Autonomous Threat Sweeper
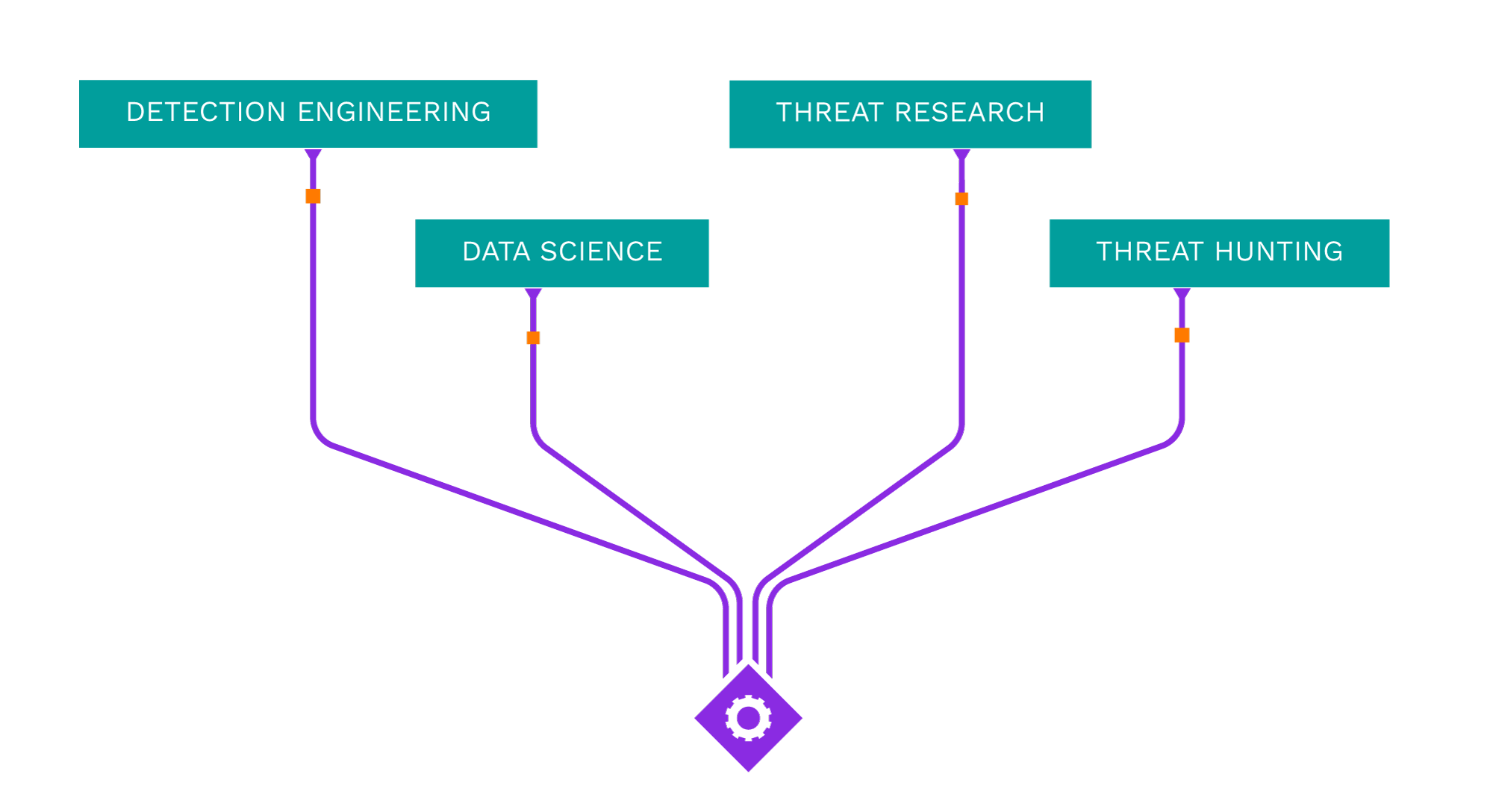
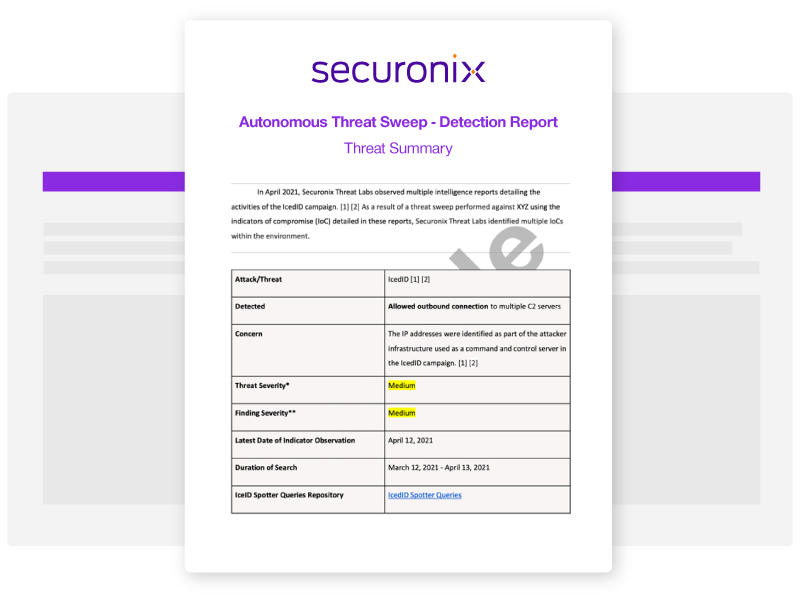
Acting as your own dedicated Cyber Rapid Response Team, Securonix Autonomous Threat Sweeper (ATS) automatically and retroactively hunts for new and emerging threats based on the latest threat intelligence from our Threat Labs Team.
Latest ATS Entries
All indicators of compromise (IOC) and Spotter queries are available on our GitHub repository.
—
- Intel Source:
- Positive Technologies
- Intel Name:
- TA558_Worldwide_Attacks
- Date of Scan:
- 2024-04-16
- Impact:
- MEDIUM
- Summary:
- Researchers at Positive Technologies have discovered a group called TA558 has carried out over 300 attacks worldwide. They are using an old vulnerability called CVE-2017-11882 to spread malware through a campaign called SteganoAmor. This campaign is affecting users in Latin America and other parts of the world. TA558 hides malware within its attacks using a technique called steganography.
—
- Intel Source:
- PaloAlto
- Intel Name:
- Campaign_For_Contact_Forms_Distributes_SSLoad_Malware
- Date of Scan:
- 2024-04-16
- Impact:
- LOW
- Summary:
- Researchers at Palo Alto have noticed that the MSI file’s WebDAV server has stopped operating. They have observed this effort spreading Latrodectus malware in the last few weeks. But Latrodectus is not the MSI linked to this specific infection chain.
—
- Intel Source:
- Blackberry
- Intel Name:
- LightSpy_campaign_returns
- Date of Scan:
- 2024-04-16
- Impact:
- LOW
- Summary:
