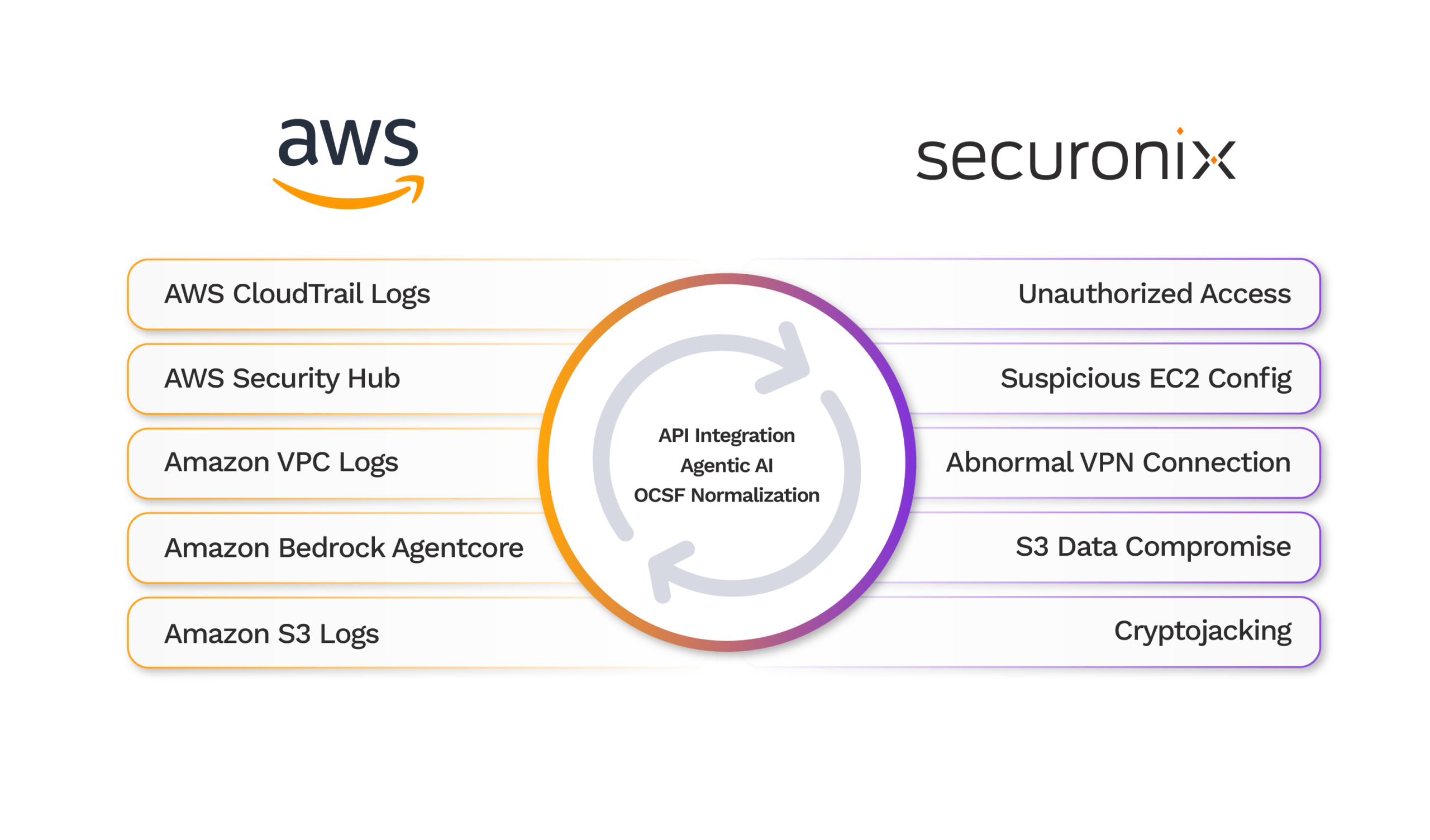
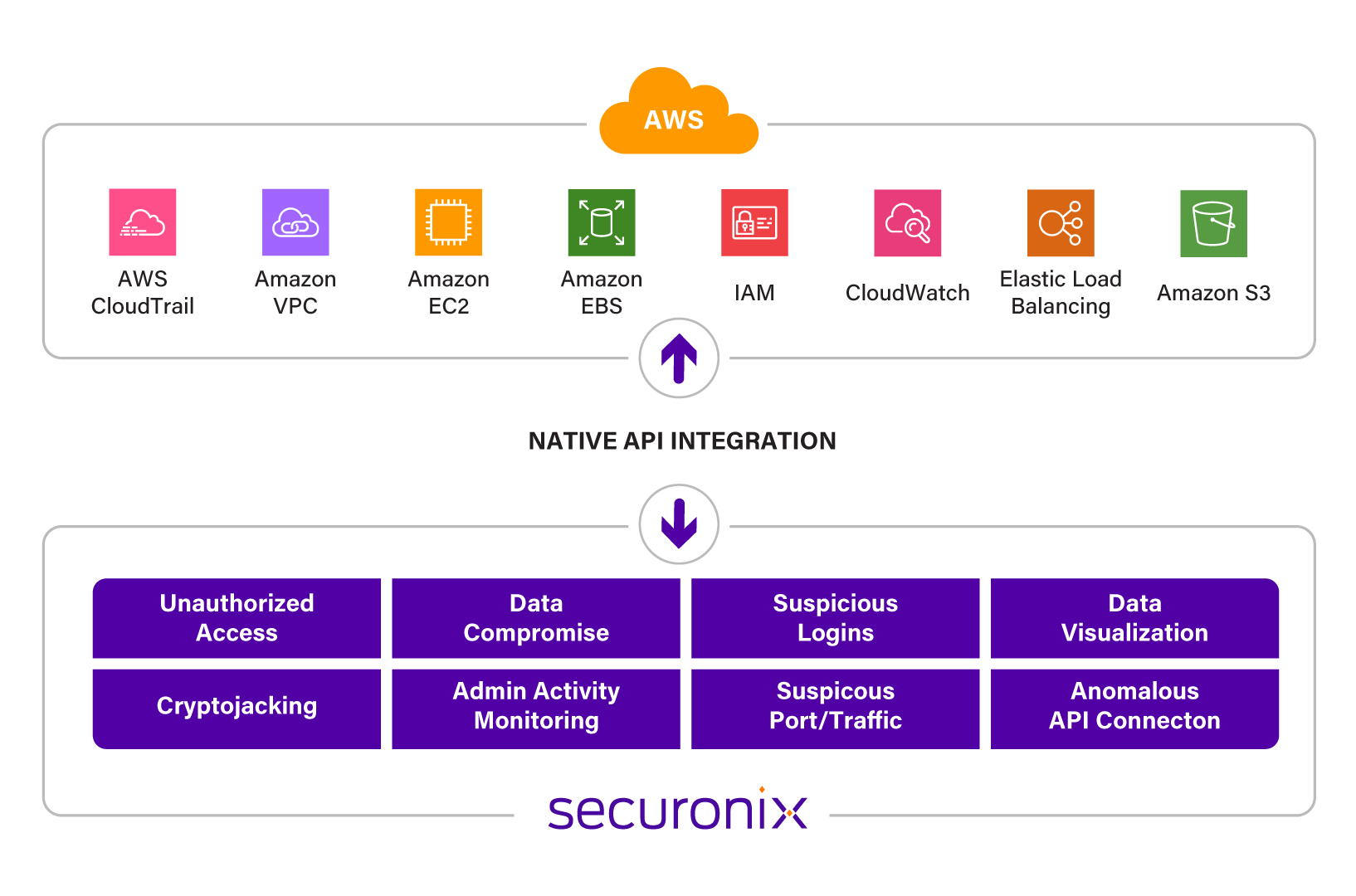
Amazon Web Services Security Monitoring Solution – AWS SIEM
