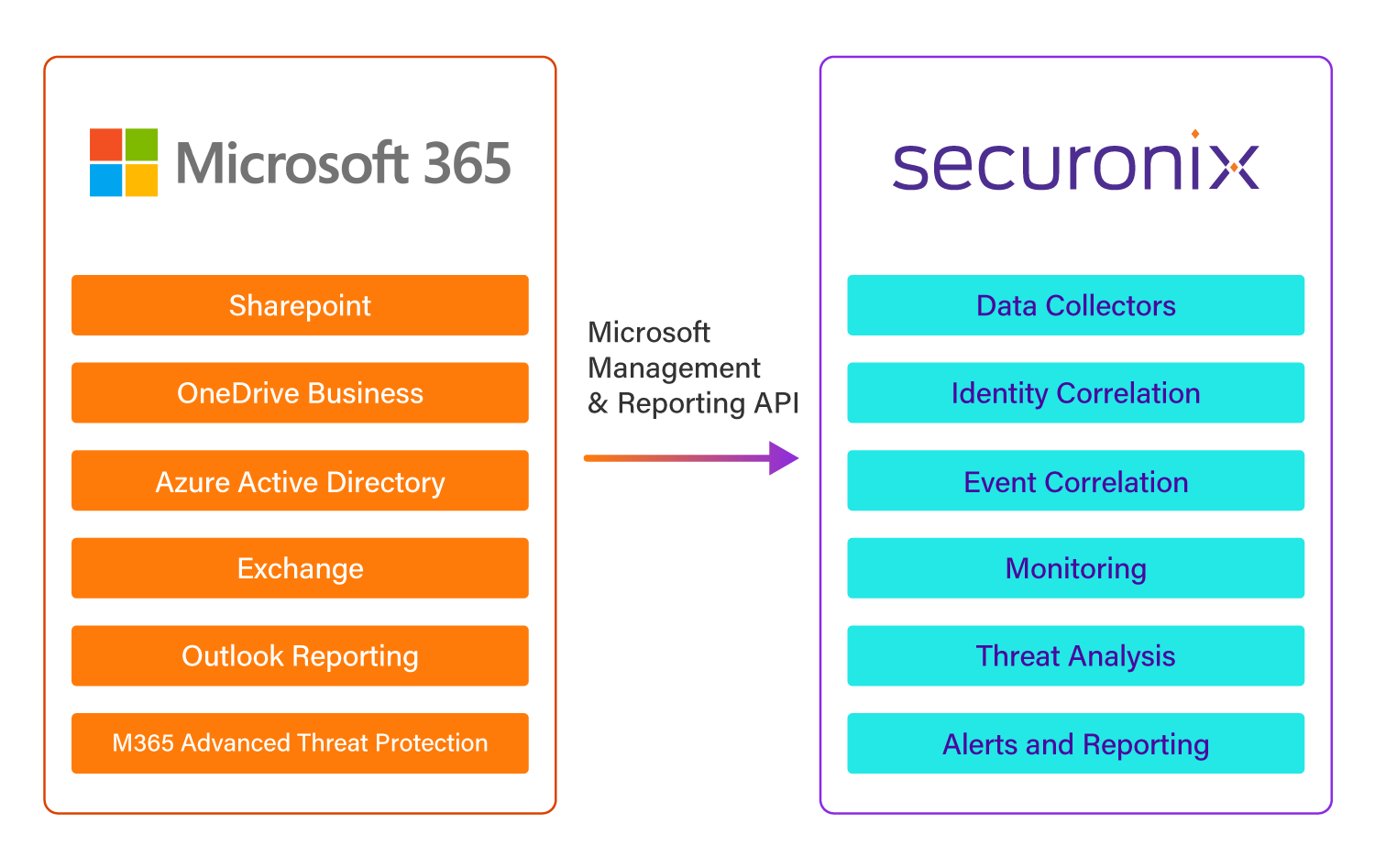
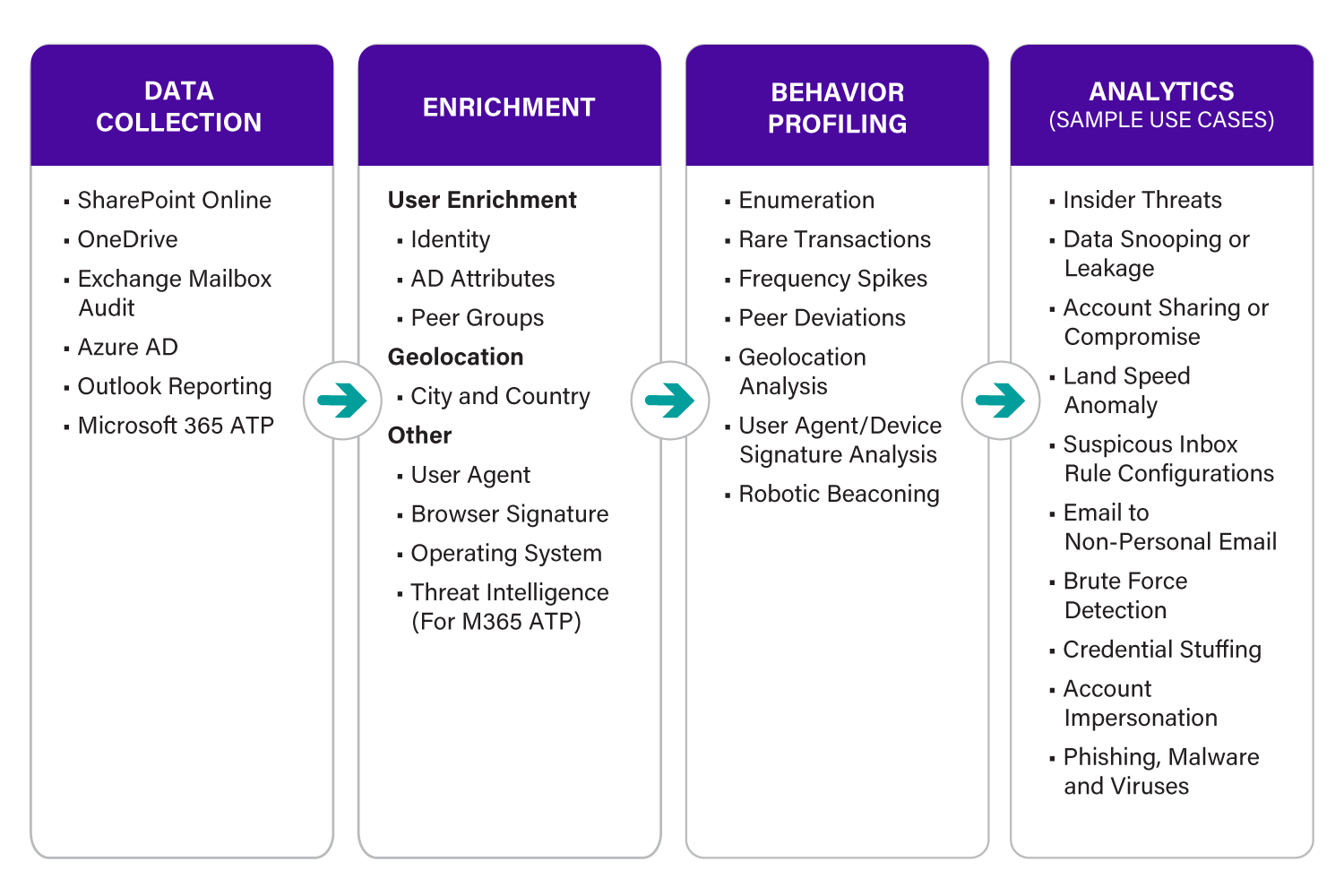
Microsoft 365 Security Monitoring Software
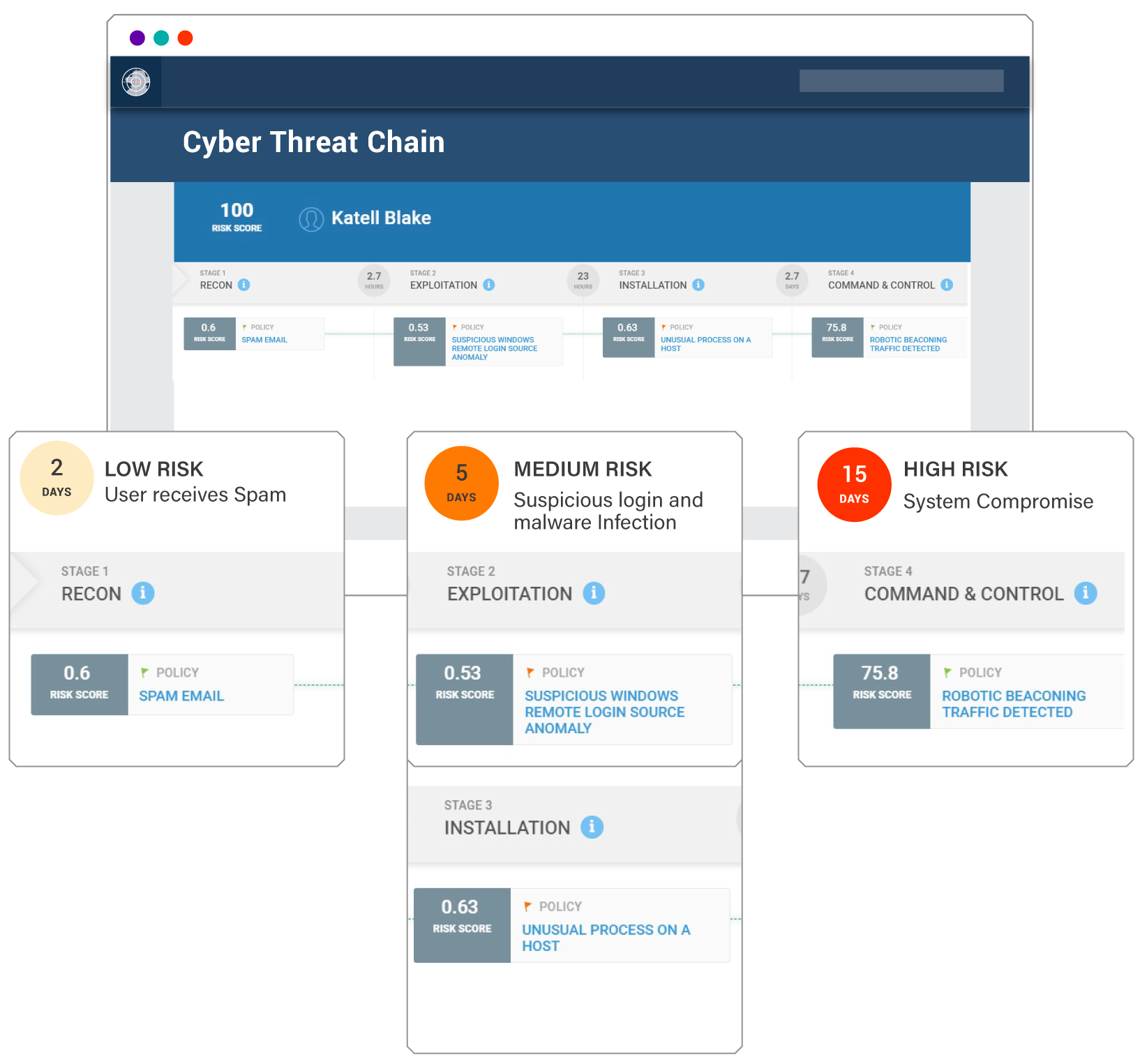
Protect your Microsoft 365 environment from emerging cyber threats with Securonix Next-Gen SIEM. Our advanced security monitoring software provides real-time visibility into potential security risks, ensuring that your organization remains safeguarded from phishing attacks, data breaches, and unauthorized access.