SIEM Defined
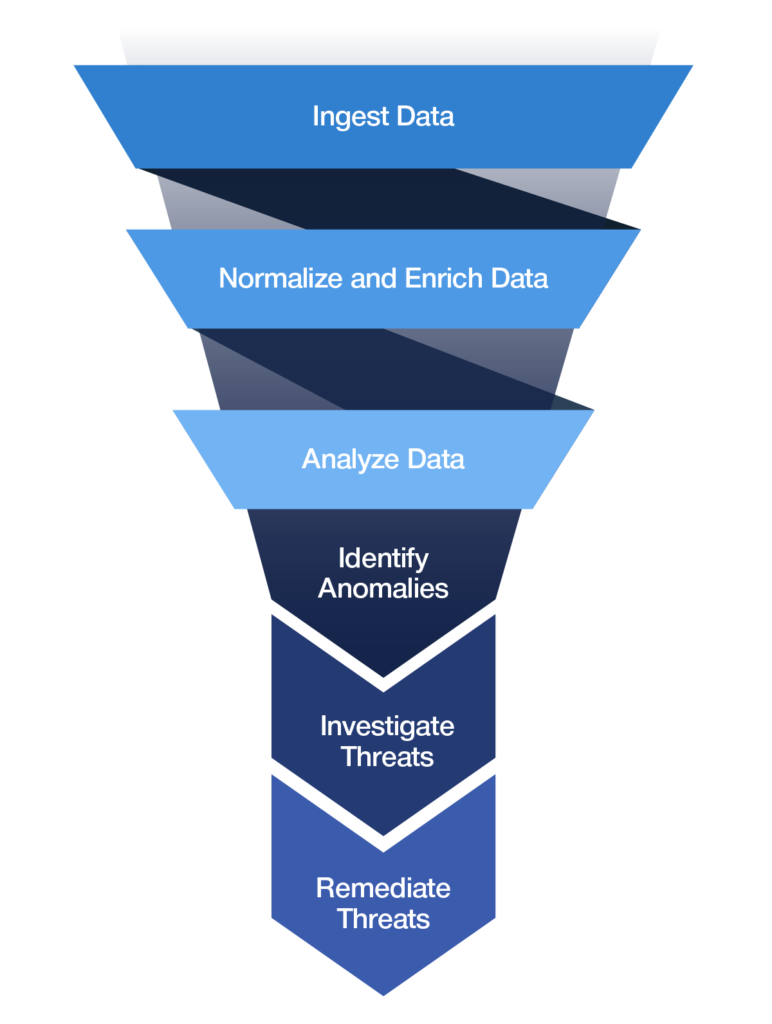
At a basic level, a security information and event management (SIEM) solution is designed to ingest all data from across your enterprise, normalize the data to make it searchable, analyze that data for anomalies, and then investigate events and remediate incidents to kick out attackers.
SIEM Was Invented To Solve Two Challenges
Complex Architectures Increase the Ways Attackers Can Gain Access
Organizations are using a more distributed architecture than ever before. The more complex an architecture, the more cracks a sophisticated attacker can utilize. This increases the company’s risk of a cybersecurity incident.

Enterprises Generate More Data Than a Human Can Review in Time To Stop an Attack
When monitoring for suspicious activity, there is more data to process than any number of analysts could ever review without help. Analysts need technology to help them find and flag the most important events to investigate, or a policy violation that needs to be mended.
How Did SIEM Evolve?

SIM and SEM
Information technology security in the 1990’s was heavily focused on protecting the perimeter. Solutions developed during this time were basic and came as either a security information management (SIM) or security event management (SEM) solution. Early solutions were also built on proprietary data bases that locked customers into one vendor’s technology.
SIEM
As data became cheaper and technology more powerful, SIEMs became better able to ingest, process, and store data. SIEMs were now able to use signature-based alerts to find threats in your data. However, there were also serious drawbacks to this generation of SIEMs. Because they relied on signatures, they could only find threats that were already known. They had a very limited capability to discover zero-day or unknown threats.
Next-Generation SIEM
Built on a big data platform that provides unlimited scalability and built in the cloud, for the cloud. A next-generation SIEM includes log management, behavior analytics-based advanced threat detection and automated incident response in a single platform.