- Blackberry researchers shared the details of the LightSpy campaign, a mobile espionage operation targeting individuals in Southern Asia, potentially with state-sponsored involvement. The “Title-Abstract” section delves into the technical details of the malware, its Chinese origins, and the advanced techniques used. The “Abstract” section offers recommendations for individuals and organizations to protect themselves. The “LightSpy Returns” section discusses the campaign’s return with expanded capabilities and the threat actor group behind it. The article emphasizes the need for increased vigilance and robust security measures in the targeted region.
—
- Intel Source:
- Proofpoint
- Intel Name:
- Decoding_TA427
- Date of Scan:
- 2024-04-16
- Impact:
- LOW
- Summary:
- Proofpoint researchers discovered a group called TA427, who are really busy causing trouble. They pretend to be experts from North Korea in different fields like education, news, and research. They do this to trick other experts and sneak into their organizations to gather important information. TA427 has been quite successful at this and doesn’t seem to be stopping anytime soon. They’re quick to change their methods and create new identities when needed.
—
- Intel Source:
- Recorded Future
- Intel Name:
- The_spread_of_infostealers_by_a_Russian_cybercriminal_campaign
- Date of Scan:
- 2024-04-15
- Impact:
- LOW
- Summary:
- The Insikt Group has uncovered a large-scale Russian-language cybercrime operation that leverages fake Web3 gaming projects to distribute infostealer malware targeting both macOS and Windows users.
