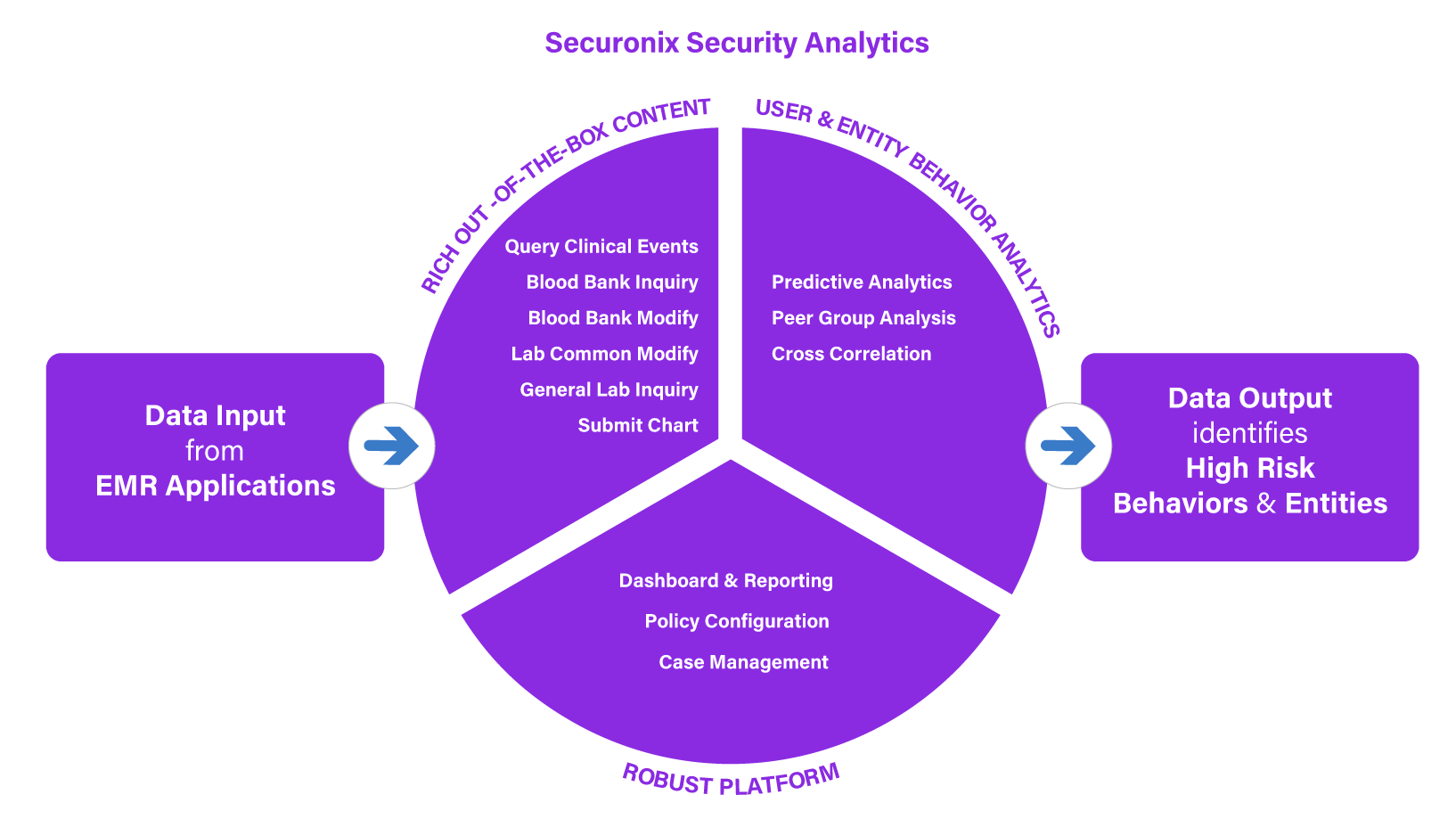
Healthcare Cybersecurity Solutions
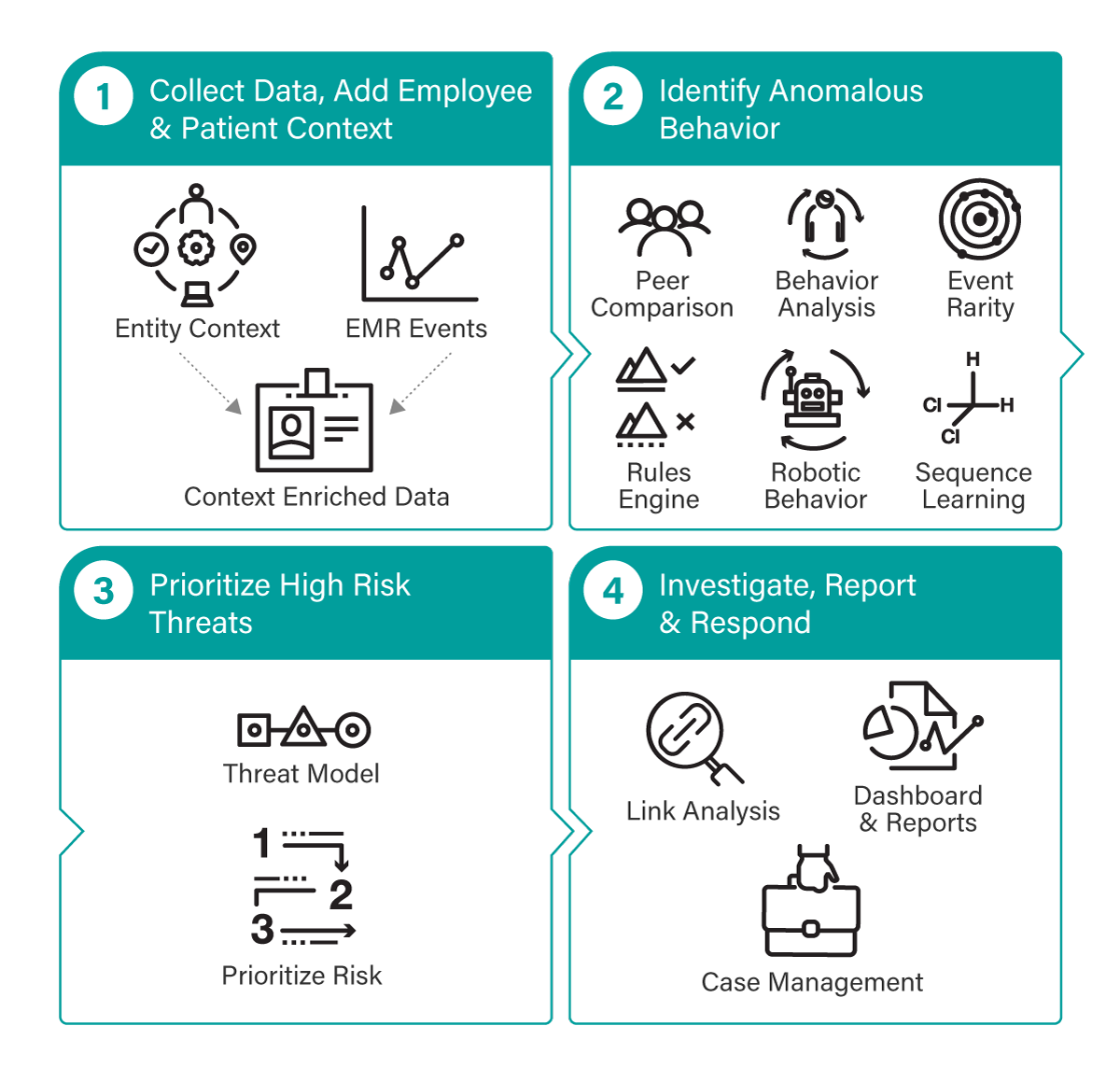
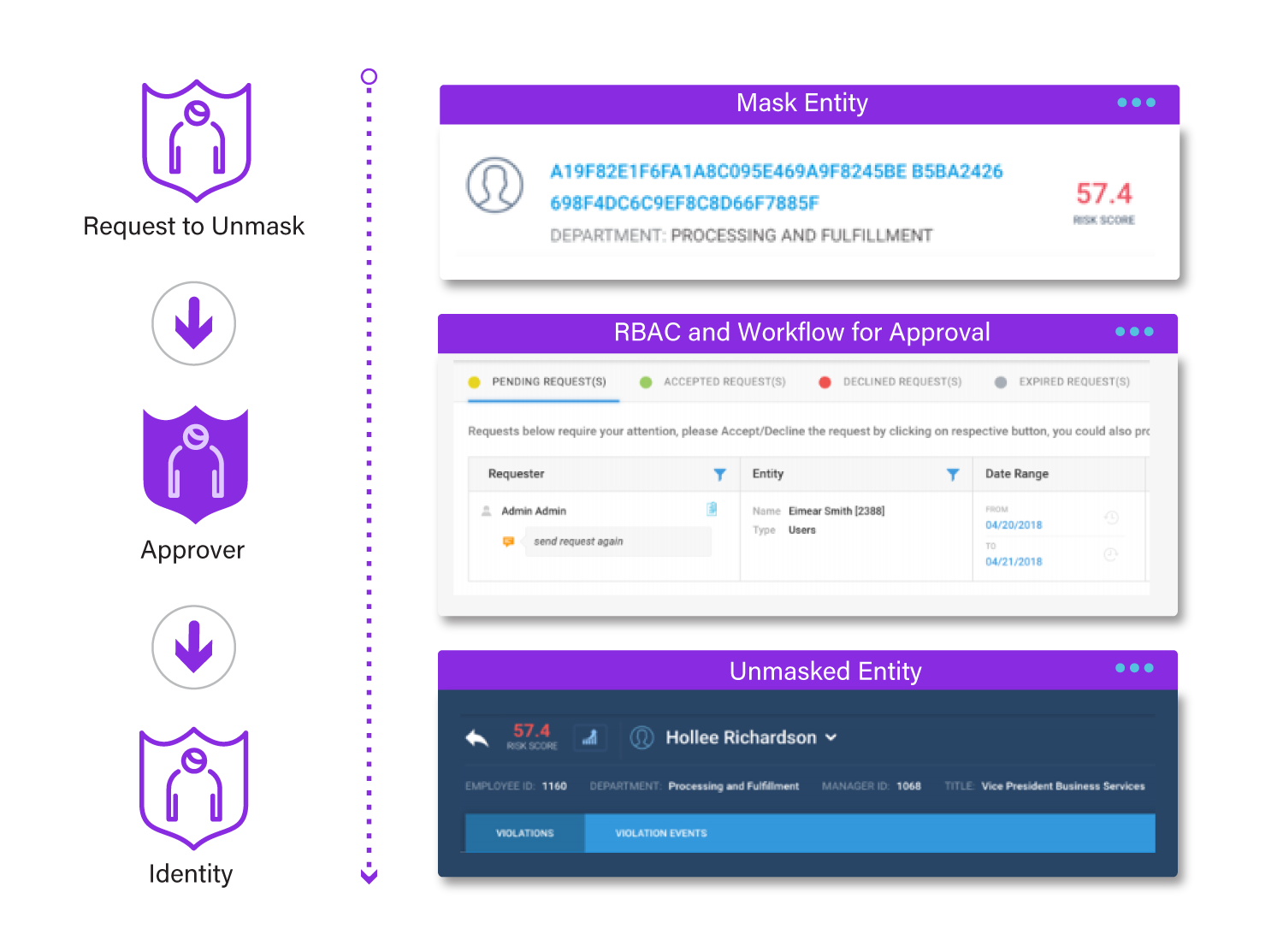
Ensure patient safety, protect sensitive medical information, and keep healthcare services operational with our advanced security monitoring and industry-leading behavior analytics. Our integrated solution helps you monitor user interactions with patient records, stay compliant with regulatory requirements, and prevent cyber threats before they impact your organization.