Autonomous Threat Sweeper
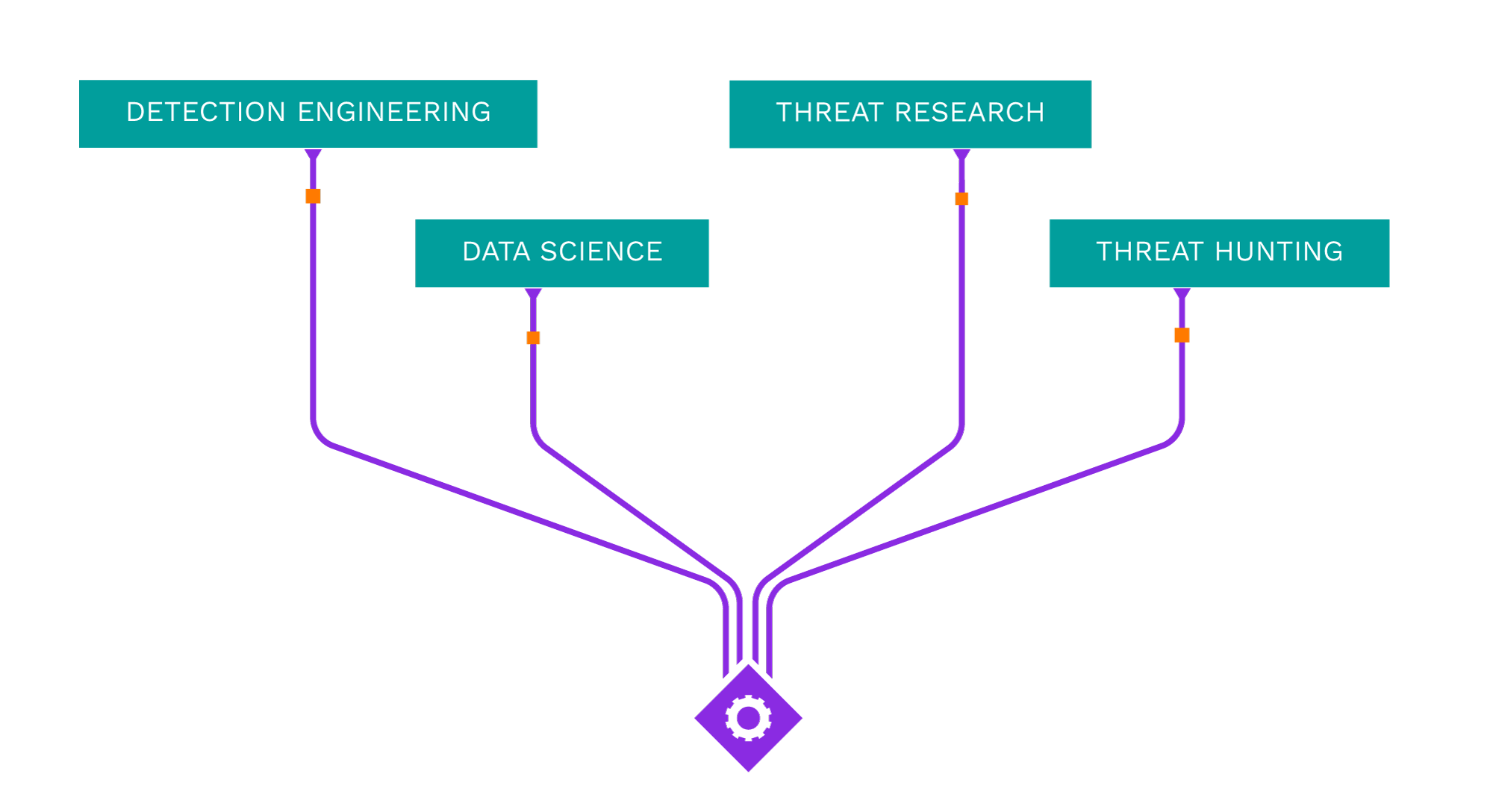
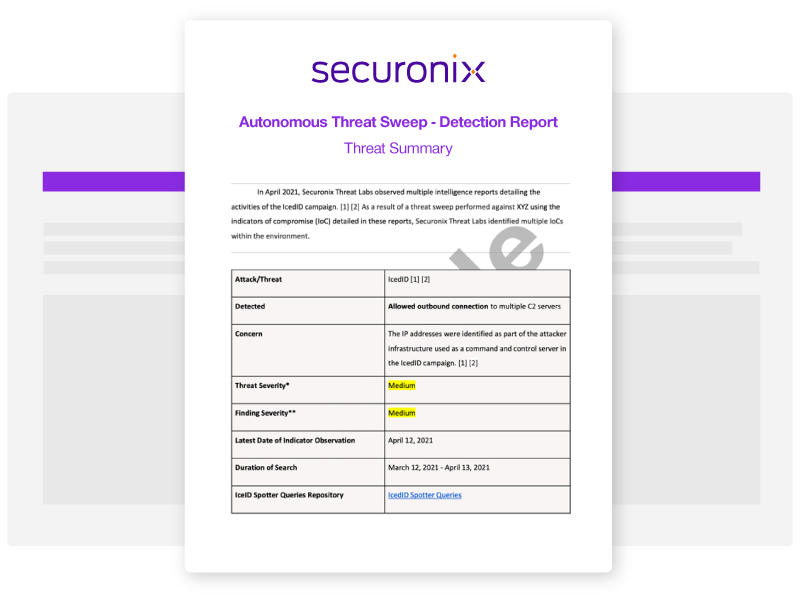
Acting as your own dedicated Cyber Rapid Response Team, Securonix Autonomous Threat Sweeper (ATS) automatically and retroactively hunts for new and emerging threats based on the latest threat intelligence from our Threat Labs Team.
