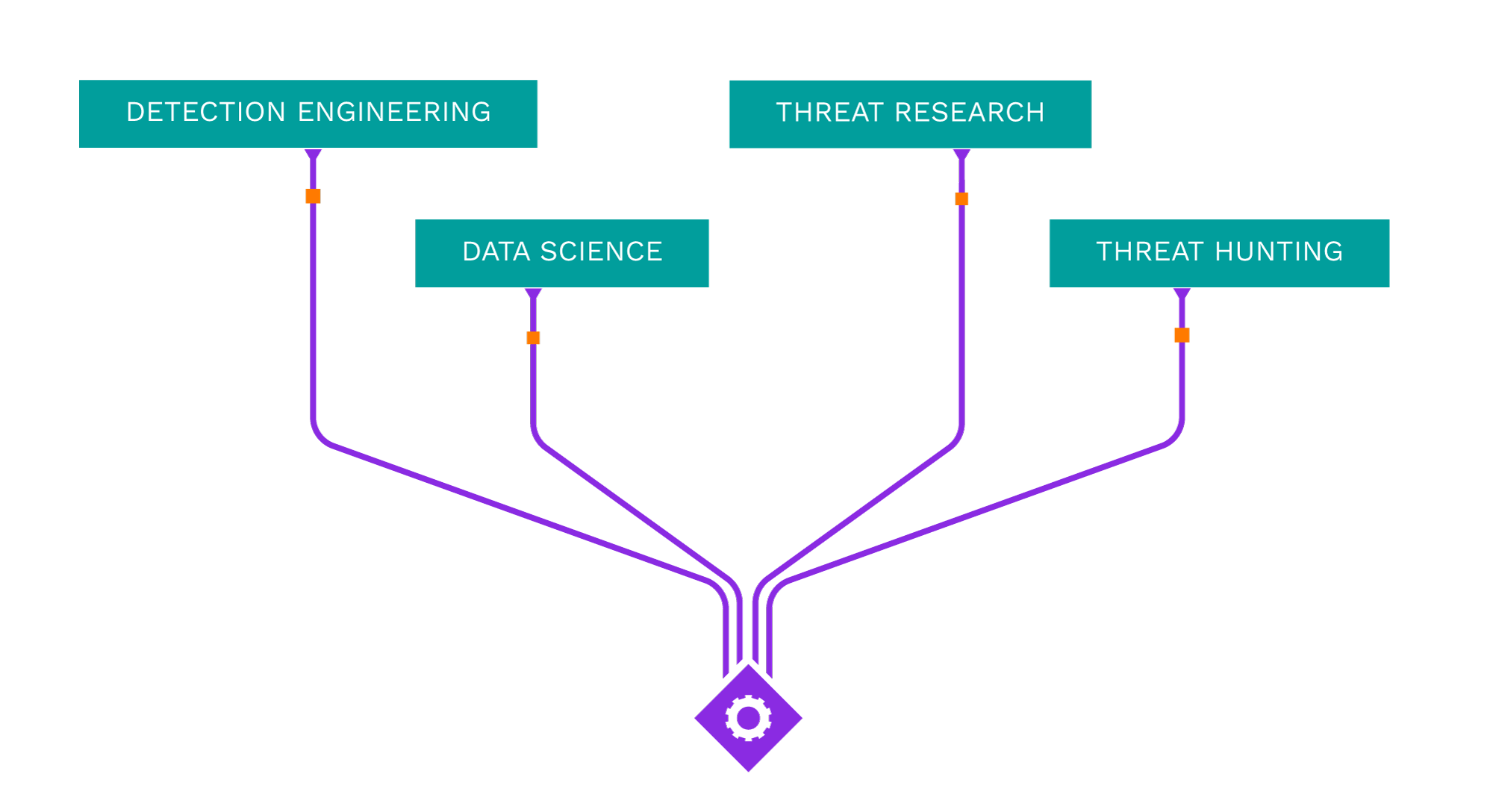
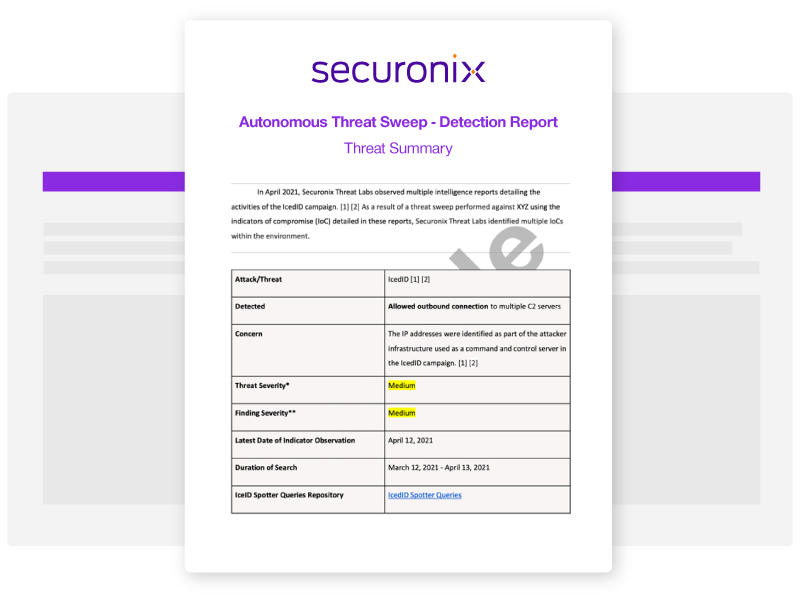
Acting as your own dedicated Cyber Rapid Response Team, Securonix Autonomous Threat Sweeper (ATS) automatically and retroactively hunts for new and emerging threats based on the latest threat intelligence from our Threat Labs Team.
