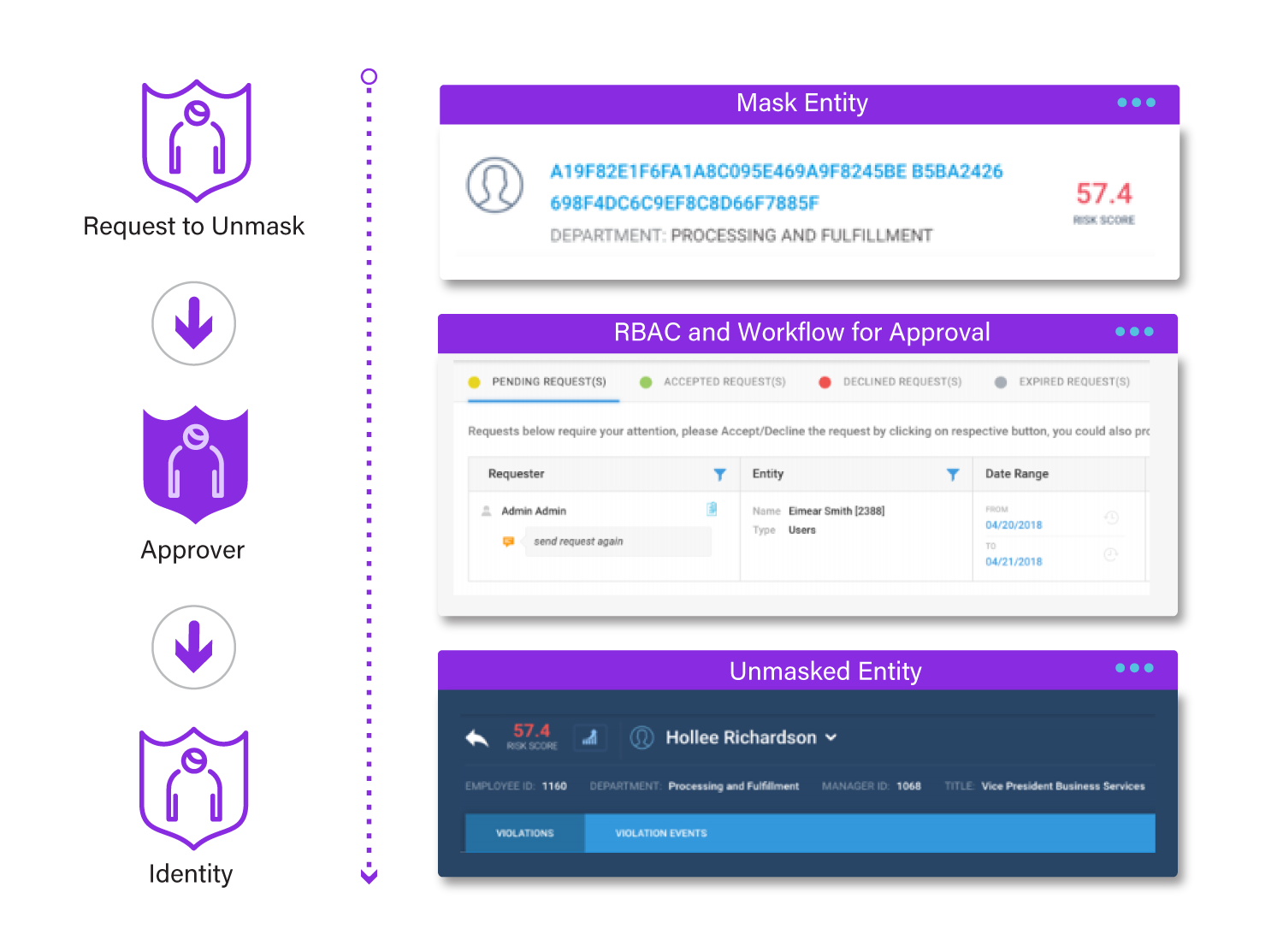
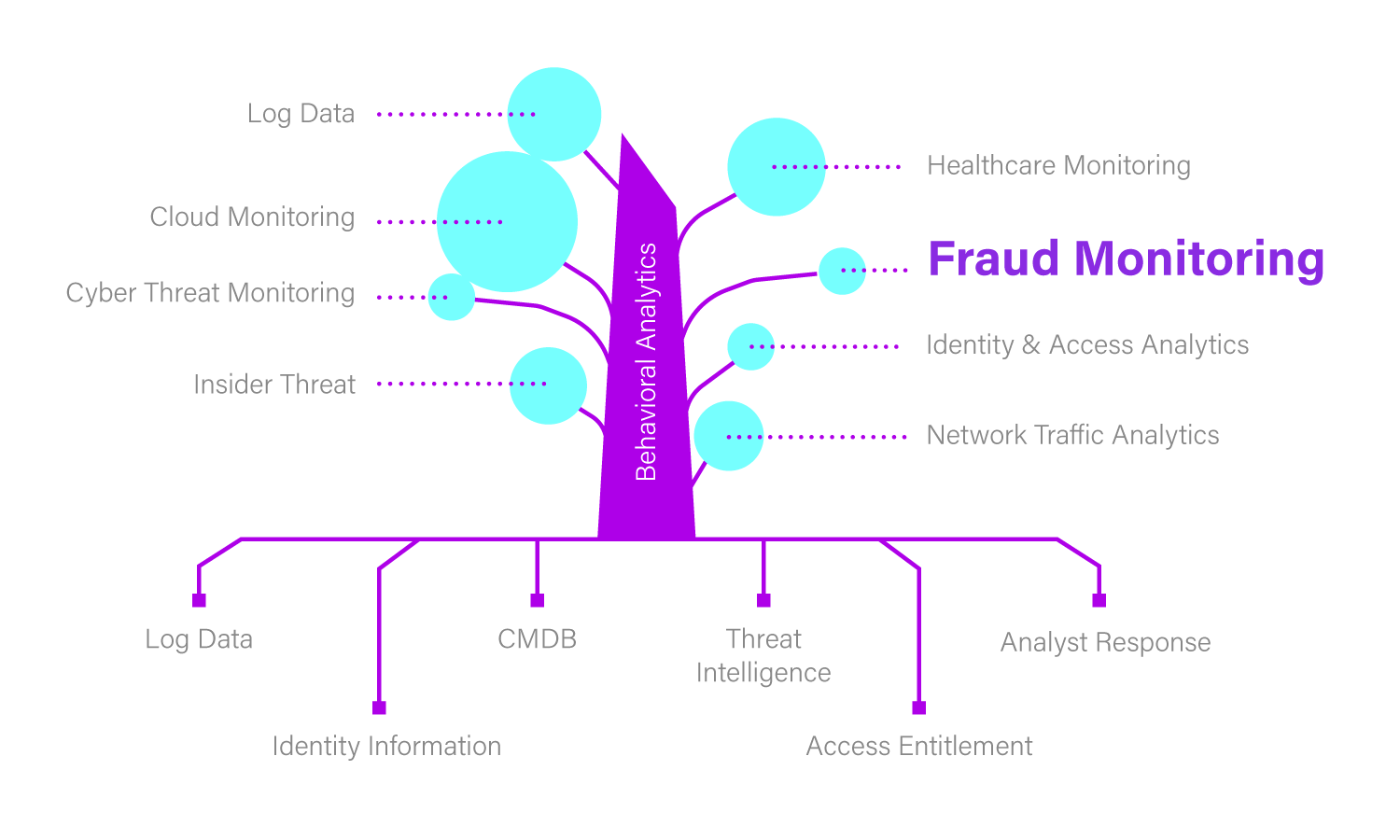
Cybersecurity Solutions for Financial Services