Latest ATS Entries
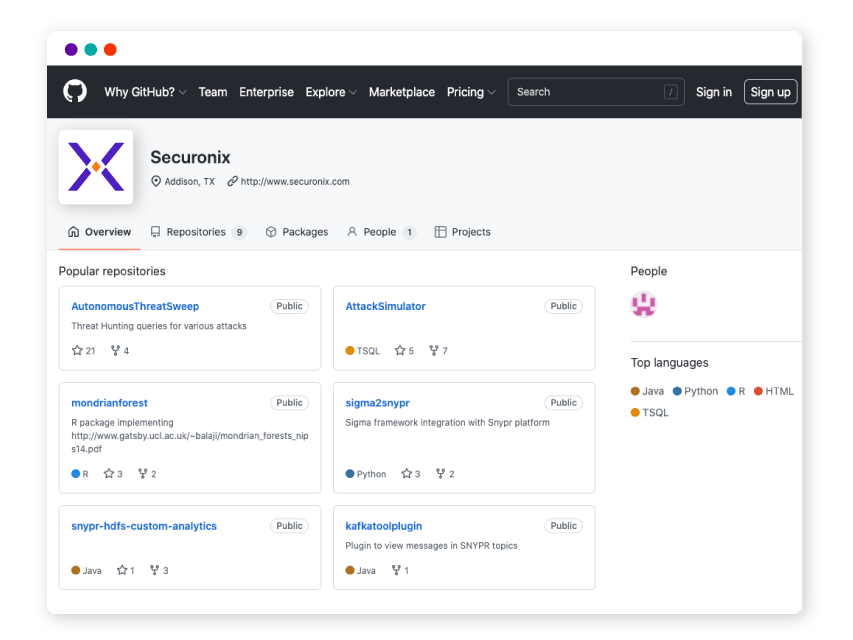
All indicators of compromise (IOC) and Spotter queries are available on our GitHub repository.
—
- Intel Source:
- Seqrite Labs
- Intel Name:
- Attacks_on_Indian_Government_Are_Increasing_by_Pakistani_APTs
- Date of Scan:
- 2024-04-24
- Impact:
- MEDIUM
- Summary:
- Researchers at Seqrite Labs have uncovered several cyberattack operations in which they have detected the use of different remote access tools (RATs), such as AllaKore RAT and Crimson RAT. They explore the mechanics of these attacks, the actions of the attackers, and the features of the malicious software that is employed. The report also discusses the increase of cyberattacks by Pakistan-affiliated Advanced Persistent Threat (APT) groups, namely SideCopy and APT36 (Transparent Tribe), against Indian government institutions.
—
- Intel Source:
- Talos
- Intel Name:
- CoralRaider_threat_actor_continues_to_expand_its_activity
- Date of Scan:
- 2024-04-23
- Impact:
- MEDIUM
- Summary:
- Back in February Cisco Talos observed a new ongoing campaign which was operated by a threat actor who distributed three famous infostealer malware, including Cryptbot, LummaC2, and Rhadamanthys. This time researchers discovered a new PowerShell command-line argument embedded in the LNK file to bypass anti-virus products and download the final payload into the victims’ host.
—
- Intel Source:
- Cert.at
- Intel Name:
- Double_Agents_of_Malicious_Python_Packages
- Date of Scan:
- 2024-04-23
- Impact:
- LOW
- Summary:
- Researcher Kamil Mankowski continued his journey tracking malicious Python packages used by Oak-Grabber-V2 and provided his analysis on it.
—
- Intel Source:
- Malware News
- Intel Name:
- Forest_Blizzards_GooseEgg_strategic_threat
- Date of Scan:
- 2024-04-23
- Impact:
- LOW
- Summary:
- Microsoft Threat Intelligence reveals the clandestine operations of Forest Blizzard, a threat actor group affiliated with the Russian GRU, utilizing the GooseEgg tool to exploit vulnerabilities in the Windows Print Spooler service. Forest Blizzard’s strategic targets include government, energy, transportation, and NGO sectors across the US, Europe, and the Middle East.