Latest ATS Entries
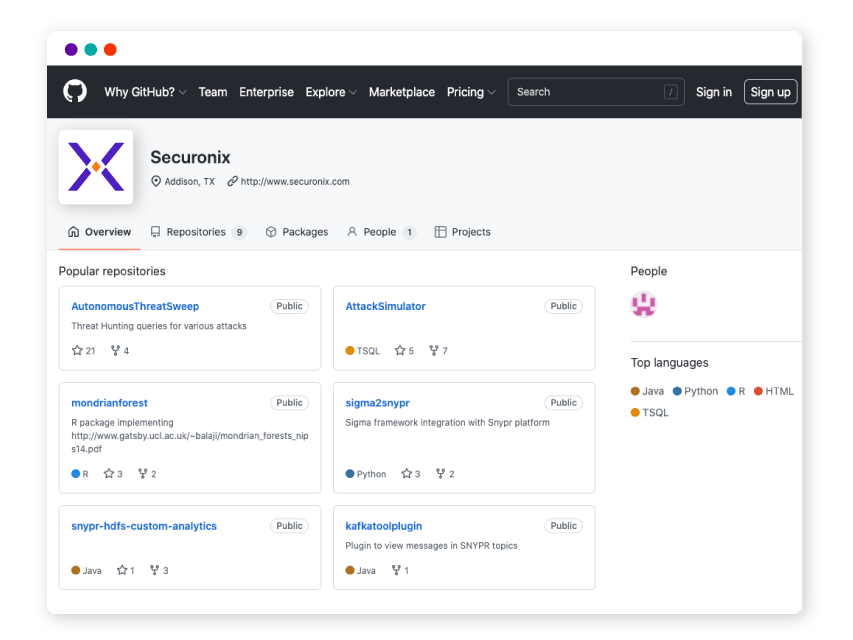
All indicators of compromise (IOC) and Spotter queries are available on our GitHub repository.
—
- Intel Source:
- Malware News
- Intel Name:
- Forest_Blizzards_GooseEgg_strategic_threat
- Date of Scan:
- 2024-04-23
- Impact:
- LOW
- Summary:
- Microsoft Threat Intelligence reveals the clandestine operations of Forest Blizzard, a threat actor group affiliated with the Russian GRU, utilizing the GooseEgg tool to exploit vulnerabilities in the Windows Print Spooler service. Forest Blizzard’s strategic targets include government, energy, transportation, and NGO sectors across the US, Europe, and the Middle East.
—
- Intel Source:
- Avast
- Intel Name:
- Spearheading_the_Opposition_to_GuptiMiner
- Date of Scan:
- 2024-04-23
- Impact:
- MEDIUM
- Summary:
- Avast Labs researchers have recently uncovered “GuptiMiner,” a very sophisticated malware operation that targets corporate networks in specifically. They discovered that GuptiMiner secretly penetrated business networks to release its harmful payloads by taking advantage of a flaw in the eScan antivirus update procedure. Their team worked closely with India CERT and eScan to fix this issue, protecting a great number of users from possible harm.
—
- Intel Source:
- Microsoft
- Intel Name:
- Threat_actor_Forest_Blizzard_recent_activity
- Date of Scan:
- 2024-04-22
- Impact:
- MEDIUM
- Summary:
- After Microsoft Threat Intelligence’s investigation of activity by the Russian-based threat actor Forest Blizzard (STRONTIUM) who used a custom tool to elevate privileges and steal credentials in compromised networks. Microsoft has spotted this threat actor abusing GooseEgg as part of post-compromise activities against targets including Ukrainian, Western European, and North American government, non-governmental, education, and transportation sector organizations.
—
- Intel Source:
- Threatdown
- Intel Name:
- FakeBat_campaign_targeting_VMware_users
- Date of Scan:
- 2024-04-22
- Impact:
- LOW
- Summary:
- Threat down researchers spotted a threat actor who’s responsible for multiple malvertising campaigns mimicking popular software downloads. It connected this threat actor with the distribution of stealers, often indirectly using known loaders such as FakeBat for Windows while using Atomic Stealer for Mac. In their latest distribution wave, the threat actor is buying ads on Google search to target VMware users.