The Evolution of SIEM Features and Capabilities
The best method to understanding next-generation SIEM is to understand the background of how the solution has evolved over the past couple of decades. The chart below helps trace the evolution of the features and capabilities of SIEM across time. Today’s next-generation SIEM requires less maintenance, grows with your data, and surfaces actual threats instead of false positives.
| Early SIEM SIM/SEM | SIEM | Next-Generation SIEM | |
|---|---|---|---|
| Deployment | On-Premises | On-Premises | SaaS |
| Form Factor | Appliance with Proprietary Technology | Appliance | Cloud |
| Scalability | Severely Limited | Limited | Unlimited |
| Data Storage | Proprietary Database | Proprietary Database | Open Source / Big Data |
| Infrastructure Management | Requires Several FTE To Manage | Requires Several FTE To Manage | Solution Is Managed by the Vendor |
| Log Management | Included Limited by Proprietary Database Capabilities |
Included Limited by Proprietary Database Capabilities |
Included With Extensive Data Lake Capabilities |
| Threat Detection Analytics | Primarily Search-Based Detection | Basic, Signature-Based Alerts Find Known Threats Prone to False Positives |
Advanced Detection With Machine Learning and Advanced Analytics To Find Known and Unknown Threats, and Reduce False Positives |
| Security for Cloud Applications and Infrastructure | Not Included | Very Limited | Included Cloud-Native SIEM Is the Best Protection for Cloud and Hybrid Infrastructure |
| Threat Hunting | Not Included | Very Manual, With Workarounds | Included |
| Reports and Compliance | Limited | Included Manual and Time Consuming |
Included Easy To Create |
| Incident Response | Not Included | Included Manual and Time Consuming |
Included No Need To Switch Between Tools – Seamless |
| Security Orchestration | Not Included | Included Manual and Time Consuming |
Included No Need To Switch Between Tools – Seamless |
How Does a SIEM Work?
Collect Data
Most SIEM solutions collect data from across the organization using agents installed on various devices including endpoints, servers, and network equipment, as well as other security solutions, such as firewalls or other network security appliances.
Next-generation SIEM solutions include support for cloud applications and infrastructure, enterprise applications, identity and HR data, and non-technical data feeds as well.
Enrich Data
Data enrichment adds context to an event. SIEM solutions should enrich incoming data with identity, asset, geolocation, and threat intelligence to aid in investigations. Data enrichment fills in critical information that a SIEM needs in order to correlate related events together and aid in threat detection.
Store Data
After data enrichment, security data is stored in a database. There the data can be searched through and referenced to during investigations. Sometimes only enriched data is stored, but sometimes the unenriched data is stored as well. It all depends on what the organization requires.
Next-generation SIEM leverages an open source, big data architecture in order to take advantage of their unlimited scalability and ability to store historical data in a way that it can easily be searched.
Apply Correlation and Analytics
SIEM solutions use different techniques to draw usable conclusions from the data and find anomalies. These analytics techniques vary widely from vendor to vendor.
Legacy SIEMs rely on simple correlation and signature-based alerts. They are prone to error, produce a lot of noise in the form of false positives, and can only find known threats. This causes analysts to waste time chasing events that may or may not be credible threats.
A next-generation SIEM uses advanced analytic techniques, beyond signature-based approachs, to catch known and unknown threats. They use sophisticated machine learning algorithms to detect threats more accurately.
User and entity behavioral analytics (UEBA) is one type of advanced analytics that is integrated into next-generation SIEMs in order to provide better detection. Another technique used are threat chain models. These models help stitch together connected alerts in order to consolidate separate but related alerts into a threat sequence, increasing the risk score of the overall threat.
Investigate and Mitigate Threats
At a basic level, a SIEM should have the ability to integrate with a third-party security orchestration, automation, and response (SOAR) solution to assist analysts as they investigate and mitigate potential threats. A SOAR solution gives analysts a workbench to collect information, track steps taken during the investigation, and remember how the threat was mitigated or whether it wasn’t a real threat.
A next-generation SIEM will incorporate SOAR capabilities natively into the platform for increased security operations efficiency and ROI. This includes playbooks, orchestration workflows, and automation. Save your team time by leveraging machine-learning powered automation that can learn how to solve your problems and guide your T1 analysts in the right direction faster.