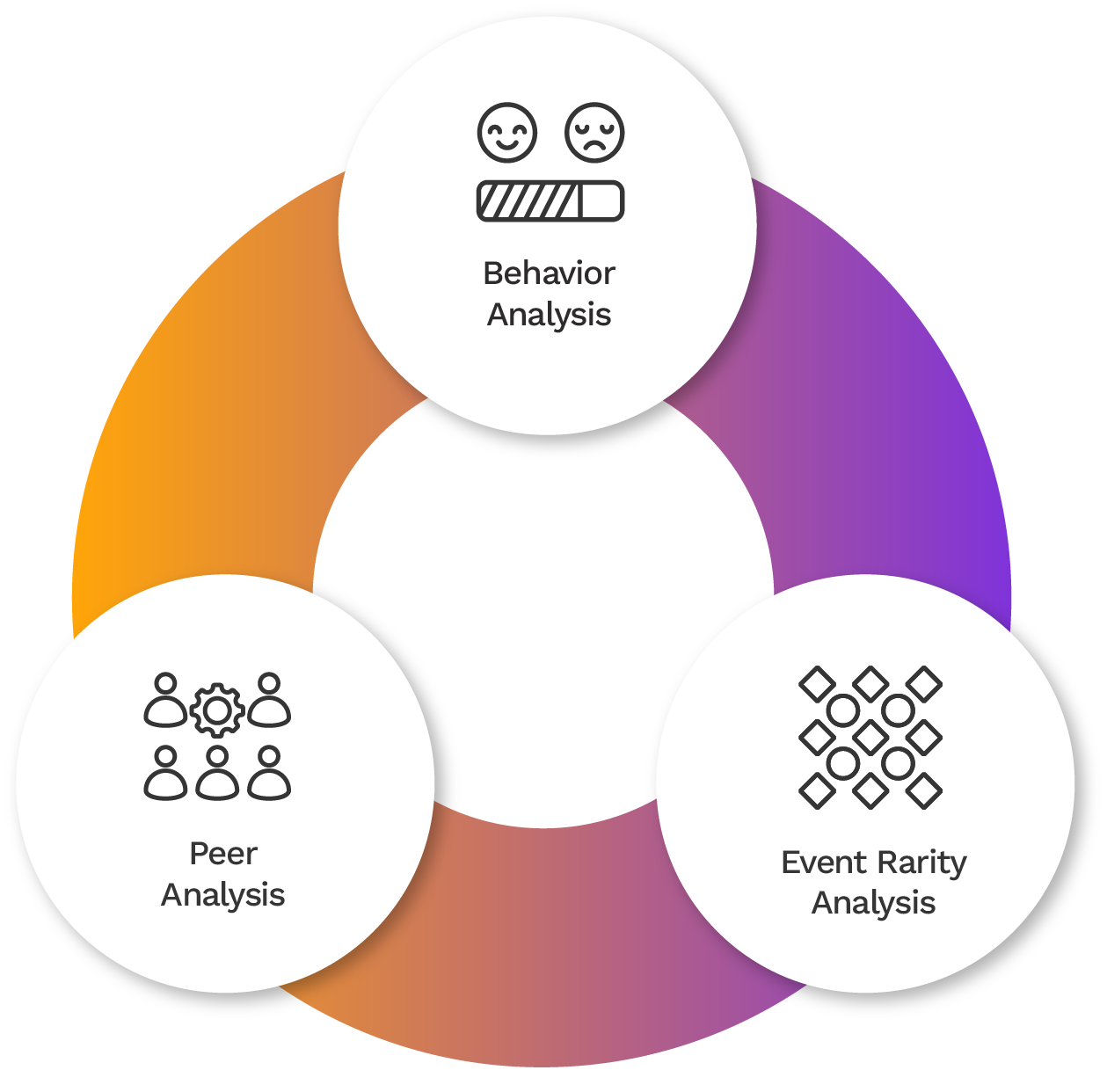
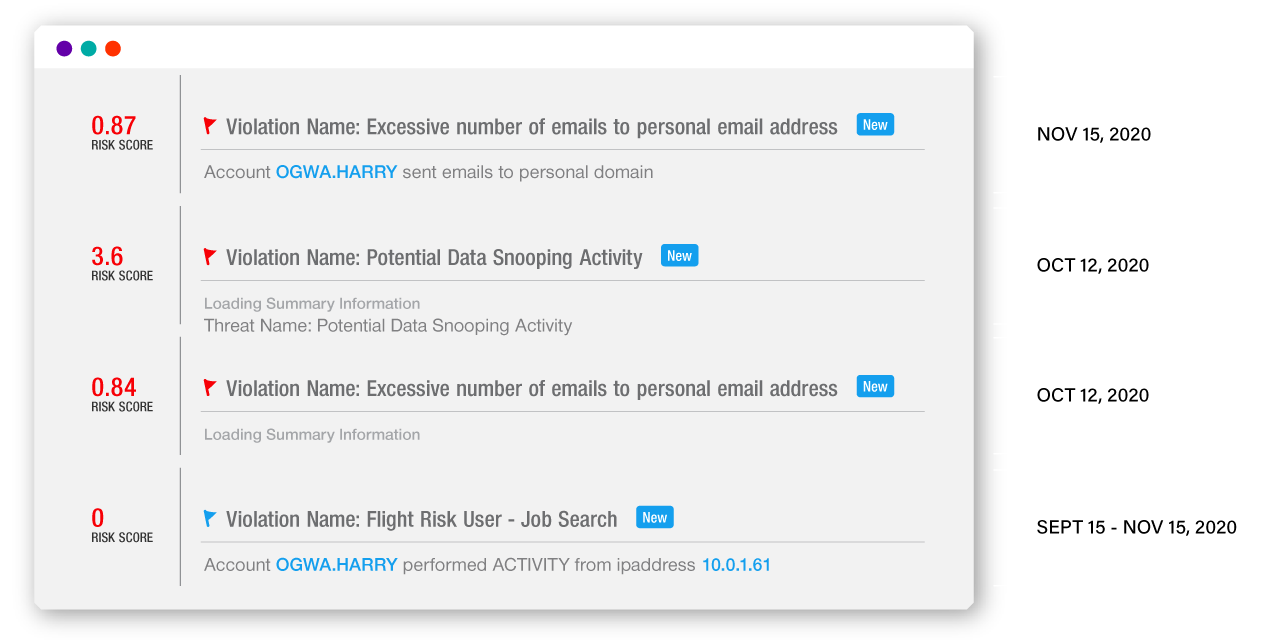
Enhance your AWS cloud security with a powerful monitoring solution designed to identify patterns, detect potential threats, and safeguard your infrastructure using advanced AWS SIEM technology and native AWS Security Hub integration.