Source:
https://www.threatdown.com/blog/fakebat-campaign-continues-now-also-targeting-vmware-users/
—
- Intel Source:
- Securonix Threat Lab
- Intel Name:
- Detecting_DLL_Sideloading_Techniques
- Date of Scan:
- 2024-04-22
- Impact:
- MEDIUM
- Summary:
- In this article, Securonix Threat Lab took a deeper dive into a prevalent “DLL sideloading” attack technique we’ve been observing in real-world attacks, including many of those we discovered, to understand its variations, how it works, and how we can detect it.
Source:
https://www.securonix.com/blog/detecting-dll-sideloading-techniques-in-malware-attack-chains/
—
- Intel Source:
- Securelist
- Intel Name:
- The_APT_group_ToddyCat_compromise_infrustructure
- Date of Scan:
- 2024-04-22
- Impact:
- LOW
- Summary:
- This month, Securelist researchers ran an investigation on how attackers got constant access to compromised infrastructure, what information on the hosts they are interested in, and what tools they used for it. ToddyCat is a threat actors group that in general targets governmental organizations located in the Asia-Pacific region. The group’s main goal is to steal sensitive information from hosts.
Source:
https://securelist.com/toddycat-traffic-tunneling-data-extraction-tools/112443/
—
- Intel Source:
- ISC.SANS
- Intel Name:
- A_Malicious_PDF_File_Using_to_Deliver_Malware
- Date of Scan:
- 2024-04-22
- Impact:
- LOW
- Summary:
- Researchers at SANS have noted that billions of PDF files are shared on a regular basis, and that many individuals take these files for trust because they believe they are “read-only” and contain just “a bunch of data”. Previously, PDF viewers were vulnerable to nasty vulnerabilities in poorly crafted PDF files. Particularly the Acrobat or FoxIt readers, they were all impacted at least once. Additionally, a PDF file can be rather “dynamic” by containing embedded JavaScript scripts, auto-open actions that cause scripts (like PowerShell on Windows) to run, or any other kind of embedded data.
Source:
https://isc.sans.edu/diary/Malicious+PDF+File+Used+As+Delivery+Mechanism/30848/
—
- Intel Source:
- CERT-UA
- Intel Name:
- Sandworm_Groups_Cyber_Scheme
- Date of Scan:
- 2024-04-22
- Impact:
- LOW
- Summary:
- Researchers at CERT-UA found that the Sandworm group had a plan to mess with almost 20 important places in March 2024. They wanted to mess up the computer systems that control energy, water, and heat in different parts of Ukraine. CERT-UA also found out that three supply chains were messed with, either because of weak software or because employees from the supplier could get into the systems.
—
- Intel Source:
- Gdatasoftware
- Intel Name:
- The_new_malware_family_Sharp_Stealer
- Date of Scan:
- 2024-04-22
- Impact:
- LOW
- Summary:
- Threat researcher Yogesh Londhe discovered a new sample that is called “Sharpil RAT.exe”. That non-obfuscated .NET application with simple stealer functionality led to another sample and the new malware family „Sharp Stealer“. The „Sharpil RAT.exe“ is written in C#, it is running in the background and immediately attempts to establish a connection with a Telegram bot.
Source:
https://www.gdatasoftware.com/blog/2024/04/37894-sharp-info-stealer
—
- Intel Source:
- ASEC
- Intel Name:
- Surge_in_Phishing_Attacks_Impersonating_Korean_Websites
- Date of Scan:
- 2024-04-22
- Impact:
- MEDIUM
- Summary:
- AhnLab’s Security Intelligence Center (ASEC) has identified a significant rise in phishing attempts mimicking Korean portal websites, logistics brands, and webmail login pages. These attacks utilize sophisticated tactics, such as replicating the appearance of legitimate websites and leveraging NoCodeForm for credential exfiltration.

Shared Security Content on Sigma
Securonix Threat Labs publishes up-to-date IOCs and threat hunting queries on Sigma, allowing you to tap into a vast community of collective defense and stay ahead of emerging threat research.
What's New from Threat Labs
-
BlogSecuronix Threat Research Knowledge Sharing Series: Detecting DLL Sideloading Techniques Found In Recent Real-world Malware Attack ChainsLearn More
-
BlogSecuronix Threat Research Security Advisory: Analysis of New DEEP#GOSU Attack Campaign Likely Associated with North Korean Kimsuky Targeting Victims with Stealthy MalwareLearn More
-
BlogSecuronix Threat Research Security Advisory: Analysis and Detection of STEADY#URSA Attack Campaign Targeting Ukraine Military Dropping New Covert SUBTLE-PAWS PowerShell BackdoorLearn More