Provide Data Insights and Reporting
A next-generation SIEM gives you the ability to search across your data quickly, allowing you to dig into alerts and search for threat actors and indicators of compromise.
You can also pivot on any entity in order to develop valuable threat context and get a full 360-degree view of the attack. Visualized data can be saved as dashboards or exported in a standard data format. You can also use out-of-the-box reports or create ad-hoc reports as needed for your incident response and compliance needs.
The Top 5 SIEM Use Cases
Cloud Security
With the rapid adoption of cloud technologies, more and more data is being moved to the cloud. Some of the key security concerns related to the adoption of cloud technologies include how to identify unauthorized activities, privilege misuse or compromise, unauthorized data sharing, and data exfiltration.
Legacy, on-premises SIEMs were created before the cloud, and struggle to monitor cloud infrastructure and applications.
A cloud-native next-generation SIEM allows you to extend seamless security monitoring across all major cloud infrastructure and application technologies. Deployed in the cloud, to protect the cloud, next-generation SIEM can analyze user entitlements and events to look for malicious activity. You can also eliminate your security blind spots by correlating on-premises data with cloud data and detecting actionable threat patterns.
Insider Threat Detection
Insider threats are concerning because these attackers don’t need to penetrate your perimeter, they’re already inside it. They can be your employees, contractors, or business associates. They might be a malicious threat actor themselves, or their account might have been compromised by external attackers, giving the attackers inside access to your infrastructure and data.
In either case, the perpetrator wants to remain unnoticed, stealthily sniffing around and collecting sensitive data to exfiltrate. The attacker may be looking for confidential customer records, credit card data, research and development designs, business strategy documentation, and other sensitive business information. If compromised, this information could cause considerable damage to your company, its place in the industry, and its relationship with consumers and investors.
Legacy SIEMs generally struggle to detect insider threats.
Next-generation SIEMs provide innovative, behavior-based analytics techniques that, in conjunction with peer group analysis techniques, detect variations in normal patterns when it comes to the access and usage of internal data sources. By comparing not only historical usage, but the usage of colleagues and team members, next-generation SIEMs are able to remove the noise associated with incremental changes in user behavior and highlight concerning activity.
Incident Response
Effective incident response is critical in order to respond to incidents quicker and decrease attacker dwell time. A SIEM should provide built-in SOAR capabilities that include incident response playbooks with configurable, automated actions. Comprehensive incident management and workflow capabilities also allow multiple teams to collaborate on an investigation as needed. A SIEM will also be capable of integrating with third-party security orchestration and case management solutions.
A next-generation SIEM will come with an artificial intelligence-based recommendation engine that can suggest remediation actions based on analysts’ previous behavior patterns to decrease your mean time to respond.
Threat Hunting and Investigation
The ability to perform threat hunting is critical in order to understand the true impact of access- and activity-based attacks and data breaches. By developing a detailed and contextual view of the attack vector, security analysts can more easily develop policies, countermeasures, and incident response processes to mitigate and ultimately remove the threat.
Effective threat hunting is enabled by blazing-fast search capabilities and the ability to search for threat actors or indicators of compromise by pivoting on an entity in order to develop valuable threat context.
By creating a 360-degree view of user access and activity behavior, threat hunters can identify the potential for abnormal activity, but also help investigate incidents through detailed analysis techniques, reporting, and contextual data.
Maintain Compliance
For many industries, adhering to compliance standards is critical. A SIEM can help by providing reports to demonstrate compliance and aid in auditing. Look for a SIEM that includes all the major compliance mandates, like PCI DSS, SOX, HIPAA, FISMA, and ISO 27001, without additional cost.
Securonix Next-Gen SIEM
A cloud-first next-generation SIEM with compelling detection and response ROI and zero infrastructure to manage. Our solution provides a single pane of glass for detection and response in the cloud, where a company’s data resides, and our integrated UEBA surfaces high-priority threats instead of false positives.
Want to Learn More About Securonix Next-Gen SIEM?
Schedule Your Personalized Demo
By clicking submit you agree to our Privacy Policy.
By clicking submit you agree to our Privacy Policy.










