- Why Securonix?
- Products
-
- Overview
- Securonix Cloud Advantage
-
- Solutions
-
- Monitoring the Cloud
- Cloud Security Monitoring
- Gain visibility to detect and respond to cloud threats.
- Amazon Web Services
- Achieve faster response to threats across AWS.
- Google Cloud Platform
- Improve detection and response across GCP.
- Microsoft Azure
- Expand security monitoring across Azure services.
- Microsoft 365
- Benefit from detection and response on Office 365.
-
- Featured Use Case
- Insider Threat
- Monitor and mitigate malicious and negligent users.
- EMR Monitoring
- Increase patient data privacy and prevent data snooping.
- MITRE ATT&CK
- Align alerts and analytics to the MITRE ATT&CK framework.
- MSSPs
- Scale multi-tenant security with predictable economics.
-
- Resources
- Partners
- Company
- Blog
Threat Research
Securonix Threat Labs January 2026 Intelligence Insights
Authors: Dheeraj Kumar and Nitish Singh
The Monthly Intelligence Insights report provides a summary of top threats curated, monitored, and analyzed by Securonix Threat Labs in January 2026. The report also includes a synopsis of the threats, indicators of compromise (IoCs), tactics, techniques, and procedures (TTPs), and related tags. Each threat has a comprehensive summary from Threat Labs and search queries from the Threat Research team. For additional information on Threat Labs and related search queries used via Autonomous Threat Sweeper to detect the below-mentioned threats, refer to our Threat Labs home page.
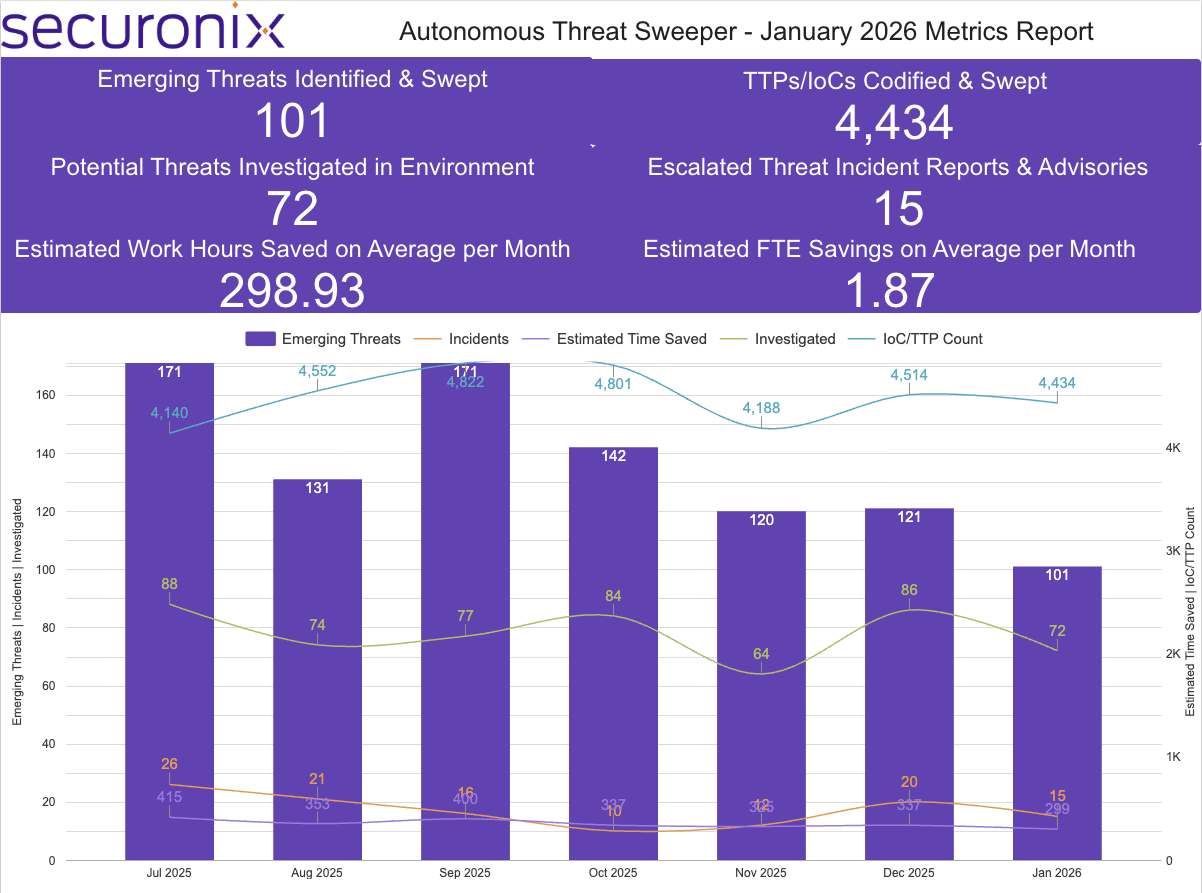
Last month, Securonix Autonomous Threat Sweeper identified and analyzed 4,434 TTPs and IoCs; identified 101 emerging threats; investigated 72 potential threats; and elevated 15 incidents. The top data sources swept against include IDS / IPS / UTM / Threat Detection, Data Loss Prevention, Endpoint Management Systems, and Email / Email Security.
In January 2026, the Autonomous Threat Sweeper team observed sustained acceleration in exploitation-driven intrusions and ransomware access optimization, with attackers blending deceptive entry techniques, supply-chain compromise, and resilient C2 infrastructure to reduce time-to-impact. Social engineering chains remained prominent, including PHALT BLYX’s fake BSOD execution masking and the modular SHADOW#REACTOR campaign, while advanced clusters such as UAT-8837 targeting critical infrastructure, UAT-7290 focusing on telecommunications, and UAC-0190 deploying PLUGGYAPE reflected continued investment in stealthy, long-term access; MuddyWater’s RustyWater evolution further highlighted a shift toward Rust-based tooling for evasion and portability. Malware delivery increasingly leveraged trusted software narratives, as seen in Operation Nomad Leopard activity, backdoored legitimate downloads, AI-enabled Gobruetforcer credential automation, trojanized Office Assistant distribution, and a supply-chain compromise impacting eScan antivirus, alongside Sliver C2 hosted on compromised FortiWeb firewalls to blend into perimeter assets. Ransomware operations also advanced in scale and precision, with LockBit 5.0 increasing affiliate tempo, Medusa abusing RMM tools for lateral movement, and regionally focused campaigns such as CrazyHunter targeting Taiwan’s healthcare sector, reinforcing a broader pattern of deceptive access, upstream trust exploitation, perimeter-adjacent C2, and faster, sector-aligned monetization.
Securonix Threat Research Highlights – Originally published in January 2026
January’s Securonix Threat Research highlights a clear attacker trend: keep payloads off disk, blend into trusted processes, and push execution onto the user or legitimate Windows tooling. Across two distinct campaigns: PHALT#BLYX and SHADOW#REACTOR, threat actors paired high-confidence deception with living-off-the-land execution to reduce detection surface area and complicate incident response.