Proactively Safeguard Financial Data with Advanced Threat Detection
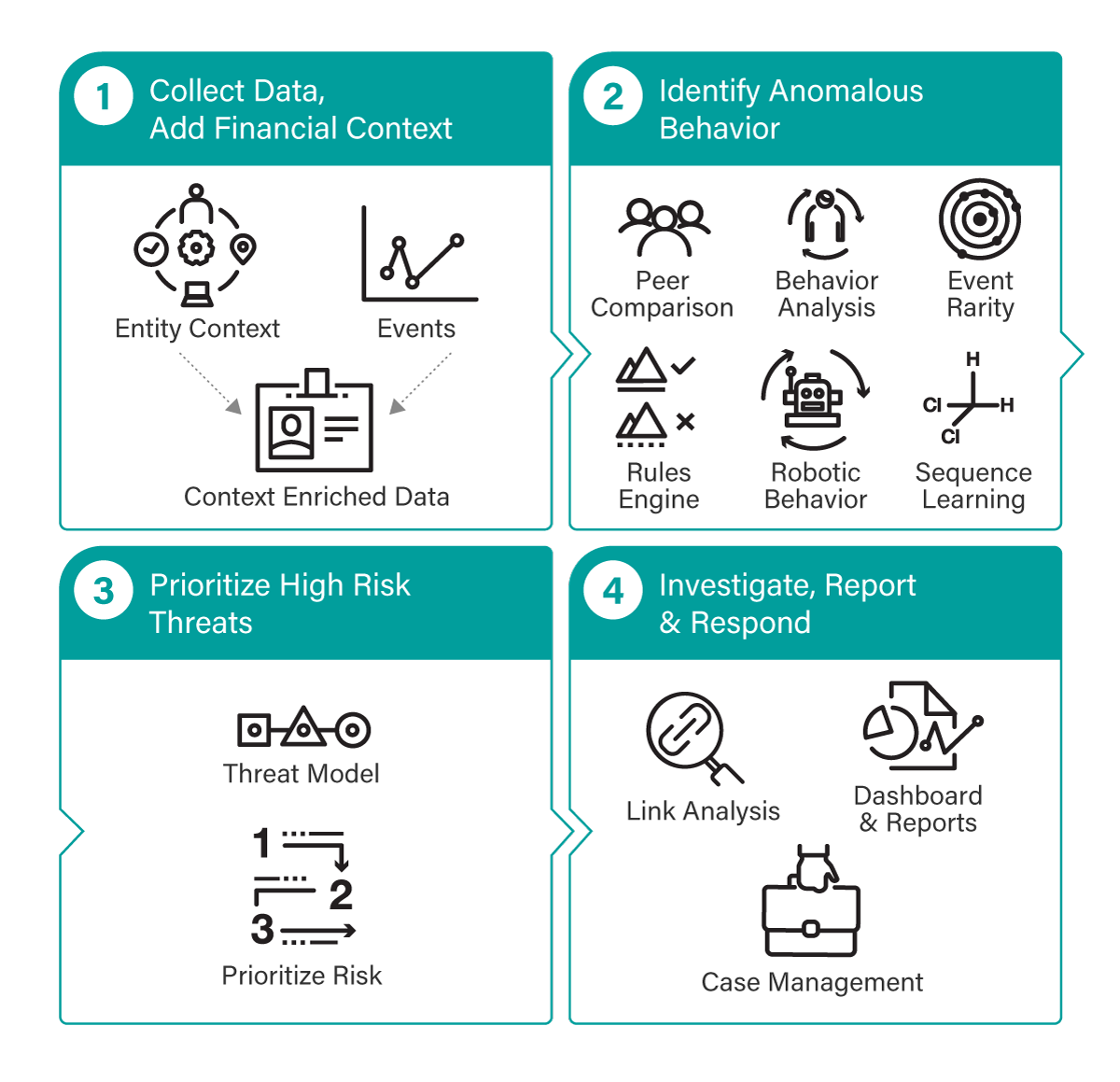
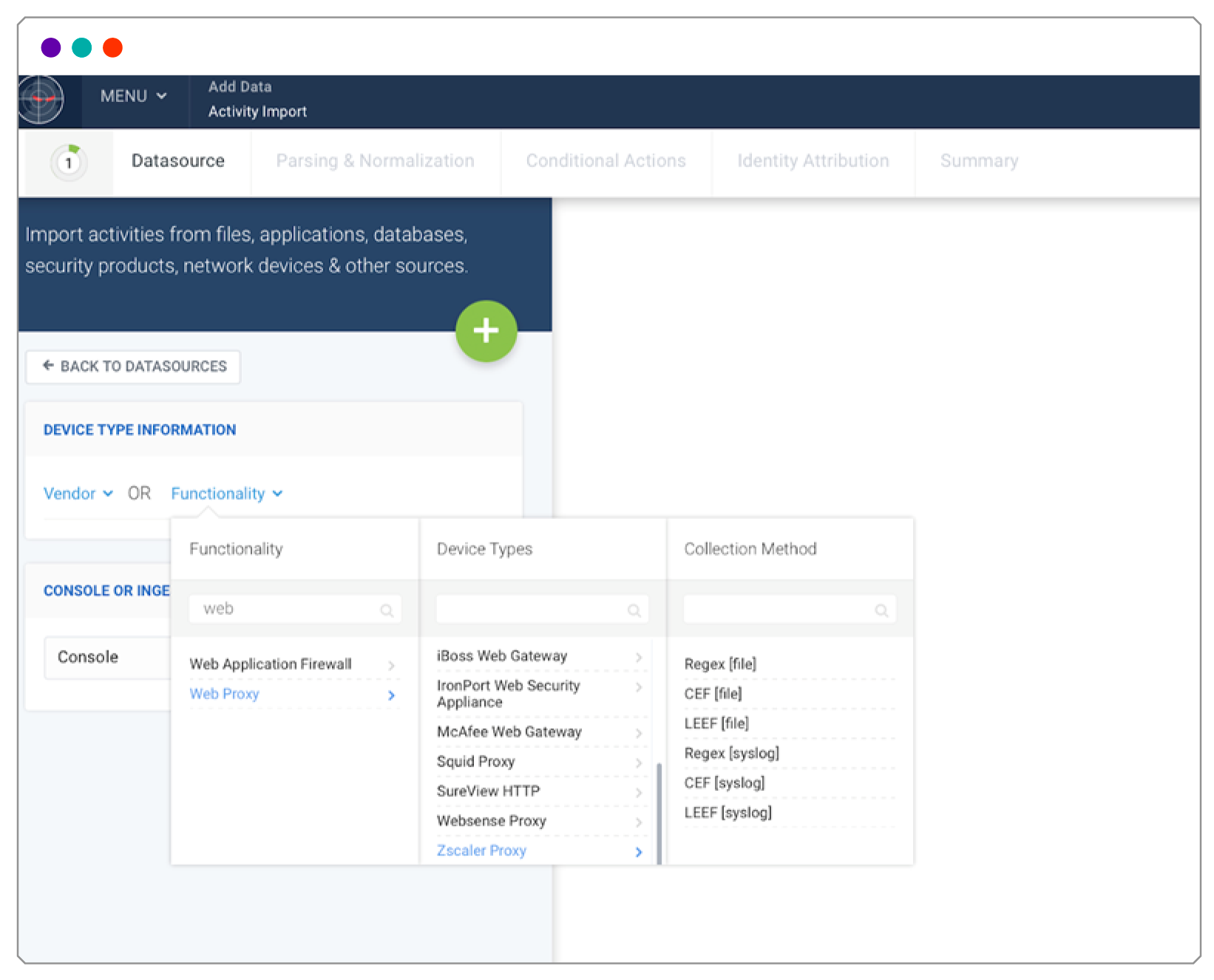
Protect your financial institution from fraud, data breaches, and compliance risks with Securonix’s Unified Defense SIEM. Our AI-Reinforced threat detection and continuous monitoring solutions help identify suspicious activities before they become serious threats.