—
- Intel Source:
- Palo Alto, Volexity
- Intel Name:
- Zero_Day_Exploitation_of_Unauthenticated_RCE_Vulnerability_in_GlobalProtect
- Date of Scan:
- 2024-04-15
- Impact:
- HIGH
- Summary:
- Researchers at PaloAlto have identified zero-day exploitation of a vulnerability found within the GlobalProtect feature of Palo Alto Networks PAN-OS. A critical command injection vulnerability in Palo Alto Networks PAN-OS software enables an unauthenticated attacker to execute arbitrary code with root privileges on the firewall. The vulnerability, assigned CVE-2024-3400, has a CVSS score of 10.0.
Source:
https://unit42.paloaltonetworks.com/cve-2024-3400/#post-133365-_ydqdbjg0dngh
https://www.volexity.com/blog/2024/04/12/zero-day-exploitation-of-unauthenticated-remote-code-execution-vulnerability-in-globalprotect-cve-2024-3400/
—
- Intel Source:
- Bitdefender
- Intel Name:
- Malvertising_campaigns_hijack_social_media_to_spread_stealers
- Date of Scan:
- 2024-04-15
- Impact:
- LOW
- Summary:
- Threat actors have been copying AI software such as Midjourney, Sora AI, DALL-E 3, Evoto, and ChatGPT 5 on Facebook to trick users into downloading purported official desktop versions of these AI software. The malicious webpages then download intrusive stealers such as Rilide, Vidar, IceRAT, and Nova Stealer.
—
- Intel Source:
- Sucuri
- Intel Name:
- Embedding_a_credit_card_skimmer_in_a_fake_Facebook_Pixel_tracker_script
- Date of Scan:
- 2024-04-12
- Impact:
- LOW
- Summary:
- Recently Sucuri discovered an interesting case of this: the attackers took that a step further by embedding a credit card skimmer in a well-concealed fake Facebook Pixel tracker script.
Source:
https://blog.sucuri.net/2024/04/credit-card-skimmer-hidden-in-fake-facebook-pixel-tracker.html
—
- Intel Source:
- Esentire
- Intel Name:
- A_series_of_tax_themed_phishing_emails_delivering_the_Remcos_RAT
- Date of Scan:
- 2024-04-12
- Impact:
- LOW
- Summary:
- Last month, eSentire researchers detected a series of tax-themed phishing emails delivering the Remcos RAT as the final payload through GuLoader. The phishing email contained the link to the password-protected ZIP archive hosted on Adobe Document Cloud.
Source:
https://www.esentire.com/blog/tax-season-alert-beware-of-guloader-and-remcos-rat
—
- Intel Source:
- Trellix
- Intel Name:
- Observed_spike_of_LockBit_related_activity_of_vulnerabilities_in_ScreenConnect
- Date of Scan:
- 2024-04-12
- Impact:
- MEDIUM
- Summary:
- Recently, Trellix Researchers have observed a rise in LockBit-related cyber activity in vulnerabilities in ScreenConnect. Researchers are confident that the cybercriminals group behind LockBit ransomware partially restored their infrastructure and created a feeling that the LE actions did not affect their normal operation.

Shared Security Content on Sigma
Securonix Threat Labs publishes up-to-date IOCs and threat hunting queries on Sigma, allowing you to tap into a vast community of collective defense and stay ahead of emerging threat research.
What's New from Threat Labs
-
BlogSecuronix Threat Research Knowledge Sharing Series: Detecting DLL Sideloading Techniques Found In Recent Real-world Malware Attack ChainsLearn More
-
BlogSecuronix Threat Research Security Advisory: Analysis of New DEEP#GOSU Attack Campaign Likely Associated with North Korean Kimsuky Targeting Victims with Stealthy MalwareLearn More
-
BlogSecuronix Threat Research Security Advisory: Analysis and Detection of STEADY#URSA Attack Campaign Targeting Ukraine Military Dropping New Covert SUBTLE-PAWS PowerShell BackdoorLearn More