PHALT#BLYX operationalizes social engineering into an execution primitive. Victims are lured via Booking.com-themed phishing designed to trigger urgency (large Euro-denominated charges), then redirected to a high-fidelity fake Booking.com page that simulates browser failure and escalates into a fake BSOD. The key pivot is “ClickFix”, users are instructed to open the Windows Run dialog and paste/execute a malicious PowerShell command (clipboard-injected), effectively bypassing security controls that are stronger against automated execution.
Once executed, the dropper locates a legitimate msbuild.exe, downloads an MSBuild project file (v.proj), and uses MSBuild trusted proxy execution to run embedded logic, an evasion-forward shift from earlier mshta-based tradecraft.
Downstream behaviors focus on durability and stealth: Windows Defender exclusion tampering (including ProgramData and common extensions) and persistence via Startup Internet Shortcut (.url) files that point to a local executable (file://), plus process masking via injection into legitimate binaries like aspnet_compiler.exe.
SHADOW#REACTOR demonstrates how commodity RAT delivery has matured into a modular, self-repairing, file-light framework. The infection chain begins with an obfuscated VBS launcher executed via wscript.exe, which invokes a PowerShell downloader that retrieves fragmented, text-based payloads from attacker infrastructure. Those fragments are reconstructed into encoded loaders and decoded in memory by a .NET Reactor–protected assembly, culminating in the staged delivery of Remcos RAT.
Key campaign mechanics emphasize evasion through format and execution context: payload movement via plain-text intermediates (qpwoe*.txt / teste*.txt / config.txt), reflective .NET loading, and late-stage abuse of MSBuild.exe as a LOLBin to complete execution while maintaining a trusted process lineage.
The .NET Reactor loader acts as the orchestration center, decoding strings, de-obfuscating paths for relaunch logic, and controlling configuration retrieval via encoded/reversed URLs, before confirming the final payload through decrypted configuration structures consistent with Remcos.
Detection Appendix: PHALT#BLYX
Key Host Artifacts (File/Path):
-
- %ProgramData%\v.proj (malicious MSBuild project)
- %ProgramData%\staxs.exe (payload staging)
- C:\Windows\Temp\tybd7.exe (copied payload)
- %Startup%\DeleteApp.url, %Startup%\update.lnk (persistence)
High-Signal Behavioral Detections:
- Trusted proxy execution via MSBuild: msbuild.exe launched with a .proj argument (v.proj)
- Defender tampering / exclusions: Add-MpPreference -ExclusionPath C:\ProgramData and extension exclusions for .exe, .ps1, .proj, .tmp
- Startup persistence via .url pointing to local file:// execution (DeleteApp.url → C:\Windows\Temp\tybd7.exe)
- Suspicious network activity by atypical process (e.g., aspnet_compiler.exe network connections after injection)
MITRE ATT&CK:
-
- T1059.001 (PowerShell), T1127.001 (MSBuild proxy execution), T1204.002 (User execution), T1562.001 (Impair defenses), T1055.012 (Process injection), T1547.001 (Startup persistence), T1095 (Non-app layer protocol / custom port)
Detection Appendix: SHADOW#REACTOR
Key Host Artifacts (Files):
- Script and staging files: win64.vbs plus text-based staging (qpwoe32/64.txt, teste32/64.txt, config.txt)
- Benign-looking payload names: Update32.exe, update.exe
- Example hashes listed for staging/payload components (incl. teste32/64.txt, config.txt, config_dec.bin, Update32.exe)
High-Signal Behavioral Detections:
-
- Parent-child chain to prioritize: wscript.exe → powershell.exe → msbuild.exe
- PowerShell obfuscation / in-memory decode: large inline commands performing normalization/decoding and immediate execution.
- MSBuild LOLBin usage in late-stage execution.
- Noise/log-pollution PowerShell with nonsensical arguments (signature evasion).
MITRE ATT&CK:
-
- T1204 – User Execution, T1059.005 – Visual Basic, T1059.001 – PowerShell, T1620 – Reflective Code Loading, T1047 – MSBuild Abuse / Signed Binary Proxy Execution, T1060 – Startup Folder / Shortcut, T1027 – Obfuscated/Encrypted Payloads, T1112 / T1116 – Execution Policy Bypass and LOLBAS Abuse, T1105 – Ingress Tool Transfer, T1219 – Remote Access Tools
Mitigations & Defensive Recommendations:
- Train users on “ClickFix” style scams: explicitly warn employees never to paste/run commands from “error pages” (Run dialog / PowerShell), and enable file-extension visibility to reduce masquerading risk.
- Strengthen phishing verification habits for urgent financial or reservation-themed lures (e.g., hospitality brands). Validate requests via official channels rather than embedded links.
- For SHADOW#REACTOR-like delivery, educate users on script-based threats and suspicious “update” prompts or unexpected downloaded artifacts.
- Restrict or closely monitor VBS/JS/PowerShell execution, especially from user-writable locations (%TEMP%, browser cache, Downloads).
- Enable enhanced PowerShell telemetry (ScriptBlock, Module logging, command-line auditing) to surface heavily obfuscated, multi-stage reconstruction activity.
- Specifically for PHALT#BLYX, enable PowerShell Script Block Logging (Event ID 4104) to capture initial dropper logic.
- Implement strict monitoring on MSBuild.exe and alert when it compiles/executes project files from non-standard directories (%ProgramData%) or initiates outbound connections.
- Ensure detections cover suspicious parent-child chains such as wscript.exe → powershell.exe → msbuild.exe, and reflective .NET loading patterns.
- Monitor Defender tampering signals (exclusions, real-time protection changes) as high-priority precursors to payload deployment.
- Monitor high-risk “legitimate” binaries for anomalous behavior, especially unexpected outbound network activity (aspnet_compiler.exe, RegSvcs.exe, RegAsm.exe) and non-standard ports (3535).
- PHALT#BLYX: creation of .proj / .exe in %ProgramData% and Internet Shortcut (.url) persistence in Startup.
- SHADOW#REACTOR: suspicious Startup shortcuts, scheduled tasks, and “benign-looking” executables written to %TEMP%, ProgramData, or user profile directories.
Tags: Threat actor / Attribution: Russian-linked threat actors (unattributed cluster) | Adversary location: Russia | Target sector: Hospitality (Booking.com-themed), Broad / opportunistic; general enterprise and SMB | Target location: Europe / European organizations | Malware / Payloads: DCRat | Target systems: Windows endpoints
Malware & Backdoor Threat Snapshot – Originally published in January 2026
January’s activity reinforced a consistent attacker playbook: abuse trust and scale. Instead of “breaking in” with exploits, multiple campaigns rode trusted distribution channels (software updates, popular download searches, signed/legit-looking components) to plant backdoors and trojans, while botnet operators continued to harvest internet-exposed services with weak/default credentials at scale. Across these incidents, defenders should assume: “working software” can still be compromised, and credential hygiene includng supply-chain integrity are now primary battlegrounds.
