- Why Securonix?
- Products
-
- Overview
- Agentic AI
-
- Securonix Cloud Advantage
-
- Solutions
-
- Monitoring the Cloud
- Cloud Security Monitoring
- Gain visibility to detect and respond to cloud threats.
- Amazon Web Services
- Achieve faster response to threats across AWS.
- Google Cloud Platform
- Improve detection and response across GCP.
- Microsoft Azure
- Expand security monitoring across Azure services.
- Microsoft 365
- Benefit from detection and response on Office 365.
-
- Featured Use Case
- Insider Threat
- Monitor and mitigate malicious and negligent users.
- EMR Monitoring
- Increase patient data privacy and prevent data snooping.
- MITRE ATT&CK
- Align alerts and analytics to the MITRE ATT&CK framework.
- MSSPs
- Scale multi-tenant security with predictable economics.
-
- Resources
- Partners
- Company
- Blog
SIEM
By Sarah Radin, Product Marketing Manager
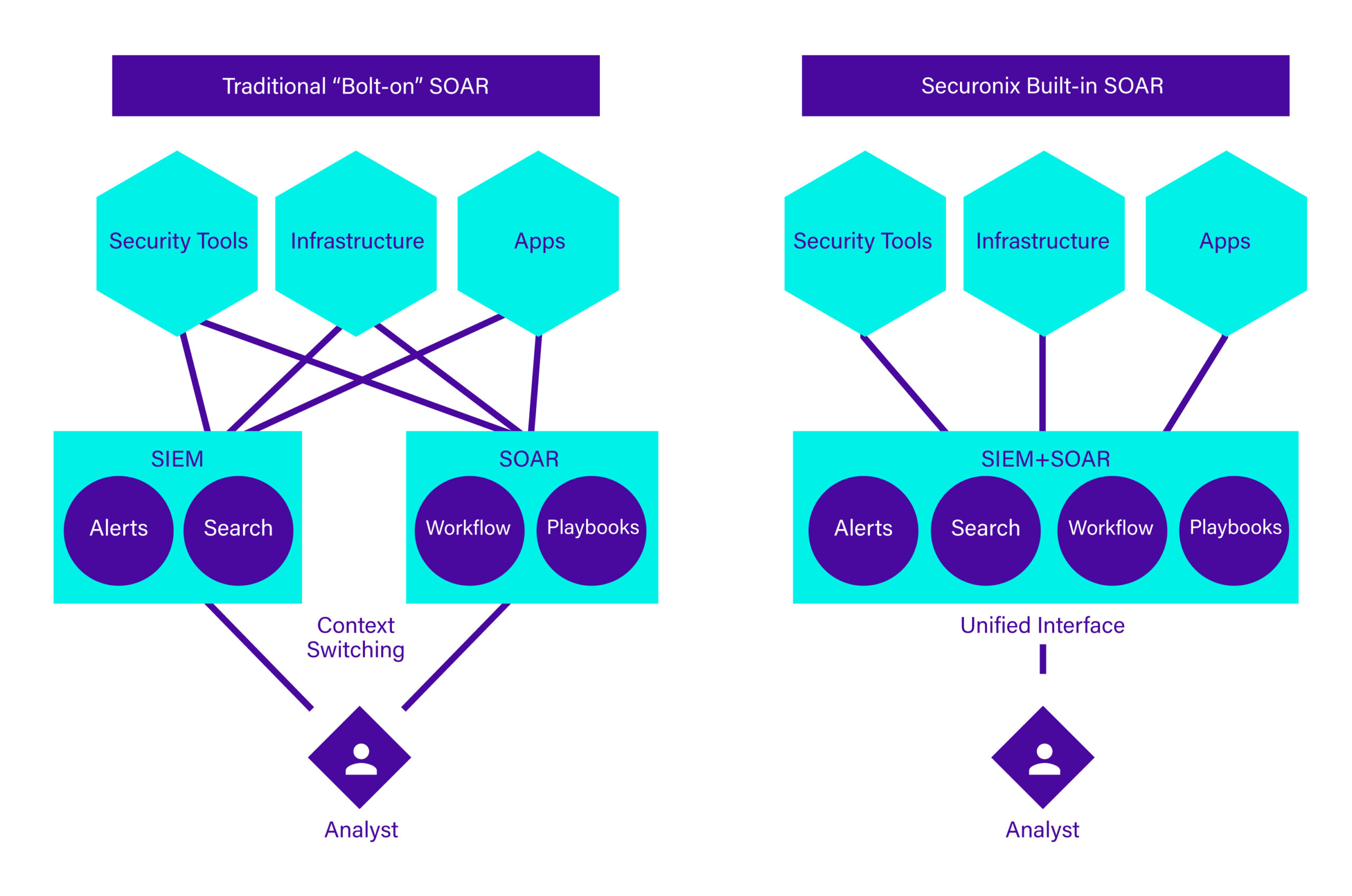
Cybercriminals are getting faster and smarter, while IT and security operations grow more cumbersome. On top of a dramatic increase in data usage and the growing complexity of IT environments, cybercriminals are becoming more aggressive with their tactics. Next-Generation SIEM solutions are proficient at recognizing complex threats, but what do you do from there? Many organizations are leaning toward SOARs to automate activity and orchestrate actions across the security team to resolve these threats. However, disparate SIEM and SOAR solutions are limited in their effectiveness. Organizations need scalable automation and orchestration capabilities to empower analysts to investigate and respond faster.
When machine speed attacks like ransomware can enact final attack stages in seconds, the stakes to respond are high. Standalone SOAR solutions struggle to improve mean time to respond (MTTR) due to a lack of necessary event data related to alerts. This requires analysts to toggle between multiple interfaces and perform repetitive tasks to investigate and respond to the threats. On the other hand, tightly integrated SOAR capabilities within the core security analytics platform simplifies the user experience and streamlines the end-to-end incident response cycle.
We’ve created an e-book that breaks down why it is essential for security teams to have SOAR capabilities that act as a seamless extension of your SIEM. Organizations that implement an integrated SIEM and SOAR solution gain the ability to:
- Streamline investigation and response
- Respond to threats at scale
- Maximize security operations investments
Let’s explore why these benefits are so crucial.
Benefit #1. Streamline Investigation and Response
When your SOAR capabilities are a seamless extension of your SIEM, analysts can significantly drive down their MTTR and free up their resources to focus on mission-critical tasks.
SOC Ergonomics
Having good SOC ergonomics and taking an analyst-centric approach to security is essential. Natively integrated SIEM and SOAR solutions that are designed to simplify an analyst’s experience and well-being will always yield better results than bolted-on solutions. Giving analysts the ability to collaborate, investigate, and respond without context switching not only allows you to drive down your MTTR, but also empowers your team to focus on high-risk threats versus mundane tasks.
Automated Response
When an alert comes through an analyst is tasked with manually searching for additional context across threat intelligence, identity repositories, and asset management sources. SOAR automatically gathers key evidence and artifacts from multiple tools and sources so that analysts can investigate alerts within a single console. This automation happens at machine speed, allowing your organization to respond to threats more efficiently from the moment they are detected.
Benefit #2. Respond to Threats at Scale
SIEM and SOAR solutions are only as good as the data they collect, making architecture massively important for fast detection and response.
Seamless Integrations
Tightly integrated cloud solutions help you avoid duplicative data resources. When the SIEM and SOAR aren’t properly connected it may increase data requirements which in turn can increase costs. A well-architectured, cloud-native SOAR embedded into the SIEM is the most effective way for modern enterprises to meet both security and data demands.
SaaS Deployment
Along with offering high configurability, cloud-based SIEM and SOAR solutions deliver nearly unlimited scale and faster velocity than on-premises or bolted-on solutions. Solutions that are developed for, and run in, the cloud allow organizations to provision and deprovision resources as needed. Not to mention the time your team saves when they don’t have to focus on managing infrastructure.
Want to learn about how SOAR helps maximize your security operations investments? Download the e-book.