—
- Intel Source:
- Harfanglab
- Intel Name:
- Muddywater_campaign_continues_abusing_Atera_Agents
- Date of Scan:
- 2024-04-23
- Impact:
- MEDIUM
- Summary:
- Harfanglab’s report details an ongoing campaign by the Iranian state-sponsored threat actor MuddyWater that has been actively exploiting the legitimate remote monitoring and management (RMM) tool Atera Agent since late 2023. The group has been relying on Atera’s free trial offers to generate agents registered with compromised email accounts, enabling them to establish remote access to targeted systems without setting up their own infrastructure. The campaign has targeted various sectors across multiple countries through spearphishing emails distributing the malicious Atera Agent installers.
Source:
https://harfanglab.io/en/insidethelab/muddywater-rmm-campaign/
—
- Intel Source:
- Avast
- Intel Name:
- Spearheading_the_Opposition_to_GuptiMiner
- Date of Scan:
- 2024-04-23
- Impact:
- MEDIUM
- Summary:
- Avast Labs researchers have recently uncovered “GuptiMiner,” a very sophisticated malware operation that targets corporate networks in specifically. They discovered that GuptiMiner secretly penetrated business networks to release its harmful payloads by taking advantage of a flaw in the eScan antivirus update procedure. Their team worked closely with India CERT and eScan to fix this issue, protecting a great number of users from possible harm.
—
- Intel Source:
- ASEC
- Intel Name:
- Surge_in_Phishing_Attacks_Impersonating_Korean_Websites
- Date of Scan:
- 2024-04-22
- Impact:
- MEDIUM
- Summary:
- AhnLab’s Security Intelligence Center (ASEC) has identified a significant rise in phishing attempts mimicking Korean portal websites, logistics brands, and webmail login pages. These attacks utilize sophisticated tactics, such as replicating the appearance of legitimate websites and leveraging NoCodeForm for credential exfiltration.
—
- Intel Source:
- ISC.SANS
- Intel Name:
- A_Malicious_PDF_File_Using_to_Deliver_Malware
- Date of Scan:
- 2024-04-22
- Impact:
- LOW
- Summary:
- Researchers at SANS have noted that billions of PDF files are shared on a regular basis, and that many individuals take these files for trust because they believe they are “read-only” and contain just “a bunch of data”. Previously, PDF viewers were vulnerable to nasty vulnerabilities in poorly crafted PDF files. Particularly the Acrobat or FoxIt readers, they were all impacted at least once. Additionally, a PDF file can be rather “dynamic” by containing embedded JavaScript scripts, auto-open actions that cause scripts (like PowerShell on Windows) to run, or any other kind of embedded data.
Source:
https://isc.sans.edu/diary/Malicious+PDF+File+Used+As+Delivery+Mechanism/30848/
—
- Intel Source:
- Ethical-Empire
- Intel Name:
- Phishing_attacks_mimicking_Korean_portal_login_pages
- Date of Scan:
- 2024-04-22
- Impact:
- LOW
- Summary:
- Researchers from Ethical-Empire spotted phishing attacks coping Korean portal login pages, where fake login screens closely resembled legitimate sites, making them difficult to distinguish at first look by targeting different Korean portals, logistics brands, and webmail services.
Source:
https://ethical-empire.com/korean-portal-phishing-scam/
—
- Intel Source:
- Securelist
- Intel Name:
- The_APT_group_ToddyCat_compromise_infrustructure
- Date of Scan:
- 2024-04-22
- Impact:
- LOW
- Summary:
- This month, Securelist researchers ran an investigation on how attackers got constant access to compromised infrastructure, what information on the hosts they are interested in, and what tools they used for it. ToddyCat is a threat actors group that in general targets governmental organizations located in the Asia-Pacific region. The group’s main goal is to steal sensitive information from hosts.
Source:
https://securelist.com/toddycat-traffic-tunneling-data-extraction-tools/112443/

Shared Security Content on Sigma
Securonix Threat Labs publishes up-to-date IOCs and threat hunting queries on Sigma, allowing you to tap into a vast community of collective defense and stay ahead of emerging threat research.
What's New from Threat Labs
-
BlogSecuronix Threat Research Security Advisory: Analysis of Ongoing FROZEN#SHADOW Attack Campaign Leveraging SSLoad Malware and RMM Software for Domain TakeoverLearn More
-
BlogSecuronix Threat Research Knowledge Sharing Series: Detecting DLL Sideloading Techniques Found In Recent Real-world Malware Attack ChainsLearn More
-
BlogSecuronix Threat Research Security Advisory: Analysis of New DEEP#GOSU Attack Campaign Likely Associated with North Korean Kimsuky Targeting Victims with Stealthy MalwareLearn More