A rare but high-impact scenario unfolded when attackers distributed malware through an antivirus update channel, compromising trust at the highest level. The incident reportedly began as unauthorized access to a regional update server, delivering a malicious reload.exe (with a fake/invalid signature) that replaced a legitimate component and executed a multi-stage infection chain.
A related supply-chain style pattern emerged through the abuse of legitimate-appearing components and ecosystem trust. Activity was observed where a commonly deployed productivity-related environment loaded malicious elements that ultimately delivered a persistent browser-based capability focused on user data collection and traffic manipulation. Rather than behaving like a single-purpose dropper, the infection path followed a staged model download, install, execute, and update allowing the operator to adjust functionality over time.
Alongside these distribution abuses, attackers also relied on “real software as camouflage” to compromise endpoints without triggering immediate user suspicion. A campaign leveraged a lookalike download experience to distribute a trojanized installer that deployed legitimate remote access functionality while quietly staging a backdoor framework in parallel. The technical flow emphasized stealth through staged loaders and memory-resident execution, minimizing obvious on-disk artifacts and reducing reliance on a single detectable binary.
On the mass-scale side, botnet operations continued to industrialize credential attacks against common internet-facing services and administrative panels. This activity relied heavily on weak and default passwords and was structured for throughput, using centrally directed tasking and aggressive concurrency to probe broad address space efficiently. The persistence of these campaigns underscores that widely exposed services remain a high-probability entry point, and that credential hygiene failures can function as an always-on backdoor for opportunistic actors.
Finally, targeted intrusion activity remained active through spear-phishing delivery of trojan implants. A recurring pattern involved convincing lures paired with containerized delivery formats and shortcut-based execution, allowing the attacker to present a decoy document while silently launching the payload. The implant behavior reflected deliberate anti-analysis and operational security measures prior to command-and-control communication, followed by host discovery and quiet data collection and transfer.
Detection Appendix: Update-Channel Tampering (Supply-Chain Style)
Key Host Artifacts (File/Path):
- Modified executables in application install directories (unexpected hash/version drift).
- New/unknown executable introduced during “update” window in system/application folders.
- Script artifacts in temp/profile paths (.ps1, .bat, .cmd) created shortly after update.
- Scheduled task entries created during update window (new task name + new action path).
- Registry payload storage patterns (unusual large values or blobs in non-standard keys).
High-Signal Behavioral Detections:
- A software update/maintenance process spawns script engines (powershell, wscript, cscript, cmd) with encoded/obfuscated arguments.
- Update process writes a new executable then executes it from temp/user-writable path.
- Attempts to block or degrade update capability (service config changes, scheduled task disabling, update URL changes).
- Creation of persistence (scheduled tasks / services / Run keys) tightly correlated with update events.
- Repeated re-creation of persistence after deletion (self-healing behavior).
MITRE ATT&CK:
- T1195 (Supply Chain Compromise), T1059.001 (PowerShell) / T1059.003 (Windows Command Shell), T1543.003 (Windows Service) / T1053.005 (Scheduled Task), T1562.001 (Impair Defenses)
Detection Appendix: Signed-Component / Plugin Delivery & Traffic Manipulation
Key Host Artifacts (File/Path):
- New DLLs/EXEs in user profile subfolders used by “helper” apps (unexpected new folder trees).
- Browser extension/plugin installation directories updated outside enterprise policy paths.
- Local config/cache folders created for extensions with frequent refresh cadence.
- Autostart entries that re-launch “helper” components (Run keys / scheduled tasks).
High-Signal Behavioral Detections:
- Productivity/helper app drops DLL/EXE into user-writable folder then launches it.
- Browser extension installed/updated without standard enterprise deployment mechanism.
- Extension/helper modifies browser settings or traffic routing behaviors (proxy, search provider, homepage).
- Continuous rule/config pull followed by bursts of redirected web traffic.
- DLL sideloading-like behavior: legitimate host process loads a newly written DLL from an unusual path.
MITRE ATT&CK:
- T1547 (Boot/Logon Autostart Execution), T1204.002 (User Execution), T1112 (Modify Registry) (if browser settings/keys are altered), T1071.001 (Web Protocols) (for config/rule polling)
Detection Appendix: Trojanized Installer with Parallel Backdoor (Legitimate App Camouflage)
Key Host Artifacts (File/Path):
- Installer package from user download directories executing secondary payload from temp
- “Loader” executable dropped alongside legitimate installer
- New service/task/run entry created immediately after install
- Executable or DLL staged in user-writable directories but launched as part of “setup” flow
High-Signal Behavioral Detections:
- Installer launches legitimate app install AND separately spawns an unknown loader/executable
- Memory-resident execution patterns: loader creates a process and injects/loads modules without corresponding file writes
- The legitimate app runs normally while a second process establishes persistence + outbound traffic
- High-entropy or unusually large payload staged then executed shortly after install
- Network: first-time outbound destination contacted within minutes of install completion, initiated by non-browser process
MITRE ATT&CK:
- T1204.002 (User Execution), T1547 / T1053.005 (Persistence via Run keys or Scheduled Tasks), T1055 (Process Injection) (if injection is observed), T1071.001 (Web Protocols)
Detection Appendix: Credential-Bruteforce Botnet Targeting Internet Services
Key Host Artifacts (File/Path):
- On servers: authentication logs showing high-volume failures
- On endpoints that become infected (if applicable): new lightweight downloader/executor in temp paths
- New cron/task/service entries on compromised systems (platform-dependent)
- Changes to firewall rules or remote access configurations post-compromise
High-Signal Behavioral Detections:
- Multiple failed logins followed by a success from same source within a short window.
- Authentication attempts against multiple services on the same host (service-hopping).
- Post-auth: new administrative sessions from unusual geos/ASNs or off-hours.
- Post-auth: rapid creation of new users, new keys, enabling remote services, or dropping of remote tooling.
- Lateral movement: same credential succeeds across multiple hosts shortly after brute-force burst.
MITRE ATT&CK:
- T1110 (Brute Force), T1078 (Valid Accounts), T1021 (Remote Services), T1562 (Impair Defenses) (if hardening controls are changed)
Detection Appendix: Spear-Phishing via Container and Shortcut (Trojan Implant)
Key Host Artifacts (File/Path):
- Email attachment opened from downloads/mail cache.
- Container files in user downloads (disk image/archive types).
- Shortcut files (.lnk) used to launch hidden commands.
- Dropped payload in temp/profile folders, often with decoy document displayed.
High-Signal Behavioral Detections:
- User opens container → .lnk executes cmd/powershell/rundll32/regsvr32 or launches an executable from temp.
- Decoy document opens while background process runs (dual execution pattern).
- Anti-analysis behaviors preceding network activity (sleep/timing checks, debugger checks).
- Host discovery followed by archive creation, then outbound transfer by non-browser process.
- Persistence created shortly after initial execution (task/service/Run key).
MITRE ATT&CK:
- T1566 (Phishing), T1204.002 (User Execution), T1059 (Command and Scripting Interpreter), T1082/T1016 (Discovery), T1071.001 (Web Protocols), T1547 / T1053.005 (Persistence)
Mitigations & Defensive Recommendations:
- Use centralized, managed software deployment; restrict end-user installs where possible.
- Inventory all internet-facing services and admin panels; remove unnecessary exposure.
- Enforce strong password policies; disable defaults immediately.
- Require MFA for remote access and privileged accounts.
- Block or tightly control high-risk attachment/container types when not required.
- Add controls for shortcut-based execution from email/download locations.
- Limit PowerShell/script execution for standard users; use constrained language mode where applicable.
- Apply application control policies for common abuse targets (script engines and system utilities).
- Monitor and alert on new/modified scheduled tasks, services, Run keys, and Startup folder entries.
- Enforce managed browser extension policies; block unapproved extensions.
- Correlate “new process + first-seen domain + persistence” as a high-confidence signal.
- Use least-privilege access controls and strong logging on sensitive shares and systems.
Tags: Target Sector: General users and organizations (broad consumer/enterprise software base), Home users, small/medium businesses, IT administrators, Web servers, Database servers, Internet-facing admin panels, Government ministries, Diplomatic or administrative entities, Consumer and enterprise endpoints using productivity tools, Broad civilian user base | Target Location: Asia, Afghanistan, China, Global | Malware / Payload Type: Backdoor, Multi-stage loader, Script-based execution chain, Loader + in-memory payload, Keylogging / remote-control capability, Credential brute-forcer, Lightweight downloader, Credential brute-forcer, Lightweight downloader, Trojan/remote access implant, Traffic manipulation component, Browser plugin-based data collection tool | Target Systems: Windows-based endpoints, Linux and Windows servers, Web/database/cloud-hosted services, Windows endpoints used within government offices
Significant APT Campaigns – Originally published in January 2025
This month’s reporting highlights APT clusters prioritizing quiet initial access and long-term persistence. Many intrusions began with spearphishing or messaging lures delivering document-themed files, archives, or double-extension payloads staged in common writable paths like ProgramData, Temp, or user desktops.
Tooling trends show increased modularity and defense awareness, including obfuscated Rust implants, plugin-based Linux backdoors on edge devices, and hands-on-keyboard activity in Windows environments using open-source post-exploitation tools with frequent tool rotation to evade detection.
Operators also relied on resilient C2 over HTTP and MQTT with retry logic and failover. Defenders should focus on persistence mechanisms, in-memory injection, registry changes, edge-device file drops, and tunneling activity, especially when tied to suspicious staging paths and unusual outbound ports.
| UAT-8837 | UAT-8837 is assessed as a China-aligned APT based on shared TTP patterns with known Chinese threat groups. Active since at least 2025, the group primarily targets critical infrastructure organizations in North America, with a focus on obtaining and brokering initial access to high-value networks. Initial access is typically achieved through exploitation of vulnerable internet-facing systems or the use of compromised credentials, followed by hands-on-keyboard activity. The actor relies heavily on open-source tooling to harvest credentials, enumerate security controls, and map Active Directory, enabling multiple persistence mechanisms. Observed tooling includes Earthworm, SharpHound, DWAgent, Certipy, and native Windows utilities, with early-stage activity involving reconnaissance, RestrictedAdmin modification for RDP credential harvesting, interactive command execution, and payload staging in commonly abused directories. |
| UAT-7290 | UAT-7290 is a China-linked APT active since at least 2022, focused on espionage against critical infrastructure, especially telecommunications providers in South Asia, with recent activity expanding into Southeastern Europe. The group conducts thorough pre-intrusion reconnaissance and primarily targets public-facing edge devices, exploiting one-day vulnerabilities and using tailored SSH brute-force attacks, often leveraging publicly available proof-of-concept code. Post-compromise, UAT-7290 deploys a modular Linux malware framework, using RushDrop as a dropper, DriveSwitch as a loader, and SilentRaid as the main implant for persistence and C2. The actor also uses Bulbature to convert compromised systems into Operational Relay Box nodes to support broader operations. |
| UAC-0190 | Between October and December 2025, UAC-0190, attributed to Void Blizzard also known as Laundry Bear, conducted a targeted cyber-espionage and sabotage campaign against Ukrainian state and social organizations. The attackers used messaging platforms to lure victims to fake charity sites or sent password-protected archives containing malicious executables disguised as documents. When opened, the files deployed PLUGGYAPE, a Python-based backdoor that enabled persistent access, system reconnaissance, remote command execution, and data exfiltration, supporting sustained espionage and potential follow-on disruptive activity. |
| Muddy Water | A targeted spear-phishing campaign attributed to the Muddy Water APT group has impacted diplomatic, maritime, financial, telecom, and government sectors across the Middle East. The operation introduces a Rust-based implant known as RustyWater, reflecting a notable shift in the group’s tooling. The attack uses phishing emails impersonating trusted regional or government entities to deliver a malicious Word document with VBA macros that extract and execute a hidden Rust payload. Once active, the malware mimics legitimate software, establishes registry-based persistence, and communicates with attacker infrastructure over encrypted HTTP. It incorporates anti-debugging and anti-analysis checks, EDR and antivirus evasion logic, in-memory execution, and layered encryption to reduce detection. |
Detection Appendix: UAT-8837 Initial Access and Post-Compromise
Key Host Artifacts (File/Path):
- Staging directories:
- C:\Users<user>\Desktop\
- C:\Windows\Temp\
- C:\Windows\Public\Music
- Tool paths (examples):
- C:\Users<user>\Desktop\go.exe (token theft utility)
- C:\Users\Downloads\dwagent.exe and Temp runtime path for DWAgent
- C:\Windows\Temp\SharpHound.exe
- C:\Windows\Temp\Invoke-WMIExec.ps1
- C:\Windows\Temp\Certipy.exe
- C:\Windows\Temp\pol.txt (secedit export output)
- C:\Windows\Temp\lo.txt (associated with Rubeus usage)
High-Signal Behavioral Detections:
- Registry change disabling RestrictedAdmin for RDP credential exposure attempts (REG ADD … DisableRestrictedAd…).
- Earthworm tunneling executed from Temp/Public paths with masqueraded filenames (*.ico) and rssocks parameters.
- AD reconnaissance via SharpHound and Certipy, plus native setspn, dsquery, dsget usage.
- Security policy export via secedit /export to C:\Windows\Temp\pol.txt.
- Creation of backdoored domain user accounts or adding users to groups for persistence.
MITRE ATT&CK:
- T1190 – Exploit Public-Facing Application, T1078 – Valid Accounts, T1112 – Modify Registry, T1090 – Proxy, T1087.002 – Account Discovery: Domain Account, T1546.003 – Event Triggered Execution: Windows Management Instrumentation, T1136.002 – Create Account: Domain Account, T1518 – Software Discovery
Detection Appendix: UAT-7290 Telecom Edge Intrusions
Key Host Artifacts (File/Path):
- “.pkgdb” folder in current working directory (drop location)
- Dropped binaries: daytime; chargen; busybox (used as utility)
- /etc/passwd accessed by file-management plugin
- Bulbature config: /tmp/<malware_binary_name>.cfg
High-Signal Behavioral Detections:
- Edge-device dropper creates/uses hidden “.pkgdb” folder and writes multiple staged binaries.
- Self-delete if VM/sandbox checks fail.
- Remote shell via executing “sh” through busybox or /bin/sh.
- Port forwarding setup between local and remote ports (including multi-port forwarding).
- Archiving via “tar -cvf” executed via busybox; removal via “rm” via busybox.
- ORB behavior: binding listener, reverse shell, /tmp .cfg C2 storage, and C2 switching.
MITRE ATT&CK:
- T1190 – Exploit Public-Facing Application, T1110 – Brute Force, T1505.003 – Server Software Component: Web Shell, T1059.004 – Command and Scripting Interpreter: Unix Shell, T1090 – Proxy, T1572 – Protocol Tunneling
Detection Appendix: PLUGGYAPE Lures via Fake Charity
Key Host Artifacts (File/Path):
- %TMP%\main.py
- %TMP%\odfadgjklfsfddapy
- %TMP%\is.py
- HKCU\Software\Microsoft\Windows\CurrentVersion\Run\’RealtekDevice’
- PDB path observed: C:\Users\User\source\repos\MolineRebuild\x64\Release\MolineRebuild.pdb
- Common delivery naming patterns:
- Inventory_list.docx.pif; Inventory_list_new.docx.pif; blank_zvernenya*.pif
High-Signal Behavioral Detections:
- Instant messenger lures leading to look-alike charity sites and password-protected archives.
- Execution of double-extension payloads (.docx.pif), including PyInstaller-packed executables.
- Loader behavior that downloads a Python interpreter and follow-on script content from paste sites (earlier variant).
- MQTT-based C2 introduced in later variants; JSON data exchange and remote code execution.
- Persistence via HKCU Run key value ‘RealtekDevice’.
MITRE ATT&CK:
- T1566.002 – Phishing: Spearphishing Link, T1204.002 – User Execution: Malicious File, T1059.006 – Command and Scripting Interpreter: Python, T1071 – Application Layer Protocol, T1547.001 – Registry Run Keys/Startup Folder, T1497 – Virtualization/Sandbox Evasion
Detection Appendix: Rust Implant via Spearphishing
Key Host Artifacts (File/Path):
- C:\ProgramData\CertificationKit.ini
- Cybersecurity.doc (malicious Word attachment)
- Masqueraded payload name: reddit.exe (presented identity)
High-Signal Behavioral Detections:
- Word document VBA macro decodes embedded hex payload and writes to ProgramData.
- Macro constructs WScript.Shell via Chr()/ASCII reconstruction, then launches cmd.exe to execute dropped payload.
- Registry persistence via Run key referencing ProgramData payload.
- HTTP beaconing with retry logic and randomized callback intervals (jitter).
- Process injection pattern: VirtualAllocEx + WriteProcessMemory targeting explorer.exe.
- Defense evasion: broad AV/EDR discovery by scanning known agent files/services/paths.
MITRE ATT&CK:
- T1566.001 – Phishing: Spearphishing Attachment, T1204.002 – User Execution: Malicious File, T1059.005 – Command and Scripting Interpreter: Visual Basic, T1106 – Native API, T1047 – Windows Management Instrumentation, T1620 – Reflective Code Loading, T1547.001 – Registry Run Keys/Startup Folder, T1055 – Process Injection
Mitigations & Defensive Recommendations:
- Alert on registry changes impacting RDP authentication/credential handling, specifically modifications referencing “DisableRestrictedAd…”.
- Restrict write/execute in common staging directories and alert on execution from C:\Windows\Temp and C:\Windows\Public\Music.
- Monitor and gate execution of reg.exe, net.exe, secedit.exe, dsquery/dsget, and setspn when launched in suspicious admin sessions or from atypical parent processes.
- Block execution of .pif and other legacy executable handlers where feasible; alert on double-extension patterns such as .docx.pif.
- Monitor for Python interpreter downloads/execution from user-writable paths and for temp-directory Python script writes (main.py, is.py).
- Quarantine Office attachments that contain macros or embed unusually large form-control strings/hex blobs.
- Enable and forward registry auditing for Run key modifications; alert on Run values pointing to ProgramData and atypical extensions (.ini).
- Enforce macro blocking from untrusted origins; log and alert on WinWord launching script interpreters or cmd.exe.
- Alert on suspicious use of wscript.exe/cmd.exe initiated from Office processes.
Tags: Malware: RushDrop, DriveSwitch, SilentRaid, RedLeaves or Shadowpad , PLUGGYAPE, RustyWater | Threat Actor: UAT-8837, UAT-7290, Void Blizzard and Muddy Water | Target Sector: Critical infrastructure, Telecommunications, Diplomatic, Maritime, Financial, and Government | Target Location: North America, South Asia, Ukrainian, Middle East| Adversary Origin: China, IRAN, Russia
Edge Ghosts Sliver C2 on FortiWeb – Originally published in January 2025
Analysis for this month highlights a recurring visibility gap: adversaries are increasingly using edge appliances (including web application firewalls) as both initial access footholds and long-lived execution platforms, where traditional endpoint AV/EDR telemetry is often absent. In the observed activity, attackers gained access by exploiting public-facing vulnerabilities and then deployed a Sliver implant directly onto impacted devices. Victim-side execution was Linux-based and frequently associated with outdated FortiWeb versions, indicating opportunistic scanning for unpatched or end-of-life appliance builds.
It describes an operation where an actor deployed Sliver C2 implants onto compromised hosts, with the majority of observed beaconing systems identified as outdated FortiWeb appliances. Initial access is assessed to be exploitation of public-facing vulnerabilities; specifically, exploitation of React2Shell (CVE-2025-55182) is cited, and exploitation of FortiWeb appliances is observed, though the exact FortiWeb vulnerability used is unknown.
After compromise, the Sliver implant was dropped to Linux paths intended to blend in with system binaries. On FortiWeb systems, the binary was deployed to /bin/.root/system-updater, while one non-FortiWeb Linux host was noted with /app/web/system-updater. The actor generated HTTP beacons and used decoy web content tied to their C2 domains to appear legitimate.
Persistence was established using systemd service configuration (explicitly referenced in the report) and additionally by modifying supervisor.conf to ensure continued execution. This indicates a focus on maintaining durable access on Linux-based appliances where traditional endpoint controls are limited.
For lateral utility and remote exposure of internal services, the actor leveraged FRP by downloading a configuration (e.g., frpc.toml) from an external server and using an FRP server that showed multiple active victims. Separately, the actor used the open-source microsocks proxy delivered as a renamed binary cups-lpd, exposing SOCKS on port 515 to masquerade as a legitimate printing daemon port; a systemd service was also observed for this proxy component.
Detection Appendix:
Key Host Artifacts (File/Path):
- /bin/.root/system-updater (Sliver binary on FortiWeb)
- /app/web/system-updater (Sliver binary on one non-FortiWeb Linux host)
- updater.service (systemd service used for persistence; ExecStart points to /bin/.root/system-updater)
- supervisor.conf modified to persist execution (runs /bin/.root/system-updater)
- /bin/.root/cups-lpd (renamed microsocks binary persisted via systemd; exposes SOCKS)
- frpc.toml (FRP client configuration downloaded to victims)
High-Signal Behavioral Detections:
- Linux appliance unexpectedly running hidden binary from dot-prefixed directory:
- Execution of /bin/.root/system-updater
- New or modified systemd service enabling persistence:
- updater.service created/enabled with ExecStart=/bin/.root/system-updater
- systemd service launching /bin/.root/cups-lpd
- Supervisord persistence:
- supervisor.conf altered to autostart/autorestart /bin/.root/system-updater
- Unexpected SOCKS exposure on printing port:
- Listener on 515/TCP associated with cups-lpd binary (masquerade of CUPS LPD port)
- Post-compromise tunneling/proxy enablement:
- Download of FRP configuration (frpc.toml) from external server and subsequent proxy activity.
MITRE ATT&CK:
- T1543.002 – Create or Modify System Process: Systemd Service, T1543 – Create or Modify System Process, T1190 – Exploit Public-Facing Application, T1572 – Protocol Tunneling, T1090 – Proxy
Mitigations & Defensive Recommendations:
- Reduce exposure of appliance management/admin interfaces to the public internet; restrict to VPN/allowlisted IPs where possible.
- Ingest and alert on systemd unit creation/changes on Linux appliances (new *.service files and ExecStart pointing to nonstandard locations like /bin/.root/).
- Monitor for modifications to supervisor.conf (or equivalent process supervisors) that introduce new autostart programs pointing to hidden paths.
- Add detections for binaries executing from dot-prefixed or otherwise hidden directories on appliances (/bin/.root/).
- Hunt for unexpected listening services on 515/TCP from appliance IPs, especially if not operating a printing service.
- If compromise suspected, triage appliances for:
- Presence of /bin/.root/system-updater or /bin/.root/cups-lpd
- updater.service and other unfamiliar systemd units
- Evidence of supervisor.conf tampering
- Network egress to the listed C2 infrastructure
- Validate appliance patch posture and urgently remediate outdated FortiWeb versions identified as impacted.
Tags: Target Sectors/Regions: Government, Financial; Bangladesh, Pakistan, US, India, Singapore | Malware/Tools: Sliver C2, FRP, microsocks (cups-lpd) | Target system/platform: FortiWeb (Linux/amd64) edge/WAF appliances
Key Ransomware Groups and Campaign Trends – Originally published in January 2025
Recent reporting across multiple ransomware families highlights a continued shift away from noisy, smash-and-grab encryption events toward long-dwell, operator-driven intrusion campaigns that closely resemble advanced persistent threats. Modern ransomware actors increasingly blend trusted tooling, living-off-the-land techniques, and bespoke loaders to evade detection, maintain persistence, and maximize extortion leverage.
LockBit 5.0 remains emblematic of this maturity, continuing to operate as a highly efficient Ransomware-as-a-Service ecosystem with refined encryption logic, service termination routines, and selective file targeting. Its use of ChaCha20-Poly1305 with X25519 key exchange, dynamic extension generation, and aggressive backup suppression underscores how even well-established RaaS groups continue to optimize for speed and resilience during the final impact phase.
Parallel to this, newer and lower-profile operations such as DeadLock demonstrate experimentation with non-traditional infrastructure, notably abusing Polygon smart contracts to dynamically retrieve proxy and communication endpoints. By embedding command routing logic into decentralized blockchain transactions, DeadLock reduces reliance on static C2 infrastructure, complicating takedowns and detection while enabling rapid proxy rotation during extortion communications .
Medusa ransomware illustrates how Remote Monitoring and Management (RMM) abuse has become a dominant access and persistence strategy. Rather than deploying custom backdoors, Medusa operators weaponize legitimate tools such as SimpleHelp, Atera, ScreenConnect, and AnyDesk to establish long-term control, perform lateral movement, exfiltrate data at scale, and execute ransomware binaries directly on victim hosts. This approach allows attackers to masquerade as legitimate administrators while bypassing traditional malware-centric detections.
CrazyHunter further reinforces the trend toward domain-centric ransomware operations, abusing Active Directory misconfigurations and Group Policy Objects to rapidly propagate payloads across enterprise environments. Its heavy reliance on BYOVD techniques, Donut shellcode loaders, and staged AV-killer binaries reflects a deliberate emphasis on disabling defenses before encryption, ensuring high impact and minimal resistance during execution.
Interlock ransomware campaigns demonstrate similar hands-on-keyboard tradecraft, chaining initial access via loader malware into prolonged RAT-based persistence, credential harvesting, and large-scale data exfiltration using legitimate utilities such as AZCopy. The group’s use of custom process-killer drivers, ScreenConnect abuse, and cross-platform ransomware payloads highlights the convergence of ransomware and full-spectrum intrusion operations.
Finally, Sicarii ransomware stands out less for technical sophistication and more for performative and deceptive signaling, blending functional ransomware capabilities with explicit ideological branding and geo-fencing logic. While the malware itself supports credential harvesting, LSASS dumping, Fortinet exploitation, and destructive recovery-blocking behavior, inconsistencies in language use, tooling maturity, and operational discipline suggest an emerging or experimental actor rather than a fully established RaaS ecosystem .
Across all these cases, a consistent pattern emerges: ransomware is no longer a single event but the final stage of a broader intrusion lifecycle, where stealth, persistence, and operational flexibility are prioritized well before encryption begins.
Detection Appendix: LockBit 5.0 Operation Analysis
Key Host Artifacts (File/Path):
- Temp directories targeted for deletion:
- C:\Users\All Users\AppData\Local\Temp
- C:\Users\Default\AppData\Local\Temp
- C:\Users\Public\AppData\Local\Temp
- C:\Users\{Username}\AppData\Local\Temp
- Ransom note filename: ReadMeForDecrypt.txt
- Exclusion examples (directories): Windows, $Recycle.Bin, System Volume Information, Microsoft\Windows, and others listed in source
- Exclusion examples (files): iconcache.db, thumbs.db
High-Signal Behavioral Detections:
- Temp directory cleanup/deletion prior to encryption to increase speed.
- Termination/disablement of VSS-related and other backup/security services.
- Packing/obfuscation indicative of anti-analysis.
- Generation of many per-run extensions (100 new 8-byte extensions) rather than a fixed extension.
- File encryption using ChaCha20-Poly1305 with X25519+BLAKE2b key exchange.
MITRE ATT&CK:
- T1071 – Application Layer Protocol (exfiltration noted, tooling referenced), T1027 – Obfuscated/Compressed Files and Information, T1070.004 – File Deletion (Temp cleanup behavior), T1490 – Inhibit System Recovery (VSS/service tampering), T1486 – Data Encrypted for Impact
Detection Appendix: DeadLock Smart-Contract Proxies
Key Host Artifacts (File/Path):
- Encrypted file extension: .dlock
- Dropped HTML file acting as a communications wrapper for a secure messenger workflow (filename not specified in source)
- PowerShell script that:
- relaunches with admin rights
- stops/disables non-whitelisted services
- deletes Volume Shadow Copies
- self-deletes
High-Signal Behavioral Detections:
- PowerShell run-as elevation attempts followed by bulk service stop/disable actions.
- Volume Shadow Copy deletion behavior.
- “Impact service stop” behavior (stopping non-native services; exception behavior noted for a remote access tool).
- Unusual proxy POST patterns to /prrq.php with method parameters:
- ping, get_snodes, get_swarms, poll, store
- Host encryption bursts leading to .dlock file renames and wallpaper/icon changes.
MITRE ATT&CK:
- T1059.001 – PowerShell, T1489 – Service Stop, T1490 – Inhibit System Recovery, T1486 – Data Encrypted for Impact, T1071.001 – Web Protocols (proxy HTTP POST comms), T1105 – Ingress Tool Transfer (inferred via dropped HTML wrapper)
Detection Appendix: Medusa RMM Abuse Patterns
Key Host Artifacts (File/Path):
- c:\windows\system32\gaze.exe
- Ransom note: !!!READ_ME_MEDUSA!!!.txt
- Observed reference to admin share execution context: \\<device_hostname>\ADMIN$ (context shown alongside ransomware binary mention).
High-Signal Behavioral Detections:
- Unexpected outbound connections to RMM infrastructure (especially if RMM is not deployed enterprise-wide).
- RMM agent reconfiguration / “phone-home” redirection to non-enterprise servers.
- Large outbound uploads to suspicious external hosts (notably exfil endpoints listed above) over 80/443/445.
- Ransomware host execution indicators:
- creation of ransom note file and rapid file modification bursts
- execution of gaze.exe from system paths
- Data staging/exfil tooling behaviors mentioned: use of rclone and robocopy for exfiltration/staging.
MITRE ATT&CK:
- T1219 – Remote Access Software, T1071 – Application Layer Protocol, T1105 – Ingress Tool Transfer, T1020 – Automated Exfiltration, T1486 – Data Encrypted for Impact, T1110 – Brute Force, T1110.004 – Credential Stuffing, T1021.001 – Remote Desktop Protocol, T1021.003 – Distributed Component Object Model, T1083 – File and Directory Discovery
Detection Appendix: CrazyHunter Stealth Tactics
Key Host Artifacts (File/Path):
- Orchestrator script: ru.bat
- AV killers: go.exe, go2.exe
- Primary encryptor: go3.exe
- Donut loader: bb.exe
- Donut shellcode file: crazyhunter.sys (encrypted shellcode)
- Backup encryptor: crazyhunter.exe
- Vulnerable driver used for BYOVD: zam64.sys
- Encrypted file extension: .hunter (and noted .Hunter)
- Wallpaper artifact: Wallpaper.png saved in \temp
- Exfil/control tool: file.exe (dual-mode: file server or file monitor/delete)
High-Signal Behavioral Detections:
- AD account compromise via weak domain passwords (valid domain account abuse)
- GPO-based payload deployment (domain policy abuse)
- BYOVD chain:
- Driver register and process termination via IOCTLs to zam64.sys
- Security process kill list behavior (enumerate processes, match against hardcoded AV list, terminate)
- Fileless/in-memory execution:
- Donut loader bb.exe executing crazyhunter.sys shellcode
- Ransomware execution chain via batch + timed delays (timeout.exe)
- Impact:
- Encryption across drives A–Z enumeration, recursive encryption, then wallpaper set
- .hunter extension output
MITRE ATT&CK:
- T1078.002 – Valid Accounts: Domain Accounts, T1204.002 – User Execution: Malicious File, T1484.001 – Domain Policy Modification, T1068 – Exploitation for Privilege Escalation, T1553.002 – Code Signing, T1036 – Masquerading, T1003 – OS Credential Dumping, T1018 – Remote System Discovery, T1021 – Remote Services, T1486 – Data Encrypted for Impact, T1485 – Data Destruction
Detection Appendix: Interlock Intrusion: Long Dwell to Encryption
Key Host Artifacts (File/Path):
- download.zip (contains Node.js runtime node.exe)
- Node.js runtime folder:
- C:\Users\<user>\AppData\Roaming\node-v22.11.0-winx64\
- …\j1wp4vw8.log (JavaScript implant)
- …\05x3aay1.log
- …\node.log (later-stage implant)
- Additional implant locations:
- C:\Users\<user>\AppData\Roaming\3o55fai8\k4myle3i.dll
- C:\Users\<user>\AppData\Roaming\dji8zg3d\aqwsxvvz.log
- C:\Users\<user>\AppData\Roaming\ro5ryxiu\g86oofvm.dll
- C:\Users\<user>\AppData\Roaming\ywgomm2t\9gesu23g.log (archive w/ Java env + jucheck.jar)
- Scheduled task names used for persistence:
- \Microsoft\Windows\Defrag\ScheduledDefrags
- \Microsoft\Windows\Chkdsk\TempDefrag
- \TimeSyncDrive, \TimeSyncroDriver, \TimeSync, \TimeSyncro
- PowerShell scripts:
- 1.ps1 placed on domain controller in share Microsoft
- Later version hosted in share out on domain controller
- Remote tool installer:
- support.msi (remote access tool installation)
- Exfiltration utility:
- win64.exe (copy of AZCopy)
- Ransomware payloads:
- jar.jar (JavaScript ransomware on Windows)
- update.jar (used in large-scale deployment)
- script (ELF ransomware used on Nutanix)
- BYOVD/process killer components:
- polers.dll (process killer launcher via rundll32.exe)
- UpdateCheckerX64.sys dropped to current directory (example E:\UpdateCheckerX64.sys)
- Kernel driver service name pattern: UpdateCheckerX64_{random-numbers}
- Custom infostealer:
- move.dll executed via rundll32.exe
- Temp output file example: random name such as zGi0UUlYs0 in %TEMP%
- CSV output format: <IP>.<username>.csv
- Encryption extensions:
- Windows: .gif
- Nutanix: .!nt3rlock
High-Signal Behavioral Detections:
- PowerShell download cradle with irm/iex fetching from external IP and time-based path.
- Node.js (node.exe) executing obfuscated JavaScript payloads from user Roaming directories.
- Persistence via autorun entry named ChromeUpdater pointing to Node.js/JS payload chain.
- Scheduled task creation/modification using masqueraded task paths (Defrag/Chkdsk/TimeSync variants) pointing to non-standard binaries in AppData.
- Interlock RAT host profiling via systeminfo executed through PowerShell and sent in plaintext in the initial C2 packet (magic value 0xDF691155).
- Remote access tool installation via MSI followed by interactive browsing of file servers and chained RDP sessions.
- Firewall rule modification for RDP using netsh.exe from interactive PowerShell.
- Bulk data exfiltration using AZCopy (win64.exe) from a file server (~250GB).
- BYOVD / process-killer activity:
- rundll32.exe .\polers.dll start Forti*
- Drop/install kernel driver UpdateCheckerX64.sys
- Driver service name UpdateCheckerX64_{random-numbers}
- Device link \\.\HtAntiCheatDriver and IOCTL usage (not always visible in standard logs)
- Large-scale ransomware deployment chain:
- W_0.bat launching PsExec.exe to run powershell.exe -ExecutionPolicy Bypass -file \\<DC>\out\1.ps1
- JavaScript ransomware executed via dropped javaw.exe in masqueraded AppData paths (Welcome/FortiClient/VMware).
- Post-impact file extensions: .gif (Windows) and .!nt3rlock (Nutanix).
MITRE ATT&CK:
- T1204.004 – User Execution: Malicious Copy and Paste, T1059.001 – Command and Scripting Interpreter: PowerShell, T1059.007 – Command and Scripting Interpreter: JavaScript, T1078 – Valid Accounts, T1053.005 – Scheduled Task/Job: Scheduled Task, T1543.003 – Create or Modify System Process: Windows Service, T1070 – Indicator Removal, T1620 – Reflective Code Loading, T1555 – Credentials from Password Stores, T1083 – File and Directory Discovery, T1021.001 – Remote Services: Remote Desktop Protocol, T1021.002 – Remote Services: SMB/Windows Admin Shares, T1074 – Data Staged, T1005 – Data from Local System, T1048 – Exfiltration Over Alternative Protocol, T1041 – Exfiltration Over C2 Channel, T1486 – Data Encrypted for Impact
Detection Appendix: Sicarii RaaS: Truth vs Myth
Key Host Artifacts (File/Path):
- Self-copy into Temp with randomized name: svchost_{random}.exe
- Data staging archive: collected_data.zip
- Destructive script: destruct.bat (registered to execute at startup)
- Likely user-dir targeting: Documents\Downloads\Desktop\Videos\Pictures\Music (collection/encryption scope)
- Persistence artifacts:
- Service name: WinDefender
- New local user: SysAdmin / password Password123!
High-Signal Behavioral Detections:
- Anti-VM/sandbox gating followed by decoy MessageBox error (“DirectX failed…”)
- Mutex-based single instance execution
- Repeated internet check loop to generate_204 (high frequency)
- SafeBoot option tampering / disabling recovery paths
- Credential access attempts:
- Registry hive collection, browser/app data harvesting
- LSASS dumping attempt
- Recon and lateral movement prep:
- ARP mapping and probing discovered hosts
- RDP exposure scanning
- Fortinet exploit attempt (CVE in source)
- Persistence bursts:
- Run key + service creation + new user creation
- Defense evasion:
- Enumerate/terminate AV/VPN processes
- Impact + sabotage:
- Encrypt in place, append .sicarii, delete original file
- Startup-registered destruct.bat invoking cipher/diskpart, boot corruption, forced shutdown
MITRE ATT&CK:
- T1497 – Virtualization/Sandbox Evasion, T1071 – Application Layer Protocol (exfil via public service), T1003 – OS Credential Dumping (LSASS dump attempt), T1082 – System Information Discovery, T1018 – Remote System Discovery (ARP mapping/probing), T1547.001 – Registry Run Keys/Startup Folder, T1543.003 – Create or Modify System Process (Windows Service), T1486 – Data Encrypted for Impact, T1485 – Data Destruction (boot/disk sabotage behavior)
Mitigations & Defensive Recommendations:
- Restrict and alert on service stop/control operations targeting backup and VSS components; treat these as “pre-impact” events requiring immediate response.
- Restrict PowerShell to constrained language mode where feasible; enforce Script Block Logging and alert on encoded/evasion-like invocation parameters.
- Restrict and monitor interactive admin share usage (ADMIN$) and remote service execution pathways; alert on unexpected execution from admin shares.
- Monitor and baseline robocopy.exe and rclone execution from non-admin user contexts; alert on high-volume copy/upload patterns.
- Alert on creation of !!!READ_ME_MEDUSA!!!.txt and mass file rename with .MEDUSA extension.
- Block or alert on vulnerable driver loading patterns and unsigned/unexpected driver installs; specifically monitor presence/load of zam64.sys.
- Block or heavily monitor outbound web requests initiated by powershell.exe / powershell_ise.exe, especially to raw IPs and uncommon ports (8080).
- Enforce least privilege and remove/disable default or rarely used local/domain administrator accounts; alert on “default Administrator” logons and RDP use.
- Block workstation-to-workstation SMB and RDP at the Windows firewall; allow only where explicitly required (servers/jump hosts).
- Alert on firewall rule changes enabling RDP, especially initiated via netsh.exe from interactive shells.
- Alert on PowerShell execution with -ExecutionPolicy Bypass and remote UNC script execution (\\<DC>\out\1.ps1).
- Monitor for creation/modification of obfuscated PowerShell scripts on domain controllers and in shared folders named like common vendors or system folders (Microsoft, out).
- Treat rundll32.exe executing DLLs from user-writable or removable paths (E:\, %TEMP%, %AppData%) as high risk; auto-contain when paired with wildcard arguments like Forti*.
- Block or closely monitor egress to public file-sharing services used for exfiltration (file.io) and alert on bulk uploads.
- Enforce controls that alert on or prevent SafeBoot configuration tampering and boot configuration modification.
- Require strong local account governance: alert on creation of new local admins (SysAdmin) and enforce randomized passwords.
Tags: Threat Actor: LockBit RaaS, Medusa, CrazyHunter, Sicarii, DeadLock, Interlock | Threat Actor Type: Ransomware-as-a-Service (RaaS), Affiliate-driven operators, Initial Access Broker (IAB) customers, Hands-on-keyboard ransomware operators | Adversary Location: Suspected Russia / Eastern Europe–based, Suspected Taiwan-based, Claimed Israeli/Jewish affiliation with likely Russian- or English-speaking operators, Unknown | Associated Ransomware: LockBit 5.0, LockBit 3.x, Medusa, CrazyHunter, Sicarii, DeadLock, Interlock | Target Sectors: Cross-sector, Healthcare, Financial Services, Manufacturing, Automotive, Education, Public Sector, Technology | Target Locations: Global, North America, Europe, Asia-Pacific, Taiwan, Middle East | Target Systems: Windows endpoints, Windows servers, Active Directory environments, VMware ESXi servers, Nutanix infrastructure, RMM management servers | Target Platforms: Windows, Linux (ESXi) | Malware: LockBit 5.0 encryptor, StealBit exfiltration tool, Medusa ransomware, CrazyHunter ransomware, Sicarii ransomware, DeadLock ransomware, Interlock ransomware, MintLoader, NodeSnakeRAT, Interlock RAT, Donut loader, SharpGPOAbuse, SimpleHelp RMM, Atera, ScreenConnect, AnyDesk, Rclone, BYOVD drivers
For a full list of the search queries used on Autonomous Threat Sweeper for the threats detailed above, refer to ours Threat Labs home page. The page also references a list of relevant policies used by threat actors.
We would like to hear from you. Please reach out to us at [email protected].
Note: The TTPs when used in silo are prone to false positives and noise and should ideally be combined with other indicators mentioned.
Contributors: Nikhil Kumar Chadha and Tanmay Kumar